ECDL/ICDL IT Security
Year 10 ICT. ECDL/ICDL IT Security. What is it about?.

ECDL/ICDL IT Security
E N D
Presentation Transcript
Year 10 ICT ECDL/ICDL IT Security
What is it about? • This module sets out essential concepts and skills relating to the ability to understand main concepts underlying the secure use of ICT in daily life. It also teaches us to use relevant technologies and applications to maintain a secure network connection, use the internet safely and securely, and manage data and information appropriately.
Goals of this Module • Understand the key concepts relating to the importance of secure information and data, physical security, privacy and identity theft. • Protect a computer, device or network from malware and unauthorised access. • Understand the types of networks, connection types and network specific issues including firewalls. • Browse the World Wide Web and communicate on the internet securely. • Understand security issues related to communications including email and instant messaging. • Back up and restore data appropriately and safely, and securely dispose of data and devices.
1 Security Concepts This section will introduce the main concepts underlying the secure use of ICT in daily life. It will explain threats to your data, and give you an understanding of measures you can take to protect it. 1.1 Data Threats When working with data, it is important to be aware of potential threats that may pose a security risk through the theft of or loss of the data. Once you are aware of potential threats, it is easier to protect yourself and your data against the outcome of these threats. Methods of protection will be covered later in this Module. 1.1.1 Distinguish between data and information Data are facts, numbers or images that are collected to be examined and considered, in order to help in decision-making. Information is the interpretation of this data in a structured way, in order to provide knowledge based on study, experience or instruction. For example, if you conduct a survey to ask 500 people of different ages and different professions how they use IT in their day- to - day lives, the answers these 500 people give to your questions are ‘data’. When you analyse this data, you obtain ‘information’, which gives you knowledge about how the use of IT is affected by age and profession.
Data Threats • When working with Data, it is important to be aware of potential threats that may pose a security risk through theft or loss of data. • Once you are aware of potential threats, it is easier to protect yourself against them.
Distinguishing between Data and Info • Data is facts, images and/or numbers that are collected to be examined and considered in order to help make decisions. • Information is the interpretation of this data in a structured way. • Example: You ask 200 people what type of phone they have. The answers you receive are classified as data. When you analyse this date, you get information.
Cybercrime • Cybercrime is the use of any computer, or network, to commit a crime. • Financial Scam • Computer Hacking • Downloading Pornographic Images from the Internet • Virus Attacks • Stalking by email • Creating Websites that promote racial hatred • Identity theft • Social Engineering.
Hacking, Cracking and Ethical Hacking • A hacker is an individual who attempts to bypass the security mechanisms of a network or information system. • A cracker is someone who exploits the weaknesses and security holes with malicious intent such as blocking accounts, or stealing information.
Hacking, Cracking and Ethical Hacking • Ethical hackers are computer security experts. They are employed by a company to attempt to bypass the security of said company’s information systems. The company can then act on this information, making their network safer.
Threats to Data • Force majeure relates to unforeseen events beyond the control of the company. Items include war, natural disasters, system crashes and corruption. • Employees can pose a risk to confidential information. They could pass information on to other people, or use it for their own advantage. They could even accidentally delete it.
Value of Information • Personal Information is any info or combination of information that enables the identification of an individual. • Personal information must be protected to prevent: • Internet based fraud • Identity Theft
Value of Information • Commercially Sensitive Information includes: • Statements of financial information • Information of a company’s pricing structure • Information in the nature of operating and financial information • Current client lists, production costs, hourly rates etc.
Value of Information • Commercially sensitive information must be protected to prevent: • Theft • Misuse of client details • Misuse of financial information
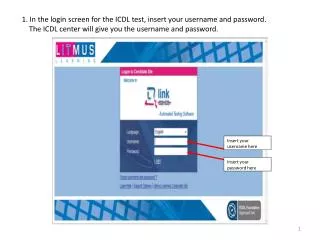
Preventing Unauthorized Access to Data • Using a username and have a good password • How strong is your password? (school, social media, home) • www.passwordmeter.com
Protecting Data • Data Encryption The process of transforming information (plaintext) using an algorithm (cipher) to make it unreadable to anyone except those possessing special knowledge. The resulting product is encrypted information (ciphertext). Reversing the process is called decryption.
