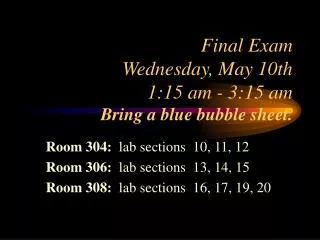
Final Exam Wednesday, May 10th 1:15 am - 3:15 am Bring a blue bubble sheet.
Final Exam Wednesday, May 10th 1:15 am - 3:15 am Bring a blue bubble sheet. Room 304: lab sections 10, 11, 12 Room 306: lab sections 13, 14, 15 Room 308: lab sections 16, 17, 19, 20. Computer Graphic Formats. Encoding Graphics, Pictures, and Images.

Final Exam Wednesday, May 10th 1:15 am - 3:15 am Bring a blue bubble sheet.
E N D
Presentation Transcript
Final ExamWednesday, May 10th 1:15 am - 3:15 amBring a blue bubble sheet. Room 304: lab sections 10, 11, 12 Room 306: lab sections 13, 14, 15 Room 308: lab sections 16, 17, 19, 20
Encoding Graphics, Pictures, and Images • Two different approaches to encoding graphics: • bitmap or raster • vector or object oriented
Bitmap • uses a code to indicate the state of each individual pixel • takes a lot of storage space for each image • slower file transfer times • .bmp .pcx .tif .gif .jpg • can modify by changing individual pixels • realistic images
Vector • consists of a set of instructions that recreate a picture • less storage space than a bitmap picture • can easily modify the picture • .wmf .dxf. .mgx .cgm
Sources of Graphics Files • Clip Art Gallery • Internet • Image scanner • Create your own • Microsoft Paint • Adobe
Computer Crime The use of computers to commit unauthorized acts.
Major Categories • manipulation or theft of data or assets • direct attack on hardware, software, or data • using the computer for conducting or planning a crime • unauthorized use of the computer for personal gain
Computer Crime Laws • different for each state • define computer data and software as personal property • define as a crime: • unauthorized access, use, modification of data • disabling a computer system
Federal Legislation • Computer Fraud and Abuse Act (1984) • Computer Fraud and Abuse Act (1986) • Computer Abuse Amendment Act (1994)
UW Computer Use Policy • Improper use includes, but is not limited to the following: • Use for personal gain, such as using the computing facilities for another job outside of the University. • Use which intentionally interferes with legitimate use by others. • Use of the electronic communication facilities to deliver threats to others, including sexual harassment.
Viruses • a program designed to reproduce itself and spread from one computer to another • can destroy data, display irritating messages or otherwise disrupt computer operations • generally infects the executable files
Other Software Hazards • Time Bombs • Michelangelo • Logic Bombs • Worms • Internet 1988 • Trojan Horses • Explore Zip • Denial of Service Attack
Detecting a Computer Virus • virus detection programs • checksum • signature • virus removal programs • information for virus protection for Windows 95/NT: • http://www.ccse.net/~tgrant/virus.htm
Preventative Measures • back up your data • use some type of virus detection and removal program and keep it updated • check any files downloaded from the Internet • always check e-mail attachments before opening or running them
Virus Information • http://www.symantec.com/avcenter/vinfodb.html • http://www.sophos.com/virusinfo/ • for information about virus hoaxes: • http://www.DataFellows.com/news/hoax.htm#aol4free