Joint Energy and Information Transfer: Optimizing Coding Strategies for Enhanced Performance
E N D
Presentation Transcript
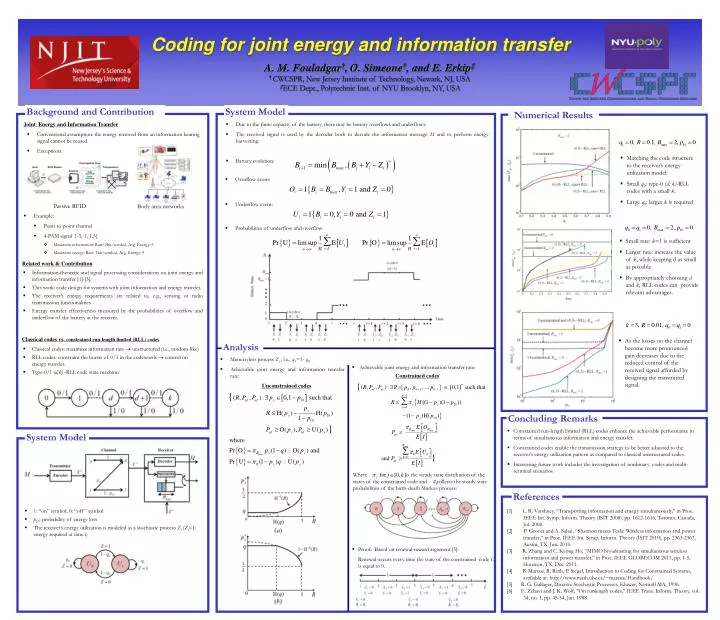
Coding for joint energy and information transfer A. M. Fouladgar†,O. Simeone†, and E. Erkip‡ † CWCSPR, New Jersey Institute of Technology, Newark, NJ, USA ‡ECE Dept., Polytechnic Inst. of NYU Brooklyn, NY, USA Background and Contribution System Model Numerical Results Joint Energy and Information Transfer • Due to the finite capacity of the battery, there may be battery overflows and underflows. • The received signal is used by the decoder both to decode the information message M and to perform energy harvesting. • Battery evolution: • Conventional assumption: the energy received from an information bearing signal cannot be reused. • Exceptions: • Matching the code structure to the receiver’s energy utilization model: • Small q0: type-0 (d; k)-RLL codes with a small k. • Large q0: larger k is required • Overflow event: • Underflow event: Passive RFID • Body area networks • Example: • Point-to-point channel • 4-PAM signal {-3,-1, 1,3} • Maximum information: Rate: 2bit/symbol, Avg. Energy: 5 • Maximum energy: Rate: 1bit/symbol, Avg. Energy: 9 • Probabilities of underflow and overflow: • Small rate: k=1 is sufficient • Larger rate: increase the value of k, while keeping d as small as possible • By appropriately choosing d and k, RLL codes can provide relevant advantages. Related work & Contribution • Information-theoretic and signal processing considerations on joint energy and information transfer [1]-[3]. • This work: code design for systems with joint information and energy transfer. • The receiver’s energy requirements are related to, e.g., sensing or radio transmission functionalities. • Energy transfer effectiveness measured by the probabilities of overflow and underflow of the battery at the receiver. Classical codes vs. constrained run-length limited (RLL) codes • As the losses on the channel become more pronounced gain decreases due to the reduced control of the received signal afforded by designing the transmitted signal. Analysis • Classical codes: maximize information rate unstructured (i.e., random-like) • RLL codes: constraint the bursts of 0/1 in the codewords control on energy transfer. • Type-0/1 (d,k) -RLL code state machine: • Memoryless process Zi , i.e., q1=1- q0 • Achievable joint energy and information transfer rate: • Achievable joint energy and information transfer rate: Constrained codes Unconstrained codes Concluding Remarks • Constrained run-length limited (RLL) codes enhance the achievable performance in terms of simultaneous information and energy transfer. • Constrained codes enable the transmission strategy to be better adjusted to the receiver’s energy utilization pattern as compared to classical unstructured codes. • Interesting future work includes the investigation of nonbinary codes and multi-terminal scenarios System Model • Where is the steady state distribution of the states of the constrained code and collects the steady state probabilities of the birth-death Markov process: References • 1: “on” symbol; 0: “off” symbol • p10: probability of energy loss • The receiver’s energy utilization is modeled as a stochastic process Zi (Zi=1: energy required at time i) [1] L. R. Varshney, “Transporting information and energy simultaneously,” in Proc. IEEE Int. Symp. Inform. Theory (ISIT 2008), pp. 1612-1616, Toronto, Canada, Jul. 2008. [2] P. Grover and A. Sahai, “Shannon meets Tesla: Wireless information and power transfer,” in Proc. IEEE Int. Symp. Inform. Theory (ISIT 2010), pp. 2363-2367, Austin, TX, Jun. 2010. [3] R. Zhang and C. Keong Ho, “MIMO broadcasting for simultaneous wireless information and power transfer,” in Proc. IEEE GLOBECOM 2011, pp. 1-5, Houston, TX, Dec. 2011. [4] B. Marcus, R. Roth, P. Siegel, Introduction to Coding for Constrained Systems, available at: http://www.math.ubc.ca/~marcus/Handbook/ [5] R. G. Gallager, Discrete Stochastic Processes, Kluwer, Norwell MA, 1996. [6] E. Zehavi and J. K. Wolf, "On runlength codes," IEEE Trans. Inform. Theory, vol. 34, no. 1, pp. 45-54, Jan. 1988. • Proof: Based on renewal-reward argument [5]: • Renewal occurs every time the state of the constrained code Ci is equal to 0.