Public Key Cryptography
Public Key Cryptography. July 2011. Topics. Symmetric and Asymmetric Cryptography Public Key Cryptography Digital Signatures Digital Certificates. The briefcase example with shared key. Private-Key Cryptography. Traditional private/secret cryptography uses one key

Public Key Cryptography
E N D
Presentation Transcript
Public Key Cryptography July 2011
Topics • Symmetric and Asymmetric Cryptography • Public Key Cryptography • Digital Signatures • Digital Certificates
Private-Key Cryptography • Traditional private/secret cryptography uses one key • Shared by both sender and receiver • If this key is disclosed, communications are compromised • Symmetric : keys used in parties are equal • No protection of sender from receiver forging a message & claiming is sent by sender
Symmetric Key Cryptography Plain-text input Plain-text output Cipher-text “The quick brown fox jumps over the lazy dog” “The quick brown fox jumps over the lazy dog” “AxCv;5bmEseTfid3)fGsmWe#4^,sdgfMwir3:dkJeTsY8R\s@!q3%” Encryption Decryption Same key(shared secret)
Symmetric Pros and Cons • Strength: • Simple and really very fast (order of 1000 to 10000 faster than asymmetric mechanisms) • Super-fast (and somewhat more secure) if done in hardware (3DES, Rijndael) • Weakness: • Must agree the key beforehand • Securely pass the key to the other party
Key Distribution Problem • In symmetric key cryptosystems • Over complete graph with n nodes, nC2 = n(n-1)/2 pairs secret keys are required. • Example: n=100, 99 x 50 = 4,950 keys are required • Problem: Managing large number of keys and keeping them in a secure manneris difficult a Secret keys are required between (a,b), (a,c), (a,d), (a,e), (b,c), (b,d), (b,e), (c,d), (c,e), (d,e) e b c d
The briefcase example with unshared key • The briefcase has to be sent back and forward three times, which seems pretty inefficient.
Desirable properties Use briefcase example to come up with a specification that are desirable for any cipher system that is to be used between two entities who do not already share a symmetric key.
Topics • Symmetric and Asymmetric Cryptography • Public Key Cryptography • Digital Signatures • Digital Certificates
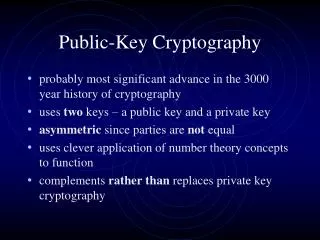
Public-Key Cryptography • Probably most significant advance in the history of cryptography • Uses two keys – a public & a private key • One for encryption and another one for decryption • Knowledge of the encryption key doesn’t give knowledge of the decryption key • Asymmetric since parties are not equal • Uses number theoretic concepts to function • Complements rather than replaces private key crypto
Public-Key Cryptography issues • Developed to address two key issues: • key distribution – how to have secure communications in general without having to trust a KDC with your key • digital signatures – how to verify a message comes intact from the claimed sender
The Two Keys Alice Bob Charlie • Each party has two keys Alice’s Private key Alice’sPublic key Bob’s Private key Bob’sPublic key Charlie’s Private key Charlie’sPublic key
Main uses of Each Key • A public-key • Public to anybody • used to encrypt messages and verify signatures • A private-key • known only to the owner • used to decrypt messages, and sign (create) signatures
How does 2 different keys work? • Just an very simple example: • Public Key = 4, Private Key = 1/4, message M = 5 • Encryption: • Ciphertext C = M * Public Key • 5 * 4 = 20 • Decryption: • Plaintext M = C * Private Key • 20 * ¼ = 5
An Example: Internet Commerce • Bob wants to use his credit card to buy some brownies from Alice over the Internet. • Alice sends her public key to Bob. • Bob uses this key to encrypt his credit-card number and sends the encrypted number to Alice. • Alice uses her private key to decrypt this message (and get Bob’s credit-card number).
private public Public Key Encryption Clear-text Input Clear-text Output Cipher-text “The quick brown fox jumps over the lazy dog” “The quick brown fox jumps over the lazy dog” “Py75c%bn&*)9|fDe^bDFaq#xzjFr@g5=&nmdFg$5knvMd’rkvegMs” Encryption Decryption Different keys Recipient’s private key Recipient’s public key
Hybrid Encryption Systems • All known public key encryption algorithms are much slower than the fastest secret-key algorithms. • In a hybrid system, Alice uses Bob’s public key to send him a secret shared session key. • Alice and Bob use the session key to exchange information.
Topics • Symmetric and Asymmetric Cryptography • Public Key Cryptography • Digital Signatures • Digital Certificates
A Digital Signature • Digital data that carries the intent of a signature related to a digital document • Use to demonstrate the authenticity of a digital message or document • A valid digital signature gives a recipient reason to believe that the message was created by a known sender, and that it was not altered in transit
priv SignedDocument Sender: Creating a Digital Signature Message or File Message Digest Digital Signature This is the document created by Charlotte This is the document created by Charlotte (Typically 128 bits) 3kJfgf*£$& Py75c%bn 3kJfgf*£$& RSA SHA, MD5 Asymmetric Encryption Generate Hash Calculate a short message digest from even a long input using a one-way message digest function (hash) Charlotte’s private key
Message Digest Generate Hash Py75c%bn Equal?? DigitalSignature Asymmetric Decryption This is the document created by Charlotte Py75c%bn pub 3kJfgf*£$& Charlotte's public key(from certificate) SignedDocument Receiver: Verifying a Digital Signature RSA
Topics • Symmetric and Asymmetric Cryptography • Public Key Cryptography • Digital Signatures • Digital Certificates
Can be a person or a computer or a device.. pub What is a Certificate ? • The simplest certificate just contains: • A public key • Information about the entity that is being certified to own that public key • … and the whole is • Digitally signed by someone trusted (like your friend or a CA) 2wsR46%frdEWWrswe(*^$G*^%#%#%DvtrsdFDfd3%.6,7 This public key belongs to Charlotte 3kJfgf*£$&4dser4@358g6*gd7dT DigitalSignature Certificate
X.500 Subject Public Key X.500 issuer Expiration date Serial Number Extensions Info CA Digital Signature Certificate X.509 Certificate Who is the owner, CN=Charlotte,O=CERN,C=CH The public key or info about it Who is signing, O=CERN,C=CH See later why expiration date is important Additional arbitrary information … of the issuer, of course
Elements of Digital Cert. • A Digital ID typically contains the following information: • Your public key, Your name and email address • Expiration date of the public key, Name of the CA who issued your Digital ID
Public key Public key Public key This public key belongs to BigRoot This public key belongs to CERN This public key belongs to Charlotte Check DS of CERN Check DS ofFoobar Issued by: BigRoot Issued by: BigRoot Issued by: CERN CERN Digital Signature BigRoot Digital Signature` BigRoot Digital Signature Certificate Certificate Certificate Certificate Validation • Essentially, this is just checking the digital signature • But you may have to “walk the path” of all subordinate authorities until you reach the root • Unless you explicitly trust a subordinate CA “In BigRoot We Trust” (installed root CA certificate)