Access Control
Access Control. Given Credit Where It Is Due. Most of the lecture notes are based on slides by Dr. Daniel M. Zimmerman at CALTECH Some slides are from Prof. Kenneth Chiu at SUNY Binghamton I have modified them and added new slides. Access Control.

Access Control
E N D
Presentation Transcript
Given Credit Where It Is Due • Most of the lecture notes are based on slides by Dr. Daniel M. Zimmerman at CALTECH • Some slides are from Prof. Kenneth Chiu at SUNY Binghamton • I have modified them and added new slides
Access Control • Once a client and a server have established a secure channel, the client can issue requests to the server • Requests can only be carried out if the client has sufficient access rights • The verification of access rights is access control, and the granting of access rights is authorization • These two terms are often used interchangeably
The Basic Model for Access Control • This model is generally used to help understand the various issues involved in access control • The subject issues requests to access the object, and protection is enforced by a reference monitor that knows which subjects are allowed to issue which requests
Access Control Matrix • The access control matrix is a matrix with each subject represented by a row, and each object represented by a column • The entry M[s, o] lists the operations that subject s may carry out on object o • Is this matrix a good way to represent access rights • Of course, we don’t really want to implement it as a matrix in any system of reasonable size, because there would be a whole lot of wasted space… ? ?
Access Control Matrix • There are two main approaches that are used instead of an actual matrix: • Each object can maintain a list, the access control list, of the access rights of subjects that want to access that object - this effectively distributes the matrix column-wise, leaving out empty entries • Each subject can maintain a list of capabilities for objects - this effectively distributes the matrix row-wise, leaving out empty entries • Of course, capabilities can’t be totally maintained by the subjects - they must be given to the subjects by some other trusted entity (like the reference monitor)
Protection Domains • ACLs and capabilities help to efficiently implement the access control matrix, but can still become quite cumbersome • A protection domain is a set of (object, access rights) pairs, where each pair specifies for a given object exactly what operations can be carried out • By associating a protection domain with each request, we can cut down on redundant information in access control lists
Protection Domains • One approach to using protection domains is to construct groups of users • Another approach is to use roles instead of groups • Roles: head of a department, manager of a project, member of a personnel search committee
Firewalls • We can use encryption to protect the files that make up the access control matrix, and various secure channel protocols to communicate that information to the objects that need it • This works well, as long as all the components in the system play by the same sets of rules - but that might not always be the case…
Firewalls - Example • Take the idea of an NFS server, which uses UNIX user and group IDs to control access to files • This works great on a private network where you can guarantee that none of the machines’ local user and group databases will be tampered with • If I tamper with a machine, create a new user with some existing user ID in my password file, and then hop onto the NFS server, I can access all that user’s files and exercise all his rights!
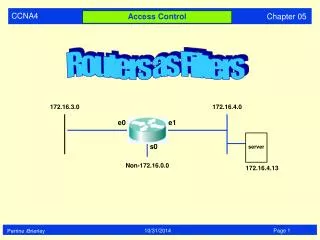
Firewalls • A firewall is a special kind of reference monitor that inspects packets traveling into and out of a private network to ensure that they aren’t harmful • There are two main types: • Packet-filtering gateways inspect only the headers of packets travelling on the network, for example, based on the source and destination addresses • Application-level gateways inspect the contents of the packets as well, for example, spam email filters
Secure Mobile Code • Code migration: It’s important to protect hosts against malicious mobile agents, and also to protect the mobile agents against malicious hosts • Much more attention has been paid to the former, because the latter is in a sense impossible - even if you protect the agent from tampering with various cryptographic techniques, nothing prevents a host from simply keeping the agent a prisoner forever
Secure Mobile CodeProtecting the Host • One approach to protecting the host is to build a sandbox, which allows the execution of a downloaded agent to be fully controlled • If the agent attempts to execute an instruction that the host doesn’t like, it can be terminated by the host • Implementing a sandbox is nontrivial • Probably the best known example is the Java sandbox model
Secure Mobile CodeThe Java Sandbox Model • The Java sandbox model consists of several components: • Class Loaders • Byte Code Verifier • Security Manager
Secure Mobile CodeThe Java Sandbox Model • Class loaders are responsible for fetching classes from servers and installing them in the host’s JVM • Only trusted class loaders are used - a Java program can’t circumvent the sandbox by creating some special kind of class loader • A byte code verifier checks whether downloaded classes obey the sandbox’s security rules • In particular, it checks to see if the code contains illegal instructions or instructions that could corrupt the stack or memory
Secure Mobile CodeThe Java Sandbox Model • A security manager performs checks at runtime to ensure that mobile code doesn’t break any rules • For instance, downloaded code cannot write to the filesystem unless given special permission to do so • In the original Java security model, the security manager was very strict and didn’t distinguish programs from different servers- Java’s current security model is much more flexible
Secure Mobile CodePlaygrounds • An alternative model is to designate a single machine on the local network as a playground in which mobile code can run • Resources local to the playground are available to code running in the playground, while resources local to other machines are isolated from the playground
Secure Mobile CodeSandboxes vs. Playgrounds • (a) illustrates a sandbox-based system, while (b) illustrates a playground-based one
Distributed Denial of Service • DDoS • Can be classified into two kinds, roughly. Bandwidth depletion and server resource depletion. • How does a typical DDoS work? How can we protect against them?
Distributed Denial of Service • No single way to protect, need comprehensive plan • Protect machines from getting taken over. • Monitor egress routers. • Monitor ingress (how well does this work?) • Monitor overall network.