Cryptographic Security
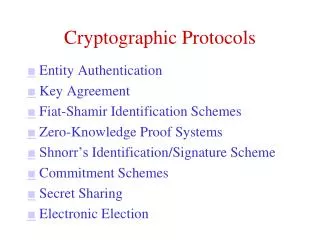
Cryptographic Security. Outline. Information security Encryption and keys Symmetric encryption DES Public-key cryptosystems RSA Digital signatures Digital certificates. Information Security. Keep data secret from unauthorized parties Authenticate identity of users

Cryptographic Security
E N D
Presentation Transcript
Outline • Information security • Encryption and keys • Symmetric encryption • DES • Public-key cryptosystems • RSA • Digital signatures • Digital certificates
Information Security • Keep data secret from unauthorized parties • Authenticate identity of users • Verify that messages have not been altered in transit • Prove that a party engaged in a transaction • Make it impossible for him to deny (nonrepudiation)
The Encryption Process OBJECT: HIDE A MESSAGE (PLAINTEXT) BY MAKING IT UNREADABLE (CIPHERTEXT) UNREADABLE VERSION OFPLAINTEXT MATERIAL WE WANT TO KEEP SECRET MIGHT BE: TEXT DATAGRAPHICS AUDIO VIDEO SPREADSHEET . . . DATA TO THE ENCRYPTION ALGORITHM MATHEMATICAL SCRAMBLING PROCEDURE (TELLS HOW TO SCRAMBLE THIS PARTICULAR MESSAGE) SOURCE: STEIN, WEB SECURITY
S P E C I A L T Y B D F G H J K M N O Q R U V W X Z A B C D E F G H I J K L M N O P Q R S T U V W X Y Z C O N S U L T I N G D S R A V G H E R M EXAMPLE: Role of the Key in Cryptography • The key is a parameter to an encryption procedure • Procedure stays the same, but produces different results based on a given key NOTE: THIS METHOD IS NOT USED IN ANY REAL CRYPTOGRAPHY SYSTEM. IT IS AN EXAMPLE INTENDED ONLY TO ILLUSTRATE THE USE OF KEYS.
Symmetric Encryption SAME KEY USED FOR BOTH ENRCYPTION AND DECRYPTION SENDER AND RECIPIENT MUST BOTH KNOW THE KEY THIS IS A WEAKNESS SOURCE: STEIN, WEB SECURITY
Data Encryption Standard (DES) • Symmetric, key-based encryption-decryption standard. No public keys • Block cipher: operates on 64-bit blocks • Uses 56-bit key • 16 “rounds” -- key for each round is a 48-bit function of the original 56-bit key. Each key bit participates in an average of 14 rounds • Completely symmetric. Same algorithm decrypts. • Fast implementation in hardware: 1 gigabit/second
Data Encryption Standard (DES) INPUT PERMUTATION 64 BITS OF MESSAGE LEFT HALF OF BLOCK (32 BITS) SUBKEYS: EACH IS A 48-BIT FUNCTION OF A 56-BIT KEY IS EXCLUSIVE-OR f IS A COMPLICATED FUNCTION INVOLVING VARIOUS PERMUTATIONS OUTPUT: 64 BITS OF ENCRYPTED TEXT INVERSE OF INPUT PERMUTATION SOURCE: SCHNEIER, APPLIED CRYPTOGRAPHY
Information Loss with Exclusive-OR • x y = 1 if either x or y is 1 but not both: • If x y = 1 we can’t tell which one is a 1 • Can’t trace backwards to determine values y x
Cracking Symmetric Encryption ESTIMATED TIME TO CRACK KNOWN SYMMETRIC ENCRYPTION ALGORITHMS (40-bit symmetric key = 384-bit PKE key)
Public-Key (Asymmetric) Encryption 3. SITE USES ITS PRIVATE KEY FOR DECRYPTION 2. SENDERS USE SITE’S PUBLIC KEY FOR ENCRYPTION 4. ONLY WEBSITE CAN DECRYPT THE CIPHERTEXT. NO ONE ELSE KNOWS HOW 1. USERS WANT TO SEND PLAINTEXT TO RECIPIENT WEBSITE SOURCE: STEIN, WEB SECURITY
Public-Key Encryption • Alice wants to send Bob a secure message M. • Alice uses Bob’s public key to encrypt M. • Bob uses his private key to decrypt M. • Bob is the ONLY ONE who can do this,so M is secure. • Problem: Anyone could have sent it. Was it really Alice? BOB’SPUBLIC KEY BOB’SPRIVATE KEY BOB DECRYPTS WITH HIS PRIVATE KEY ALICE ENCRYPTS WITH BOB’S PUBLIC KEY ALICE’SCLEARTEXT ALICE’SCODEDTEXT ALICE’SCODEDTEXT ALICE’SCLEARTEXT TRANSM ISSION
Digital Authentication • Alice wants to send Bob a message M so that Bob is sure Alice is the sender. • Alice uses her own private key to encrypt M. • Bob uses Alice’s public key to decrypt M. • Alice is the ONLY ONE who could have sent it. • Problem 1: Anyone can read it! Problem 2: Replay attack! ALICE’S PRIVATE KEY ALICE’S PUBLIC KEY BOB DECRYPTS WITH ALICE’S PUBLIC KEY ALICE ENCRYPTS WITH HER PRIVATE KEY ALICE’SCLEARTEXT ALICE’SCODEDTEXT ALICE’SCODEDTEXT ALICE’SCLEARTEXT TRANSM ISSION
