Polymorphic Viruses
Dr. Richard Ford rford@fit.edu. Polymorphic Viruses. What are we going to talk about?. Szor 7 Another way viruses try to evade scanners. Virus Scanners. Look for “known” viruses Basically, used to look for hex strings in files Virus writers tried to make this more difficult… .

Polymorphic Viruses
E N D
Presentation Transcript
Dr. Richard Ford rford@fit.edu Polymorphic Viruses
What are we going to talk about? • Szor 7 • Another way viruses try to evade scanners
Virus Scanners • Look for “known” viruses • Basically, used to look for hex strings in files • Virus writers tried to make this more difficult…
“Encrypted” viruses • First virus: Cascade • Benefit: Forces the vendor to choose a hex string from a small part of the virus code • Increases chances of a false positive
Cascade LEA si, Start MOV sp, 0682Decrypt: XOR [si], si XOR [si], sp INC si DEC sp JNZ DecryptStart:
Similarly… MOV EDI, 00403045hADD EDI, EBPMOV ECX, 0A6BhMOV AL, [key] Decrypt:XOR [EDI], ALINC EDILOOP DecryptJMP Start DB key 86 Start:
Nesting and other complications • Virus writer can implement multiple layers of “encryption” • Why do I keep using “”’s? • Use multiple keys • Start of loop can be obfuscated • Can “not” store the decryption key in the body • Can use strong Crypto (but…)
Weakness? • Well, in these examples, the decryption routine is static • Can detect on the decryption routine if not the virus body… can the attacker do better?
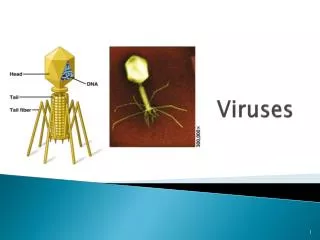
Oligomorphic Viruses • What? • Having or passing through few changes of form. • Example: Whale virus carried multiple decryptors with it • Of course, such viruses require painstaking analysis…
Polymorphic • Next level: millions of possible decryption routines, dynamically generated • First known: 1260 • Technique used: insert “junk” instructions into the decryption loop
Example • INC DINOPCLCINC AXLOOP Decrypt
Detection? • One possibility: code optimization • Well-known from other parts of CS… • But was attacked directly by MTE
Mutation Engine • Module for providing polymorphism • Called a function passing: • Work segment • Pointer to code to encrypt • Length of the virus body • Base of the decryptor • Entry-point of the host • Target location of the encrypted code • Size of decryptor (tiny, small, medium, large) • Bit field of registers not to use • Returns: a buffer containing the encrypted virus plus a decryption routine
MTE: Sample • MOV BP, A16CMOV CL, 03ROR BP, CLMOV CX, BPMOV BP, 856EOR BP, 740FMOV SI, BPMOV BP, 3B92ADD BP, SIXOR BP, CXSUB BP, B10C ; sets final value of BP…
Cntd… • Decrypt:MOV BX, [BP+0D2B]ADD BX, 9D64XCHG [BP+0D2B], BXMOV BX, 8F31SUB BX, BPMOV BP, 8F33SUB BP, BXJNZ DecryptSTART:
How to Detect? • Let’s talk about it…
Other Techniques • Carry your source and look for a compiler • Why is this so very horrible? • And then there’s System.Reflection.Emit to worry about…
Metamorphic Viruses • Muttik: “metamorphics are body-polymorphic” • Example: ZPerm • Uses JMPs to reorder its own code
Assignment • Due: 2 weeks today before class • Write a METAMORPHIC “Hello World” generator that: • Create 10 COM files • Each time you run, you should create different files • Must use C/C++ • Turn in the solution in SVN with JUST THE FILES I NEED to check out and compile with no challenges