Carnivore
E N D
Presentation Transcript
Carnivore The Electronic Surveillance Tool Pedro E. Cusinga CIS450 Strayer University
Some Statistics • Not even ten years ago , most people didn’t know what the Internet or e-mail was. • Before that, most people didn’t have computers at home or at work • Fifty years ago, In fact, there were no computers • Today, one in two Americans has computers at home or at work, and the use of the Internet has became the preferred medium for communication exchange • Now that the use of Internet is growing exponentially, so is the computer crime. • Criminals use the Internet’s inexpensive and easy communications to commit, fraud, theft, larceny, forgery, sabotage, espionage, terrorism, information warfare, hacking and many other serious and violent crimes.
But, who is out there to protect us? • The FBI is. • In fact, the FBI along with many other law enforcement agencies ,are busy conducting lawful electronic surveillance to prevent serious criminal activities. • It has become common knowledge that that terrorist, spies, hackers, and many other dangerous criminals are occupied using computers and computer networks,Including the Internet, to commit their malicious acts. Counterattacking criminal activities Investigating and deterring such wrongdoing not only requires tools and techniques designed to work with new evolving computers and network technologies . But it also requires to work in coordination and under the supervision of the Department of Justice.
Types of Cyber-crimes threats that law enforcement agencies have been and will encounter in the future. • To begin with, in every FBI investigation involving electronic surveillance, all surveillance efforts are approved, monitored, and overseen at each step of the way by both the local United States Attorneys Office and the appropriate U.S. District Court Judge. • In surveillance conducted under the Foreign Intelligence Surveillance Act (FISA), FBI is monitored and overseen by the Department of Justice’s Office of Intelligence Policy and Review, and by the Foreign Intelligence Surveillance Court. • Terrorism - Terrorist groups are increasingly using new information (IT) and the Internet to formulate plans ,raise founds, spread propaganda, and communicate securely • Espionage - Foreign intelligence services view the Internet and computer intrusions as useful tools for acquiring sensitive U.S. government and private sector information. • Information Warfare - Perhaps the greatest threat to national security by foreign militaries against the Nation’s critical infrastructures.
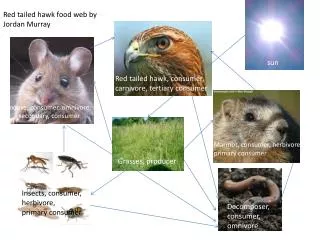
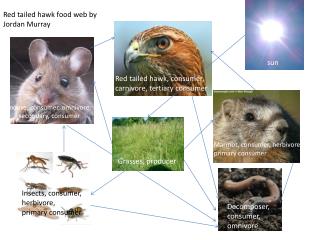
The Electronic Surveillance Process • Child Pornography and Sexual Exploitation of Children - Sexual predators find the Internet as the perfect medium to trap unwary children. • Serious Fraud - The North American Securities Administrators Association has estimated that Internet-related stock fraud results in a loss of approximately $10 billion per year (nearly $1 million per hour) Thedecision to use Carnivore comes only after a criminal investigation has proceed substantially. • First, the FBI must demonstrate that a crime has been committed or is about to be committed • Second, the FBI must explain why traditional enforcement methods are insufficient to obtain the information desired. • Third, in order to obtain a court order, the FBI must discover the identity of the target’s ISP, e-mail address, etc. • Fourth, the FBI will seek to deploy such means only in large ongoing investigations. • Fifth, FBI agents will use electronic surveillance as a last resort.
Deployment of carnivore Carnivore is a very specialized network analyzer or “sniffer” which runs as an application program in a normal computer under the Microsoft Windows operating system. It works by “sniffing the proper portions of network packets and copying and storing only those packets in conformity with the court order The Carnivore device provides the FBI with a “surgical” ability to collect only the data they are looking for while ignoring those communications which they are not authorized to intercept. Carnivore is superior to any commercial-available “sniffer” tool. Commercial sniffers are typically designed to work only with fixed IP addresses.Carnivore on the other hand was specifically designed to interface with ISP networks so that when dynamic addressing occurs it can immediately respond to it.
The example above shows how the system identifies which packets to store
System Architecture The carnivore system architecture comprises of: 1- A one-way tap into an Ethernet data steam 2- A general purpose computer to filter and collect data 3- Additional general purpose computers to control the collection and examine the data 4- A telephone link to the collection computer, and 5- DragonWare software written by the FBI. DragonWare includes Carnivore software to filter and record IP packets and Packeteer and CoolMiner, which are two additional programs that reconstruct e-mail and other Internet traffic from the collected packets.
THE ETHERNET TAP Carnivore is connected to a 10Base-T Ethernet using a Century Tap made by Shoniti Systems. In a typical installation, an existing line is disconnected from a hub or switch and plugged into port A of the tap. A new line is run from port B to the hub/switch. The tap passes the traffic along the line from A to B to A if it were standard cable. At the same time, it takes a copy of the transmit data in each direction and feeds it to ports 1 and 2. Additional cables connect ports 1 and 2 to standard hub. This connection ensures that both sides of the communication on the Ethernet appear at the hub, but no data can be sent from the hub. The carnivore system is then connected to any open port on the hub.
This cabling arrangement and the Shoniti tap ensure Carnivore is in a receive-only mode. The FBI technicians who install Carnivore work with ISP personnel to have Carnivore connected to the smallest bandwidth pipe possible.
CARNIVORE SOFTWARE PROGRAM • Carnivore is the name of the software program running on the collection computer that filters and records IP packets. When the collection computer is started, it automatically logs in as the Administrator. • Carnivore has two levels of functionality: a main screen and an advanced screen. • When the program is started, the agent sees the main screen with four functions implemented via button selections. One set of buttons starts and stops collection. Another toggles the collection detail display. A third forces collection to start using a new file, making the current file available for downloading. The fourth is used to access the advanced screen (filter settings). • The program has a separate password for accessing the filter settings. A case agent, can access the collection device via device via remote dial-in to start and stop the collection, and cause the collection to start into a new file and download the collected data. However, that agent does not need to know the password that allows the filter settings to be changed.