Web Security Common security threats and hacking
Web Security Common security threats and hacking . Nahidul Kibria Co-Leader, OWASP Bangladesh , Senior Software Engineer, KAZ Software Ltd. Twitter:@nahidupa. Writing code for fun and food. And security enthusiastic. Shahee Mirza # Certified Ethical Hacker (C|EH).

Web Security Common security threats and hacking
E N D
Presentation Transcript
NahidulKibria Co-Leader, OWASP Bangladesh,Senior Software Engineer, KAZ Software Ltd. Twitter:@nahidupa Writing code for fun and food. And security enthusiastic
Shahee Mirza # Certified Ethical Hacker (C|EH). # Microsoft® Certified Systems Administrator. #Information Security Consultant, Nexus IT Zone. http://www.shaheemirza.com FB:shaheemirzaTwitter: @shaheemirza
Most sites are not secure! • Attacker can access unauthorized data! • They use your web site to attack your users!
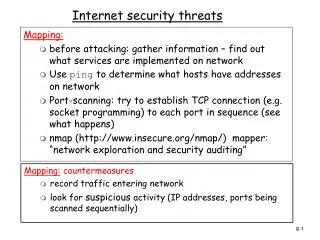
Historically the web wasn’t designed to be secure • Built for static, read only pages • Almost no intrinsic security • A few security features were “bolted-on” later
What does that mean? • Cookie based sessions can be hijacked • No separation of logic and data • All client supplied data cannot be trusted
The vast majority of web applications have serious security vulnerabilities! Most developers not aware of the issues.
Web Application threat surface XSS XML Injection Parameter tempering /sniffing Click jacking Directory Traversal CSRF SQL Injection DIRECT OBJECT REFERENCE FORGED TOKEN
Ajax Flash Silverlight Applets The attack surface is growing!
Study: Global cybercrime costs more than illegal drugs http://www.dnaindia.com/mumbai/report_cyber-crime-costs-india-rs34110-crore-per-year_1588917 Global drug trade—about $288 billion INSECURE-Mag-31
Common question is I’m inocent why should I will be target? I don’t have any sensitive data. I’m not even serve any important data. I have no enemy
Answer is • You have resource... • May be a Multi-core processor...Bandwidth • Attacker weaponize your pc to attack other or use you resource ... Turn your pc to zombie
About OWASP • OWASP’s mission is “to make application security visible, so that people and organizations can make informed decisions about true application” Attacker not use black art to exploit your application
OWASP Bangladesh Chapter Bangladeshi community of Security professional Globally recognized Open for all Free for all What do we have to offer? Monthly Meetings Mailing List Presentations & Groups Open Forums for Discussion Vendor Neutral Environments
OWASP Top 10 Web Application Security Risks (2010 Edition) http://www.owasp.org/index.php/Top_10
Application Developers • New attacks/ defense guideline • Cheat Sheets • Web Goat-emulator-designed to teach • web application security lessons
Existing Enterprise Security Services/Libraries The OWASP Enterprise Security API
Application Testers and Quality Assurance Tools Testing guide/pentester Application Security Verification Standard Project
Application Project Management and Staff Define the process SDLC Code Review
OWASP Code Review Project Code review tool http://codecrawler.codeplex.com/Release/ProjectReleases.aspx http://orizon.sourceforge.net
OWASP Testing Framework • 4.2 Information Gathering • 4.3 Configuration Management Testing • 4.4 Business logic testing • 4.5 Authentication Testing • 4.6 Authorization Testing • 4.7 Session Management Testing • 4.8 Data Validation Testing • 4.9 Testing for Denial of Service • 4.10 Web Services Testing • 4.11 Ajax Testing http://www.owasp.org/index.php/OWASP_Testing_Guide_v3_Table_of_Contents
Myth- “The developer will provide me with a secure solution without me asking”
Download Get OWASP Books
Coolest Jobs in Information Security #1 Information Security Crime Investigator/Forensics Expert #2 System, Network, and/or Web Penetration Tester #3 Forensic Analyst #4 Incident Responder #5 Security Architect #6 Malware Analyst #7 Network Security Engineer #8 Security Analyst #9 Computer Crime Investigator #10 CISO/ISO or Director of Security #11 Application Penetration Tester #12 Security Operations Center Analyst #13 Prosecutor Specializing in Information Security Crime #14 Technical Director and Deputy CISO #15 Intrusion Analyst #16 Vulnerability Researcher/ Exploit Developer #17 Security Auditor #18 Security-savvy Software Developer #19 Security Maven in an Application Developer Organization #20 Disaster Recovery/Business Continuity Analyst/Manager
Subscribe mailing list https://www.owasp.org/index.php/Bangladesh https://www.facebook.com/OWASP.Bangladesh Keep up to date! Twitter:@nahidupa Twitter:@owaspbangladesh