Reconnaissance & Scanning
610 likes | 962 Views
Reconnaissance & Scanning. By Letian Li ISQS 6342 (Spring 2003) Professor John Durrett. Reconnaissance.

Reconnaissance & Scanning
E N D
Presentation Transcript
Reconnaissance & Scanning By Letian Li ISQS 6342 (Spring 2003) Professor John Durrett
Reconnaissance • Using a combination of tools and techniques to take an unknown quantity of information and reduce it to a specific range of domain names, network blocks, and individual IP addresses of systems directly connected to the Internet. • Low-Technology Reconnaissance • Search the Fine Web • Use search engines • Whois Databases • Domain Name System
Low-Technology Reconnaissance • Social Engineering • Computer users must be trained not give sensitive information away to a friendly caller. • Physical Beak-in • A guard at the front door or a card reader checks all employees coming into a given facility. • Dumpster Diving • A well used paper shredder is the best defense against dumpster diving.
Search the Fine Web (STFW) • Searching an organization’s own web site • The Fine Art of using search engines • Listening in at the Virtual Watering Hole: Usenet
Searching an organization’s own web site • Employee’s contact information with phone numbers. • Clues about the corporate culture and language. • Business partners. • Recent mergers and acquisitions. • Technologies in use.
The Fine Art of using search engines • AltaVista • Excite • Google
Listening in at the Virtual Watering Hole: Usenet • Internet Usenet newsgroups are frequently used by employees to share information and ask questions. • Reveals sensitive information. • Web search engine such as www.groups.google.com provides a massive archive of an enormous number of newsgroups.
Defenses against web-based Reconnaissance • Establishing policies regarding what type of information is allowed in your own web servers. • Avoid including information about the products used in your environment, particularly their configuration. • Policy regarding the use of newsgroups and mailing list by employees. • Avoid posting information about system configurations, business plans, and other sensitive topics.
Whois Databases: treasure Chests of Information • Whois Databases contain a variety of data elements regarding the assignment of Internet addresses, Domain names, and individual contacts. • Researching .com, .net, and .org Domain Names. • A complete list of all accredited registrars is available at www.internic.net/alpha.html. • www.internic.net/whois.html • Allows a user to enter an organization’s name or domain name. • Researching Domain Names Other Than .com, .net, and .org. • For organizations outside of the United States, a list can find from www.allwhois.com/home.html.
IP Address Assignments through ARIN • American Registry for Internet Numbers. • Contains all IP addresses assigned to particular organization. • Users can access the ARIN whois database at http://www.arin.net/whois/index.html. • European IP address assignments can be retrieved at www.ripe.net.
Defenses against Whois Searches • Database information that is useful for attackers should not be available to the public. • Can we use some erroneous or misleading registration information? • You can quickly and easily get the contact information using whois searches. • The whois database information let us inform an administrator that their systems were being used in an attack.
Defenses against Whois Searches • There rally is no comprehensive defense to prevent attackers from gaining registration data.
The Domain Name System • DNS is a hierarchical database distributed around the world that store a variety of information, including IP addresses, domain names, and mail server information. • DNS servers store this information and make up the hierarchy.
Interrogating DNS Servers • nslookup command • Windows Nt/2000 • Most variations of Unix • host command • Included with most variations of UNIX • dig command • Included with some UNIX variants
Defenses from DNS-Based Reconnaissance • Make sure you aren’t leaking information unnecessarily through DNS servers. • Restrict zone transfers. • Use “split DNS” to limit the amount of DNS information about your infrastructure.
We’ve got the registrar, now what? • Names: Complete registration information includes the administrative, technical, and billing contact names. • An attacker can use this information to deceive people in target organization during a social engineering attack. • Telephone numbers • The telephone numbers associated with the contacts can be used by an attacker in war-dialing attack.
We’ve got the registrar, now what?(cont.) • Email addresses: this information will indicate to an attacker the format of email addressed used in the target organization. • The attacker will know how to address email for any user. • Postal addresses: • An attacker can use this geographic information to conduct dumpster-diving exercises or social engineering.
We’ve got the registrar, now what?(cont.) • Registration dates: • Older registration records tends to be inaccurate. • A record that hasn’t been recently updated may indicate an organization that is lax in maintaining their Internet connection. • Name severs: • This incredibly useful field includes the addresses for the Domain Name system servers for the target.
