BB84 Quantum Key Distribution
280 likes | 626 Views
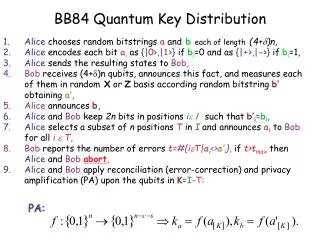
BB84 Quantum Key Distribution. Alice chooses random bitstrings a and b each of length (4+ )n, Alice encodes each bit a i as {| 0 >,| 1 >} if b i =0 and as {| + >,| - >} if b i =1, Alice sends the resulting states to Bob ,

BB84 Quantum Key Distribution
E N D
Presentation Transcript
BB84 Quantum Key Distribution • Alice chooses random bitstringsaandb each of length(4+)n, • Alice encodes each bitaias {|0>,|1>} ifbi=0 and as {|+>,|->} ifbi=1, • Alice sends the resulting states toBob, • Bob receives (4+)n qubits, announces this fact, and measures each of them in random X or Z basis according random bitstringb’obtaininga’, • Alice announcesb, • Alice andBob keep 2n bits in positionsisuch thatb’i=bi, • Alice selects a subset of n positionsTinIand announcesaitoBobfor alli e T, • Bob reports the number of errorst=#{ieT|ai<>a’i},ift>tmaxthen Alice and Bobabort, • Alice andBobapply reconciliation (error-correction) and privacy amplification (PA) upon the qubits inK=I-T: PA:
Lo-Chau Quantum Key Distribution • Alice creates 2n EPR pairs in state each in state |b00>, and picks a random 2n bitstring b, • Alice randomly selects n EPR pairs T for checking Eve’s interference, • Alice performs H on the second qubit of each pair i such that bi=1, she sends the second qubit of each pair to Bob, • Bob receives them and announces it, • Alice announces b and T, • Bob applies H on the qubits where bi=1, • Alice and Bob measure their qubits in T in the Z basis, publicly share the result. If more than t errors occurred they abort, • Alice and Bob measure their remaining qubits according a check matrix for a predetermined [n,m]-CSS code correcting any t errors. They share the results, corrects and get m nearly perfect EPR pairs, • Alice and Bob measure the m EPR pairs in the Z basis to get a shared secret-key.
Family of CSS codes Remember that CSS codewords are defined as: Equivalently, we can define CSSu,v as follows: CSSu,v codes all work the same way than CSS codes.
CSSxz(C1,C2) is a basis • C1 is a [n,k1,t]-linear code, • C2 is a [n,k2]-linear code such that the dual of C2 corrects t errors. Assume H1 is the parity check for C1 and H2 is the parity check for C2*. We have seen that: • When A measures H1 she gets sx randomly in {0,1}n-k1, • When A measures H2 she gets sz randomly in {0,1}k2. • After error-correction and decoding they get:
Thm: If n out of 2n 2-qubit states are tested that way and less than t bit and phase flips were found then the number t’ of phase and bit flips for the untested positions is such that: Error-Rate Estimation Estimating the number of bit and phase flips:
A non-local test • Since Alice and Bob are physically separated, the previous • test cannot be performed. However, • Notice that the same result than before would be obtained • if for each position either bit flip or phase flip would be • tested but not both. • Observe also that: • which means that bit flips and phase flips can be detected • by applying both the Z or the X measurements and comparing • if they got different eigenvalues. • Notice that Alice and Bob by doing this make the detection of both bit-flip and phase-flip impossible on a single qubit.
Notice that using H on the second qubit of each pair at random randomizes the distribution of the errors: Thm: If n out of 2n 2-qubit states(in Lo-Chau) are tested for bit flips and t’ are detected then the number txand tz for phase and bit flips in the untested positions is such that: Bit-Flips and Phase-Flips It follows that the number of phase-flips and bit flips are distributed identically since H is applied randomly and Eve cannot find any information about when it is the case. Only measuring for bit-flips gives a bound on both the number phase-flips and bit-flips.
High Fidelity Implies Low Entropy Lemma 12.9: If <b00(n)|r|b00(n)> > 1-2-s, then S(r) < (2n+s+1/ln2)2-s+O(2-2s). Proof: It follows that S(r) <= S(rmax) where
Application to Lo-Chau Protocol • If the estimate for the number of errors is accurate and • is such that the QECC allows to fix them then Alice and Bob share m perfect EPR pairs, • Since the estimate is mistaken only with negligible • probability 2-an then the state shared by Alice and Bob is • such that <b00(n)|r|b00(n)> > 1-2-an, • By the Corollary to the Holevo bound, the amount of Shannon • information available to the Eavesdropper, about the • outcome of Alice’s and Bob’s measurements determining • the key, is negligible, • This is a secure Quantum Key distribution protocol!