Data and the Law • The way computers can process, store and transfer data has necessitated some form of legislation to protect the privacy of individuals.
Data and the Law • Anyone with personal data on their computer (Data Controllers) must ensure that: • Personal data is processed fairly and lawfully • Personal data is always processed in accordance with good practice • Personal Data is only collected for specific explicitly stated and legitimate purposes. • Personal data is not processed for any purpose that is incompatible with that for which the information is collected. • Personal Data that is processed is adequate and relevent in relation to the purposes of the processing.
Data and the Law • No more personal data is processed than is necessary having regard to the purposes of the processing. • Personal data that is processed is correct and, if necessary, up to date. • All reasonable measures are taken to complete, correct, block, or erase data to the extent that such data is incomplete or incorrect, having regard to the purposes for which they are processed. • Personal data is not kept for a period longer than is necessary.
Personal Security • Social engineering is a way to manipulate or influence people with the goal to illegally obtain sensitive data. Social engineers gather this information through phone calls, phishing and shoulder surfing.
Definitions • Phishing: A technique of fraudulently obtaining private information. Usually in the form of a fake email, that appears to be from a legitimate business requesting verification of information. • Shoulder Surfing: Looking over someone's shoulder to see information they are entering into a computer.
Implications of Identity Theft • Personal • Can be devastating, causing emotional distress, anxiety, and even triggering depression. • Financial • Financial histories and credit records can suffer from identity theft leading to the loss or misuse of one of more existing accounts. • Business • Particularly in credit and financial fields, also suffer financial losses. A business can suffer from lost time and productivity when the victim is an employee. • Legal • Re-establishing a legal identity, including personal details, passport and tax records.
Methods of Identity Theft • Information Diving • The practice of recovering technical data • Skimming • An electronic method of capturing a victim’s personal information used by identity thieves. The skimmer is a small device that scans a credit card and stores the information found in the magnetic strip. • Pretexting • Creating and using an invented scenario to engage a targeted victim.
Advantages and Limitations of Encryption • Advantages: • Protect information stored on your computer from unauthorised access • Protect information while it is in transit from one computer system to another • Deter and detect accidental or intentional alterations • Verify whether or not the author of a document is really who you think it is.
Advantages and Limitations of Encryption • Limitations • If you forget your password then there is almost no chance of recovering your data • Some forms of encryption only offer nominal protection and can be broken easily. • Encrypted files attracts a suspicion as to what it is you are trying to protect. • Cannot prevent deletion of data.
Review • The process of intentionally accessing a computer without authorisation or exceeds access is known as: • A) Cracking • B) Phishing • C) Hacking • D) Pretexting
Review • The process of intentionally accessing a computer without authorisation or exceeds access is known as: • A) Cracking • B) Phishing • C) Hacking • D) Pretexting
Review • Which of the following is not a basic characteristic of information security? • A) Confidentiality • B) Locality • C) Integrity • D) Availability
Review • Which of the following is not a basic characteristic of information security? • A) Confidentiality • B) Locality • C) Integrity • D) Availability
Review • Encryption is the process of transforming plaintext using an algorithm to create ________ and make it unreadable by the use of a key • A) Pretext • B) Short Text • C) Gibberish Text • D) Ciphertext
Review • Encryption is the process of transforming plaintext using an algorithm to create ________ and make it unreadable by the use of a key • A) Pretext • B) Short Text • C) Gibberish Text • D) Ciphertext
Review • Which one of the following terms describes the process of someone monitoring you keying in your ATM pin with malicious intent? • A) Shoulder Surfing • B) Phishing • C) cyber Bullying • D) Cracking
Review • Which one of the following terms describes the process of someone monitoring you keying in your ATM pin with malicious intent? • A) Shoulder Surfing • B) Phishing • C) cyber Bullying • D) Cracking