General Purpose Reconnaissance Tools • Sam Spade, a General-Purpose Reconnaissance Client Tool. • One of the easiest to use and most functional integrated reconnaissance suites available today. • Runs on Windows 9X, NT, and 2000. • Available at www.samspade.org/ssw/
Sam Spade’s Capabilities • Ping: This tool will send an ICMP Echo request message to a target to see if it is alive and determine how long it takes it to respond. • Whois: Conduct Whois lookups using default Whois servers, or by allowing the user to specify which Whois database to use. • IP Block Whois: Used to determine who owns a particular set of IP addressed, using ARIN databases. • Nslookup: Querying a DNS server to find domain name to IP address mapping. • DNS Zone Transfer: Transfers all information about a given domain from the proper name serer.
Sam Spade’s Capabilities (cont.) • Traceroute: Return a list of router hops between the source machine and the chosen target. • Finger: Supports querying a system to determine its user list. • SMTP VRFY: Determine whether particular email addresses are valid on a giver email server. • Web browser: Sam Spade’s built-in mini browser lets its users view raw HTTP interaction, including all HTTP headers.
General Purpose Reconnaissance Tools(cont.) • Other client-based reconnaissance tools similar to Sam Spade include: • cyberKit: A freeware tool fro Windows available at http://www.twpm.com/internet/downloads/cyberkit.htm • iNetScanTools: a feature-limited demonstration tool from windows and Macintosh, available at www.wildpackets.com/products/inettools
Web-Based reconnaissance tools: Research and Attack Portals • www.samspade.org • www.network-tools.com • www.securityspace.com/ • www.grc.com/x/ne.dll?bhobkyd2 • www.doshelp.com/dostest.htm • www.dslreports.com/r3/dsl/secureme
Scanning • Scanning phase is akin to a burglar turning doorknobs and trying to open windows to find a way into your house. Common techniques include: • War Dialing • Network Mapping • Port Scan • Vulnerability Scan
War Dialing • A war-dialing tool automates the task of dialing large pools of telephone numbers in an effort to find unprotected modems. • An attacker can scan in excess of a thousand telephone numbers in a single night using a single computer with a single phone line. • More computers and phone line make the scan even faster.
War Dialer vs. Demon Dialer • A war dialer is a tool used to scan a large pool of numbers to find modems and other interesting lines. • A demon dialer is a tool used to attack just one telephone number with a modem, guessing password after password in an attempt to gain access. • War dialing focuses in scanning a variety of telephone numbers, while demon dialing focuses in gaining access through a single telephone number.
A Toxic Recipe: Modems, remote Access Products, and Clueless Users • By default, many of these remote control products include no password for authentication. • Anyone dialing up to a system with war-dialer installed has complete control over the victim machine without providing even password. • We can discover modems connected to servers and routers that either request no password or have a trivial-to-guess password.
Finding Telephone Numbers to Feed into a War Dialer • The phone book. • The Internet. • Whois databases. • Your organization’s Web site. • Social engineering.
War-Dialing Tools • THC-Scan 2.0. • THC-Scan is one of the most full-featured, noncommercial war dialing tool available today. • You can find it at www.ussysadmin.com/modules.php?name=Downloads&d_op=search&query= • l0pht’s TBA War-Dialing Tool • Available at www.l0pht.com
The War Dialer provides a List of Lines with Modems: Now What? • The attacker may find systems without password. The attacker will connect to such system, look through local files, and start to scan the net work. • If all of the discovered systems with modems are password protected, the attacker will then sort to password guessing.
Defenses against War Dialing • Modem policy. • Dial-out only? • While this technique works quite well, some users have a business need that requires incoming dial-up modem access. • Find your modems before the attackers do. • Use a commercial war dialer. • www.sandstorm.netwww.securelogix.com • Desk-to-desk checks.
Network Mapping • Network mapping" is the effort to map • Topology • How network components are connected to each other to build up the network. • Network devices • Types, brands, versions etc. • Computers and services • Computers and their placement, vendors and models of running O.S.'s, published services
Common Network Mapping • Sweeping: Finding Live Hosts. • Traceroute: What Are the Hops?
