Comparative Analysis of Encrypted Number Mapping in Privacy-Preserving Auctions
130 likes | 156 Views
Detailed discussion on Conditional Encrypted Mapping (CEM), encrypted number comparisons, and CEM applications in auctions for privacy protection and secure data transfer. Includes algorithms, related works, and tools like homomorphic encryption.

Comparative Analysis of Encrypted Number Mapping in Privacy-Preserving Auctions
E N D
Presentation Transcript
Conditional Encrypted Mapping andComparing Encrypted Numbers Vladimir Kolesnikov Joint work with Ian F. Blake University of Toronto
Privacy in Auctions Note to self: spam Austin with $999 tickets offers I am selling a ticket to Anguilla. $1000 One hundred million dollars! Sorry Deal!
Comparing Encrypted Numbers I have no idea what the bids were Enc($100000000) Enc($1000) Enc(0) Enc(1) I lost I won What if bidders lie about the result?
Conditional Encrypted Mapping (CEM) Prepare two secrets: s1 – signed contract s0– loser notification Enc($100000000) Enc($1000) Enc(s0) Enc(s1) s0 s1
Q-CEM s0, s1 Q(x,y) m=Rmap(s0, s1, e0, e1, pk) e0 = Enc(x) e1 = Enc(y) m ? ? Rec(m, sk) = sQ(x,y) Pair (Rmap, Rec) for Q is a Q-CEM
Definitional Choices CEM: Rmap(s0, s1, e0, e1, pk), Rec(m, sk) • Strong notion of privacy • Output of Rmap contains no statistical information other than the value sQ(x,y) • Strong composability • Holds for all generated key pairs, valid inputs and randomness used in encryption • E.g. Adv does not benefit from maliciously • choosing randomness when encrypting inputs
Definitional Choices CEM: Rmap(s0, s1, e0, e1, pk), Rec(m, sk) • Do not specify security requirements of the • encryption scheme • One definition is useable in most settings • Delay discussion of easy but tedious details (e.g. what if inputs contain decryption keys) • Q-CEM with semantically secure encryption gives a protocol in the semi-honest model • can be modified to withstand malicious players (ZK or the light-weight CDS)
Some of Related Work • Auctions and GT • Naor, Pinkas, Sumner 1999 • Di Crescenzo 2000 • Fischlin 2001 • Laur, Lipmaa 2005 • Many others • CEM • Conditional Oblivious Transfer and variants • Di Crescenzo, Ostrovsky, Rajagopalan 1999 • Gertner, Ishai, Kushilevitz, Malkin 1998 • Aiello, Ishai, Reingold 2001 • Di Crescenzo 2000 • Laur Lipmaa 2005
Tools – Homomorphic Encryption Encryption scheme, such that: Given E(m1), E(m2) and public key, allows to compute E(m1 m2) We will need: • Additively homomorphic ( = +) schemes • Large plaintext group The Paillier scheme satisfies our requirements Can compute E(cm1 + m2) from c, E(m1), E(m2)
The GT-CEM Construction y1, …, yn x1-y1, …, xn-yn :0 = 0, i = rii-1+di 1 -1 1 -1 1 -1 d = 0 0 0 0 0… 1 -1 = 0 0 0 t1 t2 t3 t4 t5… s0, s1 x y x1, …, xn d = Linear Map 0 R -1 s01 s1 0 R -1 ES01 ES1 • ESi is a randomized encoding of si • contains no other information
Randomized Mapping Given s0, s1 f(-1) = b-a = ES0 (1) f(1) = a+b = ES1 (2) f(0) = b = ½ (ES0 + ES1) ES0, ES1, f(x) = ax + b Assume s0, s1 contain redundancy Choose R 2R ZN. View R as blocks r0, r1: R = r0 2k + r1 r0 r0 s0 r1 s0 _ _ _ _ _ _. _ _ _ _ _ _ _ _ _ _ _. _ _ _ _ _ ES0 = ES1 = s1 r1 r1 r0 s1 _ _ _ _ _ _. _ _ _ _ _ _ _ _ _ _ _. _ _ _ _ _ c=0 c=1 c 2R {0,1} • Set f = ax+b to satisfy (1),(2) • f(-1), f(1) contain s0, s1 and no extra information* • f(0) = ½ (ES0 + ES1) = ½ (s0 2k + r1 + r0 2k + s1) = • ½ (R + … ) = R’
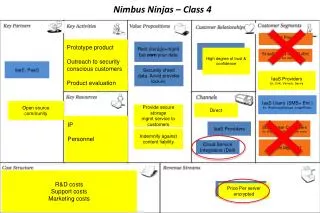
Resource Comparison Orders of magnitude improvement over GM-based schemes Performance similar to previous Paillier-based COT schemes • c-bit secrets are transferred based on comparison of n-bit numbers. • and are the correctness and security parameter
Conclusions • General and convenient definition of CEM • CEM for any NC1 predicate • GT-CEM Constructions • Simple and composable • Especially efficient for transferring larger secrets ( e.g. ¼500-1000 bits ) • Applications to auctions, etc