Phishing with Worms
150 likes | 306 Views
Twenty Years of Digital Threats—What Have We Learned and Where Are We Now?. Phishing with Worms. The worst and the worser. WORMS. Is it a worm, virus, or trojan?. Malware is a general term. Trojans hide as another program. Trojan disguises itself as another program with value.

Phishing with Worms
E N D
Presentation Transcript
Twenty Years of Digital Threats—What Have We Learned and Where Are We Now? Phishing with Worms
The worst and the worser WORMS
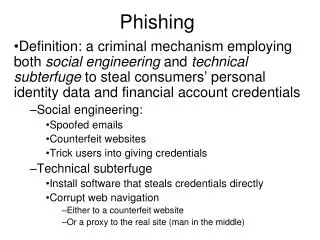
Is it a worm, virus, or trojan? • Malware is a general term. • Trojans hide as another program. • Trojan disguises itself as another program with value. • Might disguise itself as a free tool for editing photos. • Virus hides within another program. • Infected program may or may not still operate after the attack. • Worms hide without disguise. • Worm is the entity. • It self-installs.
Back “in the day” • Worms travelled by floppy. • Transmission rates were slow. • Still some worms became widespread.
Worm infected machines assemble themselves into collective “botnets” capable of sending spam, and crunching passwords. Assimulation
The Collectives Botnet Collective Spam rate Name Machines (billions/day) Conficker 20 million 10 Kraken 500,000 9 Srizbi 450,000 60 Bobax 185,000 9 Rustock 150,000 30 Cutwail 125,000 16 Storm 85,000 (peak 1.5 million) 3
What to do with a botnet Spam engine Password/Encryption hacking Bank fraud, identity theft Criminal computing enterprises Decentralized computing Huge bandwidth potential More computing cycles than top ten mainframes
Storm botnet Evades tracking, morphs Takes defensive measures – known to launch denial of service attack against suspected investigators Summer of 2007, Storm forces Estonia “off the web.” Key servers for the baltic nation moved offline for extended period included government, banking, media, and police sites. Once involved 1.5 million computers
Conficker : new guy on the block Date Estimated Infections Dec 1, 2008 500,000 Dec 2, 2008 less than million Dec 4, 2008 1.2 million Dec 5, 2008 3.5 million ................................ Jan 17, 2009 9 million Jan 23, 2009 10 million Jan 26, 2009 15 million
Conficker Payload Delivery • FlashDrive • Auto run • Default action • Autorun / AutoPlay • Hard to turn off • Registry editing • Network • Password guessing • Weak passwords
Microsoft's Part • Announced a fix in October • Apparently not everyone installed the update • Malicious Software Removal Tool • Worm may block • access to MS Update • antivirus from updates • Windows Defender or turn it off
What does the worm do? We don't know It seems to be waiting for orders
What can you do? • Update Windows Regularly • Apply MS08-067 • Disable Autoplay / AutoRun • Run the Malicious Software Removal tool available from www.update.microsoft.com
You might have conficker if ... You cannot connect to websites or online services that contain the following strings:virus spyware malware rootkit defender microsoft symantec norton mcafee trendmicro sophos panda etrust networkassociates computerassociates f-secure kaspersky jotti f-prot nod32 eset grisoft drweb centralcommand ahnlab esafe avast avira quickheal comodo clamav ewido fortinet gdata hacksoft hauri ikarus k7computing norman pctools prevx rising securecomputing sunbelt emsisoft arcabit cpsecure spamhaus castlecops threatexpert wilderssecurity windowsupdate
You might have conficker if ... The following services are disabled or fail to run: • Windows Security Center Service • Windows Update Auto Update Service • Background Intelligence Transfer Service • Windows Defender • Error Reporting Service • Windows Error Reporting Service