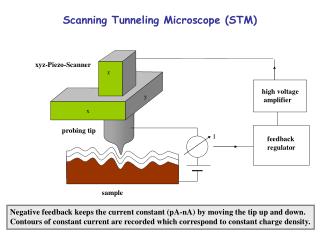
Sweeping: finding Live Hosts • ICMP • Send an ICMP Echo Request packet to every possible address. • If a reply comes back, that address has an active machine. • But many networks block incoming ICMP messages.
Sweeping: finding Live Hosts (cont.) • TCP/UDP • An attacker could alternatively send a TCP or UDP packet to a port that is commonly open, such as TCP port 80. • If nothing comes back, there may or may not be a machine there.
Traceroute: What Are the Hops? • Tracerouting relies on the Time-To-Live (TTL) field in the IP header. • Start with a TTL of one. This process continues with incrementally higher TTLs until reach the destination. • ICMP Time Exceeded message has the router’s IP address. • Most UNIX varieties include a version for the traceroute program. • Windows NT and Windows 2000 include tracert program.
Cheops: A Nifty Network Mapper and General-Purpose Management Tool • Available at www.marko.net/cheops • Runs Linux.
Defenses against Network Mapping • Filter out the underlying messages that mapping tools rely on. • At Internet gateway, block incoming ICMP messages, except to hosts that you want the public to be able to ping. • Filter ICMP TIME Exceeded messages leaving your network to stymie an attacker using traceroute(tracert).
Determining Open Ports Using Port Scanners • Discover the purpose of each system and learn potential entryways into your machines by analyzing which ports are open. • The attacker may focus on common services like telnet, FTP, email. • Free port-scanning tools: • Nmap, at www.insecure.org/nmap/. • Ultrascan. • Strobe.
Nmap: A Full-Featured Port Scanning Tool • A nice GUI for Nmap.
Common Type of Nmap Scans • TCP Connect • TCP SYN Scans • TCP FIN, Xmas Tree, and Null Scans • TCP ACK Scans • FTP Bounce Scans
The Polite scan: TCP Connect Complete the TCP three-way handshake. Connect scans are really easy to detect. The web server’s log file will indicate that a connection was opened from the attacker’s IP address. Attackers often use stealthier scan techniques.
A Little Stealthier: TCP SYN Scans • SYN scans stop two-thirds of the way through the handshake. • If the target port is closed, the attacker’s system will receive either no response, a RESET packet, or an ICMP Port unreachable packet, depending on the target machine type and network architecture. • Benefits: • Stealthier. A true connection never occurs. • Speed.
Violate the protocol Spec: TCP FIN, Xmas Tree, and Null Scans • A FIN packet instructs the target system that the connection should be torn down. • A closed port should respond with a RESET. • An open port will respond nothing. • Xmas Tree and Null scan are similar to FIN Scan. • Unfortunately, this technique does not work against Microsoft Windows-based systems.
Obscure the Source: FTP Bounce Scans • Some old FTP servers allow a user to connect to them and request that the server send a file to another system. • Attacker opens a connection to a FTP server supporting the bounce feature. • The attacker’s tool requests that the innocent FTP server open a connection to a given port in the target system. • Innocent FTP then will tell the attacker the status of the port.
Don’t Forget UDP! • UDP does not have a three-way handshake, sequence numbers, or code bits. • Packets may be delivered out of order, and are not retransmitted if they are dropped. • False positives are common during UDP scan.
Setting Source Ports for a successful Scan • TCP port 80 is a popular choice for a source port, as the resulting traffic will appear to be coming from a Web server using HTTP. • Attackers also widely use TCP source port 25, which appears to be traffic from an Internet mail server using the SMTP protocol. • Another interesting option involves using a TCP source port of 20, which will look like an FTP-data connection.
Defenses against port Scanning • Harden your systems. • Close all unused ports. • For critical systems, delete the programs associated with the unneeded service. • Find the Openings before the Attackers Do. • Scan your systems before an attacker does to verify all ports are closed except those that have a defined business need. • Add Some Intelligence: Use Stateful Packet Filters or Proxies.
Vulnerability Scanning Tools • A vulnerability-scanning tool will automatically check for the following types of vulnerabilities on the target system: • Common configuration errors: Numerous systems have poor configuration settings, leaving various openings for an attacker to gain access. • Default configuration weaknesses: default accounts and passwords. • Well-known system vulnerabilities: new security holes are discovered and published.