Network Security Essentials: Protecting Your Digital Perimeter
Cyber threats are constantly evolvingu2014your network security shouldnu2019t fall behind. CodeGuardianu2019s Network Security Essentials safeguard your digital perimeter with real-time monitoring, threat detection, and advanced firewall protection. Stay ahead of breaches, protect sensitive data, and ensure business continuity. Secure your network today with CodeGuardianu2019s trusted security solutions.

Network Security Essentials: Protecting Your Digital Perimeter
E N D
Presentation Transcript
Network Security Protecting Your Digital Assets
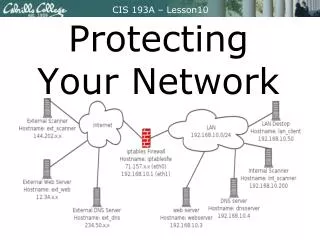
Introduction to Network Security Protecting Digital Assets Network security safeguards against unauthorized access, use, disclosure, disruption, modification, or destruction of information. Cyber Threats and Attacks Cybersecurity threats include malware, phishing, denial- of-service attacks, and data breaches.
Common Network Security Threats Malware Phishing Viruses, worms, Trojans, ransomware, Deceptive emails or websites can and spyware can damage systems and trick users into revealing sensitive steal data. information. Data Breaches Denial-of-Service Attacks Unauthorized access to sensitive data These attacks overwhelm a network or can lead to financial loss, identity theft, server, making it unavailable to legitimate and reputation damage. users.
Firewalls and Access Control Firewalls Act as a barrier between a network and the outside world, blocking unauthorized traffic. Access Control Restricts access to specific resources based on user identity and permissions. Authentication Verifies the identity of users and devices before granting access to the network. Authorization Determines what actions users are allowed to perform once they are authenticated.
Incident Response and Disaster Recovery Incident Response Plan Recovery and Mitigation A documented process for handling Restores affected systems and security incidents. data and implements measures to prevent future incidents. Incident Analysis and Containment Identifies the cause and scope of an incident and takes steps to contain it.
Best Practices for Network Security Strong Passwords Use complex and unique passwords for all accounts. Regular Updates and Patches Keep software up to date with the latest security patches. Employee Training Educate employees about security risks and best practices. Multi-Factor Authentication Use multiple methods of authentication for critical accounts.
THANK YOU FOR YOUR ATTENTION www.codeguardian.ai +918826499999