Virtualization in Software Engineering
Explore the concept of virtualization in software engineering, including its benefits, implementation methods, and various use cases in development, testing, and system optimization.

Virtualization in Software Engineering
E N D
Presentation Transcript
Virtualization in Software Engineering Dennis Kalinowski 4/30/2007
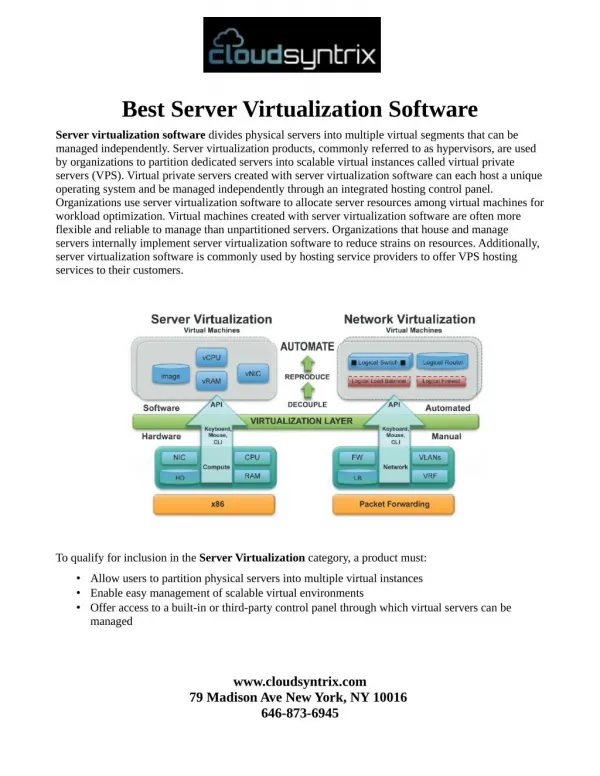
What is Virtualization? Abstraction of computer resources Servers, operating systems, applications, or storage devices Technique for hiding characteristics from other systems, applications, or users Used to provide different interfaces or resources Can be used to make a physical resource appear as multiple logical resources Or multiple physical resources appear as a single logical resource
Why Use Virtualization? Improve portability, security, performance, reliability Can be used in design, implementation, testing, or deployment of systems
Old Idea, Innovative Uses Early 1970s, IBM 370 mainframe used virtualization to run multiple operating systems Each operating system operated as if it had exclusive control of the hardware Some hardware implement virtualization Intel's Hyper-Threading Technology Single physical processor appears as multiple logical processors Automatic parallelization Two or more physical processors exposed as a single logical processor Executes multiple instructions from the current thread
Hardware Virtualization • Virtual Machine Monitor (VMM) – aka hypervisor • Allocates system resources for each virtualized operating system or program • Layer between software and other resources (such as hardware) • Either sits directly on hardware or runs within an operating system
Hardware Virtualization • When run within an operating system... • Host OS controls hardware • Guest OS runs in the virtualized environment • Three types: • emulation/simulation – simulates complete hardware. (Can host an unmodified OS for the same or different CPU) • native virtualization – simulates enough hardware so the guest is in isolation. (Only allows unmodified OS for the same CPU) • paravirtualization – provides an API which must be used by the guest OS.
Hardware Virtualization Guest OS can be altered or observed during execution States of system can be snapshotted Other examples of hardware virtualization Storage devices File systems Accessing disk images as if they were an actual drive Virtual memory
Example 1 Usage of a VMM Image from: [16] Intel virtualization technology.
Advantages of HV Portability Software would not need to be rewritten for new hardware, only the virtualization layer needs to be altered Security Isolated environment to restrict spread of intrusion Guest OS can be monitored to observe for calls or behavior that may indicate intrusion
Advantages of HV Performance IBM 370 mainframe ran OS's that did not support threading in parallel with OS's that did Therefore, less CPU cycles were wasted Virtualization may be used to maximize utilization of resources Possible issue: overhead Loading a previous snapshot may be faster than a fresh load Reliability Recovery – On failure or lose, an image of system's pristine or last good state can be reloaded Redundancy – Identical resources or software run in parallel Hardware example: fault tolerant CPU Software example: share load two identical servers
Example 2 Performance Image from: [15] Performance Evaluation on Server Consolidation Using Virtual Machines.
Example 3 Reliability Image from: [9] High performance fault tolerant computer and its fault recovery. Virtualization hides the true underlying system from the running program
Example 3 Reliability Image from: [9] High performance fault tolerant computer and its fault recovery.
Use in Software Development Virtualize hardware and/or software environments Increase portability of software by testing in various operating systems, architectures, or configuration By isolating build/testing environments to virtual systems, you do not risk contaminating your own development system Keep testing environments consistent or configured with minimal software dependencies Cheaper to run multiple virtual machines than multiple physical computers
Use in Software Development Testing Can observe or alter software running in virtual environment So, ideal for debugging OS kernels States can be snapshotted to allow exact replication of bugs or tests After executing tests, can revert to initial state Use with automated test suites to ensure consistent environments Test upgrade processes Keep a snapshot of installations for all versions or varying dependencies
Example 4 Test Environment Image from: [11] Test Optimization Using Software virtualization.