Modified* Lo-Chau Protocol Alice creates n random check bits, and n EPR pairs in state |b00>. She encodes n qubits in state |0> or |1> according the check bits and picks a random 2n-bit string b, • Alice creates 2n EPR pairs each in state |b00>, and picks a random 2n bitstring b, • Alice randomly selects n EPR pairs T for checking Eve’s interference, • Alice performs H on the qubit to be sent for each i such that bi=1, she sends the qubits to Bob, • Bob receives them and announces it, • Alice announces b and T, • Bob applies H on the qubits where bi=1, • Alice and Bob measure their qubits in T in the Z basis, publicly share the result. If more than t-n errors occurred they abort, • Alice and Bob measure their remaining qubits according a check matrix for a predetermined [n,m]-CSS code correcting t errors. They share the results, correct and get m nearly perfect EPR pairs, • Alice and Bob measure the m EPR pairs in the Z basis to get a shared secret-key. Alice randomly picks n positions T to put the check qubits among n EPR pairs, Bob measures the check qubits in Z basis, publicly shares the result with Alice, if more than t-n errors occurred then they abort.
She could have done this here !! • Alice creates n random check bits, and n EPR pairs in state |b00>. She also encodes n qubits in state |0> or |1> according the check bits and picks a random 2n-bit string b, • Alice randomly picks n positions T to put the check qubits among n EPR pairs, • Alice performs H on the qubit to be sent for each i such that bi=1, she sends the qubits to Bob, • Bob receives them and announces it, • Alice announces b and T, • Bob applies H on the qubits where bi=1, • Bob measures the check qubits in {|0>,|1>} basis, publicly shares the result with Alice, if more than t-n errors occurred then they abort. • Alice and Bob measure their remaining qubits according the check matrix for a CSSx,z(C1,C2) where x and z are random. They share the results, correct the errors, decode and gets m perfect EPR pairs. • Alice and Bob measure the m EPR pairs in the Z basis to get a shared secret-key. The key is random and determined by Alice here The random CSS code is randomly selected by Alice when she measures.
Removing the Need for EPR Pairs • At step 8, Alice gets x and z randomly and uniformly since: • At step 9, Alice obtains a random m-bit sting k encoded in CSSxz(C1,C2) code: m=k1-k2 All those measurements commute with Eve and Bob actions. They could all occur at the very beginning!
Bob needs storing! CSS codes protocol • Alice creates n random check bits, and n EPR pairs in state |b00>. She also encodes n qubits in state |0> or |1> according the check bits and picks a random 2n-bit string b, • Alice randomly picks n positions T to put the check qubits among n EPR pairs, • Alice performs H on the qubit to be sent for each i such that bi=1, she sends the qubits to Bob, • Bob receives them and announces it, • Alice announces b and T, • Bob applies H on the qubits where bi=1, • Bob measures the check qubits in Z basis, publicly shares the result with Alice, if more than t-n errors occurred then they abort. • Alice and Bob measure their remaining qubits according the check matrix for a CSSx,z(C1,C2) where x and z are random. They share the results, correct the errors, decode and gets m perfect EPR pairs. • Alice and Bob measure the m EPR pairs in the Z basis to get a shared secret-key. Alice creates n random check bits, a random m bit key k, randomx and z. She encodes |k> in CSSxz(C1,C2). She also encodes n qubits in state |0> or |1> according the check bits and picks a random 2n-bit string b. Alice randomly chooses T and put the check qubits among the encoded|k>, Still needs quantum Computer!!! Alice announces x,z, b and T to Bob, Bob corrects and decodes the remaining qubits according the CSSxz(C1,C2) code, Bob measures the decoded qubits in basis Z and gets key k.
Alice sends the encoding: x is removed using Alice’s announcement Bob receives: Bob decodes for bitflips: Bob can recover k by measuring and identifying the coset: Removing the need for Quantum Computer z and correcting e2 are now useless!
But Alice does! CSS codes protocol • Alice creates n random check bits, a random m bit key k, randomx and z. She encodes |k> in CSSxz(C1,C2). She also encodes n qubits in state |0> or |1> according the check bits and picks a random 2n-bit string b. • Alice randomly chooses T and put the check qubits among the encoded|k>, • Alice performs H on the qubit to be sent for each i such that bi=1, she sends the qubits to Bob, • Bob receives them and announces it, • Alice announces x,z, b and T to Bob, • Bob applies H on the qubits where bi=1, • Bob measures the check qubits in {|0>,|1>} basis, publicly shares the result with Alice, if more than t-n errors occurred then they abort. • Bob corrects and decodes the remaining qubits according the CSSxz(C1,C2) code, • Bob measures the decoded qubits in basis Z and gets key k. Alice announces x, b and T to Bob, Bob measures the remaining qubits to get vk+w+x+e1 and subtracts x before correcting e1 to get vk+w, Bob computes the coset vk+w+C2=vk+C2 in order to get k. Bob doesn’t need to do quantum error-correction!
