GSM network and its privacy
180 likes | 378 Views
GSM network and its privacy. Thomas Stockinger. Overview. Why privacy and security? GSM network‘s fundamentals Basic communication Authentication Key generation Encryption: The A5 algorithm Attacks Conclusion. Why?. From technical point of view

GSM network and its privacy
E N D
Presentation Transcript
GSM network and its privacy Thomas Stockinger
Overview • Why privacy and security? • GSM network‘s fundamentals • Basic communication • Authentication • Key generation • Encryption: The A5 algorithm • Attacks • Conclusion
Why? • From technical point of view • Electromagnetic waves as communication media • From customer’s point of view • Privacy • Cell phone cloning • From operator’s point of view • Billing fraud • Loss of customer faith • m-commerce applications
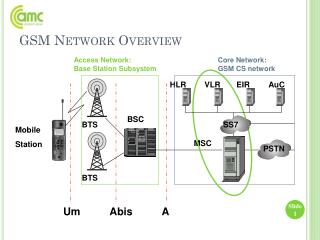
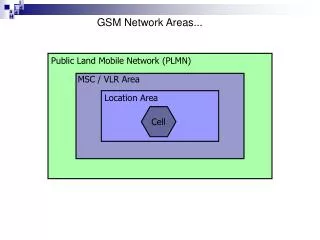
The GSM network • 1982 – Start of design • Group Spécial Mobile • 1991 – Commerical start • Global System for Mobile Communication • Worldwide system • Digital • Cellular • Subscriber Identity Module (SIM) • Flexible design (SMS, MMS, 2.5G, 3G, ...)
Security services • Authentication • Through challenge-response • Identity protection • Through temporary identification number • User data protection • Through encryption • Signaling data protection • Through encryption
Radio Interface „over-the-air“ Base Station Mobile Equipment Challenge RAND (128bit) KI(128 bit) KI(128 bit) A3 A3 Response SRES (32 bit) ? A8 A8 SIM KC (64 bit) KC(64 bit) Encrypted data A5 A5 GSM communication
Algorithms • Optimized for hardware • Never officially published („security by obscurity“) • A3 / A8 may be choosen by operator • COMP128 is assumed to be only a „proof of concept“
SIM RAND (128 bit) SRES (32 bit) A3 Ki (128 bit) Authentication: A3 • Input: Random challenge RAND + Secret Key Ki • Output: Signed response SRES • Completely implemented in the SmartCard • Ki never leaves the SIM • COMP128 algorithm or variations
SIM RAND (128 bit) Kc (64 bit) A8 Ki (128 bit) Key generation: A8 • Same algorithm as A3 • Output: Cipher key Kc • Only 56 bits of Kc are used
Encryption: A5 stream cipher • Input: • 228-bit data-frame every 4.6 ms • Framecounter Fn • Secret Key Kc produced by A8 • Clocked linear feedback shift registers (LFSRs) generate pseudo random bits PRAND • Output: • 114-bit ciphertext + 114-bit plaintext • Same PRAND used for encoding and decoding
R 1 0 8 13 16 17 18 C 1 Clocking Unit Output R 2 0 10 20 21 C 2 R 3 0 7 10 20 21 22 C 3 A5/1 scheme
A5 sequence • Zero registers • 64 cycles: Shift-in Kc • 22 cycles: Shift-in Fn • 100 cycles: Diffuse, with irregular clocking • 228 cycles: Generate output, with irregular clocking • XOR PRAND and frame-data
Majority R 1 0 12 13 14 15 16 17 18 Majority Output R 2 0 9 13 16 20 21 Majority R 3 0 7 13 16 18 20 21 22 Clocking Unit R 4 0 3 7 10 11 16 A5/2 scheme
Cryptanalytical attacks • Algorithms kept secret • After reverse-engineering, many attacks: • Golic, 1997 (A5/1) • Goldberg + Wagner, 1998 (COMP128) • Goldberg + Wagner + Briceno, 1999 (A5/2) • Biryukov+ Shamir + Wagner, 2000 (A5/1) • Biham + Dunkelman, 2000 (A5/1) • Ekdahl + Johansson, 2002 (A5/1) • Barkan + Biham + Keller, 2003 (A5/2) • COMP128 and A5/2 completely broken • A5/1 very weak
Attacks in real life • Knowledge and hardware needed • Only on short distances • More effective ways: • Wiretapping • Eavesdropping • Microphones with directional effect • ...
Conclusion „Every chain is only as strong as its weakest link“ • Good design, bad implementation • Tradeoff because of limited hardware capabilities • Future networks will use stronger ciphers • 3G: A5/3 „Kasumi“ = „Misty“ block cipher • Enough protection for everyday-users
Thank you! Questions? Thomas.Stockinger@nop.at http://www.nop.at