Other Virtualization Technologies Operating System Virtualization A layer in the operating system to run servers in a virtualized environment Each environment is a “container” The container can restrict resources (processor usage, file systems, etc.) However, there is no isolation from the kernel If kernel has vulnerabilities, entire system can be affected Protecting specific resources and other processes may be all the security required for some applications Useful for running multiple instances of a server using different configurations
Other Virtualization Technologies Application Virtualization “breaking the age old bond between physical hardware, operating system, and the program which runs on top of them” High-Level Languages (HLL) Java Microsoft's Common Language Infrastructure (CLI) Intermediate code generated by compilers get translated into native machine code using “just in time” technology Application only compiled once for all architectures present and future Only new HLL Virtual Machines are needed for new architectures
Other Virtualization Technologies Process Virtualization “Ghost processes” - An experiment by researchers using Linux kernel Duplicate processes Migrate processes Create process checkpoints Revert to process checkpoints Useful for testing and debugging Saving and restoring processes to allow reproduction of process states Or use to restore process to a good state on failures Loading from a snapshot may be quicker than a fresh load
Conclusion Abstraction to simplify use of computer resources Represent resources in simpler or different forms Add additional functionality or ability to resources Improve portability, security, performance, and reliability Cheaper alternative to multiple computers Excellent tool for testing
References [1] Virtualization. Retrieved April 2, 2007, from Wikipedia. Web site: http://en.wikipedia.org/wiki/Virtualization [2] Figueiredo, R.; Dinda, P.A.; Fortes, J. (2005, May). Guest Editors' Introduction: Resource Virtualization Renaissance. Computer. 38(5), 28-31. [3] Hyper-threading. Retrieved April 2, 2007, from Wikipedia. Web site: http://en.wikipedia.org/wiki/Hyperthreading [4] Automatic parallelization. Retrieved April 2, 2007, from Wikipedia. Web site: http://en.wikipedia.org/wiki/Automatic_parallelization [5] Vaughan-Nichols, S.J. (2006, Nov.). New Approach to Virtualization Is a Lightweight. Computer. 39(11), 12-14. [6] Smith, J.E.; Ravi Nair. (2005, May). The architecture of virtual machines. Computer . 38(5), 32-38. [7] Litty, Lionel. (2005). Hypervisor-based Intrusion Detection. Unpublished master's thesis. University of Toronto. [8] Ligneris, B. (2005, May). Virtualization of Linux based computers: the Linux-VServer project. High Performance Computing Systems and Applications, 2005. Proceedings. 19th International Symposium . 340-346. [9] Nakamikawa, T.; Morita, Y.; Yamaguchi, S.; Ishikawa, S.; Miyazaki, Y. (1997, Dec.). High performance fault tolerant computer and its fault recovery. Fault-Tolerant Systems, 1997. Proceedings. Pacific Rim International Symposium . 2-6. [10] Hypervisor. Retrieved April 2, 2007, from Wikipedia. Web site: http://en.wikipedia.org/wiki/Hypervisor
References [11] Seetharaman, S.; Krishna Murthy, B.V.S. (2006, Sept.-Oct.). Test Optimization Using Software virtualization. IEEE Software. 23(5), 66-69. [12] Operating system-level virtualization. Retrieved April 2, 2007, from Wikipedia. Web site: http://en.wikipedia.org/wiki/Operating_system-level_virtualization [13] Vallee, G.; Lottiaux, R.; Margery, D.; Morin, C. (2005, July). Ghost Process: a Sound Basis to Implement Process Duplication, Migration and Checkpoint/Restart in Linux Clusters. Parallel and Distributed Computing, 2005. ISPDC 2005. The 4th International Symposium on 04-06 July 2005. 97-104. [14] Application Virtualization. Retrieved April 2, 2007, from Wikipedia. Web site: http://en.wikipedia.org/wiki/Application_Virtualization [15] Hidenori Umeno; Parayno, M.L.C.; Koudai Teramoto; Masato Kawano; Hiraku Inamasu; Shuuhei Enoki; Masato Kiyama; Tomoo Aoyama; Takafumi Fukunaga. (2006, Oct). Performance Evaluation on Server Consolidation Using Virtual Machines. SICE-ICASE, 2006. International Joint Conference. October 2005. 2730-2734. [16] Uhlig, R.; Neiger, G.; Rodgers, D.; Santoni, A.L.; Martins, F.C.M.; Anderson, A.V.; Bennett, S.M.; Kagi, A.; Leung, F.H.; Smith, L. (2005, May). Intel virtualization technology. Computer. 38(5), 48-56.