BOB’S PUBLIC ALICE’S PRIVATE ALICE ENCRYPTS WITH HER PRIVATE KEY ALICE ENCRYPTS WITH BOB’S PUBLIC KEY ALICE’S PUBLIC BOB’S PRIVATE ALICE’SCODED ANDSIGNED TEXT ALICE’SCODED ANDSIGNED TEXT T R A N S M I BOB DECRYPTS WITH ALICE’S PUBLIC KEY BOB DECRYPTS WITH HIS PRIVATE KEY T ALICE’SCLEAR TEXT (DECRYPTED AND AUTHENTICATED) ALICE’SCODEDTEXT (AUTHENTICATED) ALICE’SCLEARTEXT ALICE’SCODEDTEXT Secure Authenticated Messages • Alice must send Bob a secret & authenticated message M so Bob is sure it was sent by Alice. Use both encryption and signature. 4 KEYS NEEDED:
Rivest-Shamir-Adelman (RSA) • It is easy to multiply two numbers but apparently hard to factor a number into a product of two others. • Given p, q, it is easy to compute n = p • q • Example: p = 5453089; q = 3918067 • Easy to find n = 21365568058963 • Given n, hard to find two numbers p, q with p • q = n • Now suppose n = 7859112349338149 What are p and q such that p • q = n ? • Multiplication is a one-way function • RSA exploits this fact in public-key encryption
RSA Encryption • Select two large prime numbers p, q (> 100 digits) • Let n = p • q • Choose a small odd integer e that does not dividem = (p - 1)(q - 1). Then x(p-1)(q-1) = 1 (mod n) • Compute d = e-1(mod m) • That is, d • e gives remainder 1 when divided by m • Public key is the pair (e, n) • Private key is the pair (d, n) • Knowing (e, n) is of no help in finding d. Still need p and q, which involves factoring n • DEMO
6 • 2 = 12 WHEN DIVIDED BY 7 GIVES REMAINDER 5 MULTIPLICATION MOD 7 EACH ROW EXCEPT THE ZERO ROW HAS EXACTLY ONE 1 EACH ELEMENT HAS A UNIQUE INVERSE Multiplicative InversesOver Finite Fields • The inverse e-1 of a number e satisfies e-1 • e = 1 • The inverse of 5 is 1/5 • If we only allow numbers from 0 to n-1 (mod n), then for special values of n, each e has a unique inverse
RSA Encryption • Message M is a number • To encrypt message M using key (e, n): • Compute C(M) = Me (mod n) • To decrypt message C using key (d, n): • Compute P(C) = Cd (mod n) • Note that P(C(M)) = C(P(M)) = (Me)d (mod n) = Me•d (mod n) = Mbecause e • d = 1 and m = (p-1)(q-1)
Message Digest (Hash) • A message digest is a “fingerprint” of a message • Much shorter than the original message (e.g. 160 bits) • Easy to compute • Can’t recover the message from the digest • Changing the message changes the digest MESSAGE (VERY LONG) DIGEST CAN BE USED TO VERIFY THAT THE MESSAGE HAS NOT BEEN ALTERED DIGEST
Single Step of SHA-1 80 WORDS INPUT HERE, 1 EACH STEP MAGIC CONSTANTS Operates on 16-word (512-bit) blocks Expands 16 words to 80 words Wt Performs 80 operations as shown for t = 0..79 a, b, c, d, e are special constants Kt are special constants + + + + REVISED CONSTANTS FOR NEXT STEP INITIALLY CONSTANTS “<<< 5” means “cyclic left shift 5 bits” SOURCE: SCHNEIER, APPLIED CRYPTOGRAPHY
MESSAGE (LONG) USE SECURE HASH ALGORITHM (SHA) TO PRODUCE HASH (MESSAGE DIGEST) HASH ENCRYPT HASH USING SIGNER’S PRIVATE KEY PRIVATE KEY SIG APPEND SIGNATURE TO MESSAGE; SEND BOTH DIGITALLYSIGNED MESSAGE SIG MESSAGE (LONG) Digital Signature • A function of both the message AND the signer’s private key (different for every message)
SIG MESSAGE (LONG) Authentication by Digital Signature RECIPIENT RECEIVES SIG + MESSAGE MESSAGE (LONG) RECIPIENT USES SHA TO COMPUTE HASH RECIPIENT DECRYPTS SIG WITH SIGNER’S PUBLIC KEY =? HASH HASH IF HASHES ARE EQUAL, MESSAGE IS AUTHENTIC. WHY? IF ANY BIT OF M OR SIG IS ALTERED, HASH CHANGES.
X.509 Version 2 Certificate VERSION # OF X.509 UNIQUE # ASSIGNED BY CA EXAMPLES: MD5RSA, sha1RSA USUALLY A DOMAIN NAME EXAMPLES: RSA SOURCE: FORD & BAUM, SECURE ELECTRONIC COMMERCE
Q A &