Removing Alice’s encoding Since Alice does not need to announce z, she sends a mixture: When w1+w2<>0 then half the z will produce -1 and half +1 This state is simpler to create than a CSS encoding: Alice classically chooses w in C2 at random, constructs |vk+w+x> as before using random x and k.
Alice creates n random check bits, a random x, a random vk in C1/C2, and a random w in C2. She encodes n qubits in state |0> or |1> according vk+w+x. She also encodes n qubits in state |0> or |1> according the check bits and picks a random 2n-bit string b. • Alice creates n random check bits, a random m bit key k, randomx and z. She encodes |k> in CSSxz(C1,C2). She also encodes n qubits in state |0> or |1> according the check bits and picks a random 2n-bit string b. • Alice randomly chooses T and put the check qubits among the encoded|k>, • Alice performs H on the qubit to be sent for each i such that bi=1, she sends the qubits to Bob, • Bob receives them and announces it, • Alice announces x, b and T to Bob, • Bob applies H on the qubits where bi=1, • Bob measures the check qubits in {|0>,|1>} basis, publicly shares the result with Alice, if more than t-n errors occurred then they abort. • Bob measures the remaining qubits to get vk+w+x+e1 and subtracts x before correcting e1 to get vk+w, • Bob computes the coset vk+w+C2=vk+C2 in order to get k. Alice randomly chooses T toput as check qubits among the encoded|vk+w+x>, No more quantum computer needed
Further Simplifications in C2 in C1/C2 in {0,1}n Alice sends: Bob gets : Alice announces: Bob subtracts : If Alice chooses vk in C1 then w becomes useless!!
Further Simplifications in C1 in {0,1}n Alice sends: Bob gets : Alice announces: Bob subtracts : Notice that vk+x is completely random, so Alice could choose x at random and send |x> with no change for the rest of the world.
Alice could prepare the qubits already in bases b! Almost BB84 • Alice creates n random check bits, a random x, a random vk in C1/C2, and a random w in C2. She encodes n qubits in state |0> or |1> according vk+w+x. She also encodes n qubits in state |0> or |1> according the check bits and picks a random 2n-bit string b. • Alice randomly chooses T and put the check qubits among the encoded|k>, • Alice performs H on the qubit to be sent for each i such that bi=1, she sends the qubits to Bob, • Bob receives them and announces it, • Alice announces x, b and T to Bob, • Bob applies H on the qubits where bi=1, • Bob measures the check qubits T in {|0>,|1>} basis, publicly shares the result with Alice, if more than t-n errors occurred then they abort. • Bob measures the remaining qubits to get vk+w+x+e1 and subtracts x before correcting e1 to get vk+w, • Bob computes the coset vk+w+C2=vk+C2 in order to get k. Alice chooses random vk in C1 and creates 2n qubits in states |0> and |1> according to 2n random bits. She also picks a random b in {0,1}2n, Alice randomly chooses n check positionsT while the others are |x>, Alice announces b, x-vk, and T to Bob, Bob measures the remaining qubits to get x+e, subtracts x-vk to get vk+ e, and corrects eaccording C1 to finally get vk, Aliceand Bob compute the coset vk+C2 in order to get k. Only quantum memory remains to be removed
Almost done • Alice could pick (4+)n random bits, for each she creates a qubit in basis |0>,|1> or |+>,|-> according b. • Upon reception, Bob could measure randomly in the X or Z basis. • When Alice announces b, they keep only the matching positions. • Only then, Alice chooses the check qubits.
Secure BB84 • Alice creates (4+n random bits, • For each bit, she creates a qubit in the Z or X basis according a • random b, • Alice sends the resulting qubits to Bob, • Alice chooses a random vk in C1, • Bob receives and publicly announces it. He measures each qubit in • random Z or X basis, • Alice announces b, • Alice and Bob only keep the qubits measured and sent in the same • basis. Alice randomly picks 2n of the remaining positions and picks • n for testing, • Alice and Bob publicly compared their check bits. If too many errors • occurred then they abort. Alice is left with |x> and Bob with |x+e>. • Alice announces x-vk. Bob subtracts this from his result and corrects • according C1 to obtain vk, • Alice and Bob compute the coset vk+C2 in C1 to obtain k.
Tolerable noise level for secure QKD Randomizing the positions of errors allows for correcting t errors with a code of minimum distance about t (with good prob).
QKD for Sale! Plug-and-play Quantum Key Distribution system that was designed for research and development applications. It is the ideal tool for researchers interested to contribute to the field of Quantum Cryptography. Link Encryptors are hardware Quantum Cryptography appliances for point-to-point wire-speed link encrpytion. Quantum Key Distribution and AES encryption engines are combined in a stand-alone unit. Vectis is a layer 2 encryption device that securely bridges two Fast Ethernet fiber optic networks.