Security & .NET
Security & .NET. Contents . Introduction Security : overview .NET Framework Architectures Conclusion. Introduction . Advent of Networking Sharing through Internet Distributed environment Challenges of Dist. Environment Security Key goal of .NET:

Security & .NET
E N D
Presentation Transcript
Contents • Introduction • Security : overview • .NET Framework • Architectures • Conclusion
Introduction • Advent of Networking • Sharing through Internet • Distributed environment • Challenges of Dist. Environment • Security • Key goal of .NET: • Securely Manage who ,and what, accesses their data
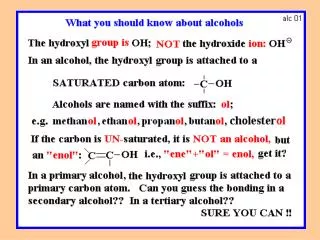
Security : overview • .NET Framework • Foundation for .NET dev. Technologies • Basis for easy building , deploying & executing : • XML based web services • web applications • client applications
Security ( Contd.. ) • .NET Framework • CLR • Execution engine for .NET Framework based apps • Functions • Code Management • Memory Management for apps & objs • Security rules enforcement • Access control for code • Interoperation between code & pre-existing COM objs
Security ( contd.. ) • .NET Framework • Class Libraries • Provides functionality for : • User interface design • Threading • Security Management • NT communications etc.
Security ( contd.. ) • .NET Framework • Security features • Role-based • Evidence-based • Code-based • Cryptography
Security ( contd.. ) • Role-based Security • Applications use role-based security to enforce business rule constraints • Individuals are grouped into roles with varying levels of access • .NET role-based security works by making user and role information available to the current thread • Unified model for Authentication & Authorization
Security ( Contd.. ) • Role-based Security (Contd..) • Authentication : • Examining user credentials • Authorization : • Analyzing user roles – what rights and operations allowed to perform • .NET Framework provides support for common authentication protocols • KERBEROS • SSL/TLS etc.
Security ( Contd.. ) • Role-based Security (Contd..) • .NET Framework also enables • Developers to incorporate .NET passport authentication & cookie based authentication • Great deal of flexibility with authorization • Ex. devs can use XML to designate to what level of access users have etc.
Security ( Contd.. ) • Evidence-based • granting access based on evidence shown • ex: • Code signed with a certain key or having certain hash value • gives more granular support for admins to control dangerous , partially trusted code
Security ( Contd.. ) • Code – Access • Similar to evidence based • Ex. code residing in a directory • Similar access as in evidence-based • Four different possibilities: • Trusted user , un-trusted code • Un-trusted user , trusted code • Trusted user , Trusted code • Un-trusted user , Un-trusted code
Security ( Contd.. ) • Code-Access (Contd..) • Hence has to authorize both users and code • No runtime security decisions by users • Code is verified by memory type safe • only access objects it has reference to • only use defined interfaces to objects • also , well informed metadata and instructions
Code-Access ( Contd.. ) • C# , VB verifiable • C++ not verifiable • Permissions can always be defined to limit access to system resources • Stack walk • Demand must be satisfied by all callers
Security ( Contd.. ) • Cryptography • .NET Framework includes functions for • Encryption • Hashing • Digital signatures • Random No. generation
Architectures • Global XML Web Services Architecture (GXA) • XML web services are the building blocks in the move to distributed computing on internet. • These web services provide greater level of interoperability through numerous protocols • XML • SOAP • UDDI • GXA is Microsoft’s Web service architecture with added reliability and security
Architectures (Contd..) • GXA ( Contd.. ) • Key design principles : • Modularity • Built on modular components which can be used to create solutions giving exact set of features • General purpose • Designed for variety of XML web service scenarios including B2B , B2C , P2P apps • Federated • Standards based • Built on standard XML web services and protocols
Architectures (Contd..) • GXA ( Contd.. ) • Security in GXA • Using WS-Security specification • defines Std. set of SOAP extensions for implementing integrity and confidentiality in Web services applications • Provides standard mechanisms to exchange secure, signed messages in a Web services environment • Provides an important foundation layer that will help developers build more secure and broadly interoperable Web services.
Architectures (Contd..) • .NET Passport • Centralized model of FIM • Subsequent sites gets user authentication info by CCD (Component configuration Document) • CCD is an XML doc.
Conclusion • XML playing crucial role in distributed env • .NET provides means for the info to travel seamlessly and securely between applications , web sites and devices. • .NET provides all round security in to the new world of distributed computing and WS.