Wireless Security: Unveiling 802.11 Risks and Solutions
Learn about the risks in wireless security with 802.11 technologies and discover effective solutions. Explore common threats like misconfigurations, insertion attacks, and interception. Get insights on protective measures and tools to enhance your wireless network's security.

Wireless Security: Unveiling 802.11 Risks and Solutions
E N D
Presentation Transcript
Wireless (in)Security Or Everything You Wanted to Know about Wireless but Were Afraid to Ask
Introduction to 802.11 • At present there are three wireless LAN technologies in common use today: 802.11b, 802.11a, and 802.11g. • Wireless LAN devices consist of wireless cards that fit into computers and access points. An AP (access point also known as a AP) is the wireless server that connects clients to the internal network. AP’s typically act as a bridge for the clients.
Introduction to 802.11 • The 802.11 client cards for PDA’s, laptops, and desktops are approximately under $19US. • Because of the inexpensive price, within many companies employees can purchase wireless equipment without approval and deploy this in a rogue fashion. • The same security issues apply to home networks, corporate networks, and telecommuters that are using wireless.
Introduction to 802.11 • Airports, hotels, coffee shops like Starbucks, and even McDonald’s are deploying 802.11 networks.
War Driving etc. • Taken from the movie, "WarGames", dialing many phone numbers looking for computers to access was called "War-Dialing". • This similar action has been applied to wireless. • WiFi War-chalking Symbols are at http://www.warchalking.org .
802.11 Risks • Denial of Service • Insertion Attacks • Interception and monitoring wireless traffic • Misconfiguration
Denial of Service • 802.11b and 802.11g devices are subject to interference from other sources transmitting at the same frequency such as digital cordless telephones and microwaves. • A more sophisticated attack involves forcing clients to diassociate.
Insertion Attacks • Plugging in unauthorized clients • Plugging in unauthorized rogue access points
Insertion and Monitoring Wireless Traffic • Wireless Sniffer • An intruder who monitors the wireless network can apply this same attack principle on the wireless as on a wired network. • Highjacking the Session • If an attacker can sniff the wireless traffic, it is possible to inject false traffic into a connection.
Insertion and Monitoring Wireless Networks • Broadcast monitoring • If an AP is connected to a hub rather than a switch, any network traffic across that hub can be potentially broadcasted out over the wireless network. • Evil Twin • This is the wireless equivalent of the “bait and switch” scam.
Misconfiguration • The SSID • The SSID (Server Set ID) is a configurable identification that allows clients to communicate to the appropriate AP. • Clients that are configured with the same SSID can communicate with AP’s having the same SSID.
Misconfiguration • The SSID • Some default SSID’s • “tsunami” - Cisco • “101” – 3Com • “RoamAbout Default Network Name” - Lucent/Cabletron • “Default SSID" • “Compaq” - Compaq • “WLAN” – Addtron, a popular AP • “intel” - Intel • “linksys” – Linksys • “Wireless”
Misconfiguration • WEP (Wired Equivalent Privacy) • WEP can be typically configured in 3 possible modes: • No encryption mode • 40 bit encryption • 128 bit encryption • WEP, by default out of the box, is turned off. 64 bit encryption versus 128 bit encryption provides no added protection against the known flaw in WEP.
Misconfiguration Papers on WEP Insecurities • Researchers at Berkeley have documented these findings at: • http://www.isaac.cs.berkeley.edu/isaac/wep-faq.html • Using the Fluhrer, Mantin, and Shamir Attack to Break WEP • http://www.cs.rice.edu/~astubble/wep/wep_attack.html
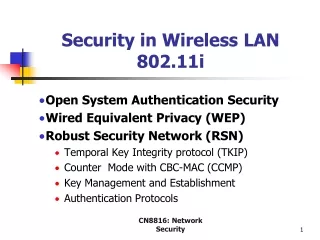
Misconfiguration • WEP (Wired Equivalent Privacy) • Using WEP is better than not using it. • It at least stops casual sniffers. • Far off on the horizon is 802.11i which will bring robust and secure authentication to networks. • In the meantime, the Wi-Fi Alliance has come up with WPA (Wi-Fi Protected Access).
Misconfiguration • WEP Keys • The NetGear Access Point uses the following 4 WEP sequences as default keys. • 10 11 12 13 14 • 21 22 23 24 25 • 31 32 33 34 35 • 41 42 43 44 45 • It is highly recommended not to use the default WEP keys.
Misconfiguration • SNMP (Simple Network Management Protocol) • Many wireless AP’s have SNMP (Simple Network Management Protocol) agents running. If the community word is not properly configured, an intruder can read and potentially write sensitive information and data on the AP. If SNMP agents are enabled on the wireless clients, the same risk applies to them as well.
War Driving, War Walking • Here are some popular places to upload War Driving AP maps. • http://www.netstumbler.com. • http://www.wigle.net • http://www.wifimaps.com
802.11 Security Tools • Airsnort - http://freshmeat.net/projects/airsnort/ • Wepcrack - http://sourceforge.net/projects/wepcrack • Netstumbler - http://www.netstumbler.com/ • Kismet - http://www.kismetwireless.net/
What Can You Do About Wireless Security • Follow secure file-sharing practices. • Enable WEP encryption • Use non-obvious WEP keys and periodically change them. • Secure your wireless router / Access Point (AP). • Disallow router/ AP administration via wireless.
What Can You Do About Wireless Security • Use MAC address based Access and Association control. • Don’t broadcast the SSID. • Don’t put AP’s next to exterior walls. • Add the extra security of RADIUS. • If you can get away with it, don’t use DHCP.
What Can You Do About Wireless Security • While you’re at it, change the subnet. • Avoid 64 bit WEP! • Avoid equipment that can’t be upgraded. • Hunt down rogue access points. • Determine where the broadcast perimeter of the wireless network ends. • Use a VPN (Virtual Private Network).
Conclusion • You can implement as much or as little security as you want to on your wireless network. There is no one single thing you can do to make your wireless LAN secure. Fortunately, there are a lot of things that can be done to make an essentially insecure medium into a more secure medium suitable for many uses beyond mere hobbyist tinkering.