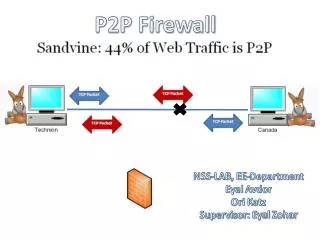
P2P Firewall Detection and Spoofed Reset Packet Analysis
DESCRIPTION
This report discusses the findings from the NSS-LAB's research on P2P traffic detection. Under the supervision of Eyal Zohar, Eyal Avdor and Ori Katz analyzed how firewalls generate reset packets in response to detected P2P traffic. The study highlights the implications of spoofed reset packets sent to both endpoints, which leads to unexpected connection terminations. This work aims to enhance understanding of P2P interactions in network environments and improve firewall strategies to handle such traffic effectively.
1 / 2
Download Presentation 

P2P Firewall Detection and Spoofed Reset Packet Analysis
An Image/Link below is provided (as is) to download presentation
Download Policy: Content on the Website is provided to you AS IS for your information and personal use and may not be sold / licensed / shared on other websites without getting consent from its author.
Content is provided to you AS IS for your information and personal use only.
Download presentation by click this link.
While downloading, if for some reason you are not able to download a presentation, the publisher may have deleted the file from their server.
During download, if you can't get a presentation, the file might be deleted by the publisher.
E N D
Presentation Transcript
P2P Firewall NSS-LAB, EE-Department EyalAvdor Ori Katz Supervisor: EyalZohar
detected P2P traffic reset packets generated by the firewall Spoofed Reset packets sent to both sides leading to connection termination
More Related