Why Extractors?

Why Extractors?
E N D
Presentation Transcript
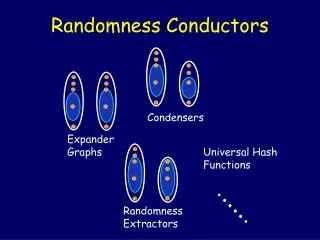
… Extractors, and the closely related “Dispersers”, exhibit some of the most “random-like” properties of explicitly constructed combinatorial structures. In turn, extractors and dispersers have many applications in “removing randomness” in various settings, and in making randomized constructions explicit … Why Extractors?
Santa Clause and his (Un)- Biased Elves The Story of Randomized Computations and Weak Random Sources
Distributed Computations • Cryptography The Computational Tasks of Santa (and Atnas) Clause Sampling, Simulations, Algorithms (e.g. Approximated TSP).
A coin please … Santa’s Source of Randomness
A coin please … But the North Pole is no Fairyland …
Thanks Erwin but I’ve grown attached to my elves … Pure Randomness in Nature? Hey Santa, you can use my cat !!
EXT almost uniform output source of biased correlated bits Assumeb1 b2 …bi … are i.i.d. 0/1 variablesand bi =1with someprobabilityp < 1then translate 01 1 10 0 Deterministic Extraction Other “easy” sources: markov chains[vN51,Eli72,Blu84],two independent sources[SV84,Vaz85,CG85] , bit-fixing sources[CGH+85,BBR85,BL85,LLS87,CDH+00],some efficiently samplable sources[TV00].
If b1 b2 …bi … are 0/1 variabless.t. bi =1with prob. p = p(b1 b2 …bi-1)[½-, ½+] cannot deterministically extract even a single bit !! A single SV-Source is sufficient to simulate BPP Can this Work for all Sources? • Can use even weaker sources [ChorGo88, CohenWi89, …]
Distribution on {0,1}nw/ k“bits of randomness” EXT mbits distance from uniform dtruly random bits Extractors[ , 93] • Xhas min-entropy k if xPr[X = x] 2-k(i.e. no likely elements). • Nonconstructive & optimal [NZ,RT]: extract all the randomness (i.e. mk+d) using d log ntruly random bits ( =.01)
Where Does the Seed Come From? • If “truly” random bits exist but expensive ... • Sometimes we can just enumerate over all 2d seeds:Let A be some probabilistic procedure and e an element from the weak random source.Run A(Ext(e,0…0)) , … , A(Ext(e,1…1))“combine” the outputs (majority, median, best, …). • In particular: can simulate BPP using a weak source [Zuc90].
G x,y x, Ext(x,y) Weak Sources in (Space Bounced) Computations • Thm [NZ93] Let A be a (randomized) space S machine(i.e. A can be in 2s configurations). If A uses poly(S) random bits it can be fully derandomized in space O(S). • Basic idea: Let A read a random2Sbit string x. Since A remembers at most S bits, x still contains (roughly) Sbits of entropy (independent of A’s state). Can recycle:
Applications of Extractors • Randomized algorithms w/ weak random sources. • Pseudorandom generators [NZ93,RR99,STV99] • Randomness efficient sampling and deterministic amplification [Zuc97] • Hardness of approximation [Zuc96,Uma99] • Exposure-resilient cryptography [CDHKS00] • Superconcentrators, sorting & selecting in rounds, highly expanding graphs [WZ93] • Leader election [Zuc96, RZ98], List decodable error correcting codes [TZ00], and more [Sip88,GZ97, …]
Constructions of Extractors • The “early days” [Zuc,NZ,WZ,GW,SZ,SSZ,NT,Zuc,TaS]Mainly hashing and various sorts of compositions.Some extractors: • [Zuc97] Fork = (n)can extractm=(1-) k bitsusing d =O (log n/) • [NT98] For allk can getm=k andd = poly (log n/) Other results in the high min-entropy case [GW], low min-entropy case [GW,SZ], dispersers [SSZ,TaS]
(Some) constructions of PRG from hard functions extractors Ha yes ... and there is a very nice one based on the NW generators Constructions of Extractors (cont.) • The “new age” [Tre99,RRVa,RRVb,ISW,RSW,RVW,TUZ] • Some more extractors [RSW]: for allk, • m= (k)andd = log n polyloglog nor • m=k/log kandd = O(log n)
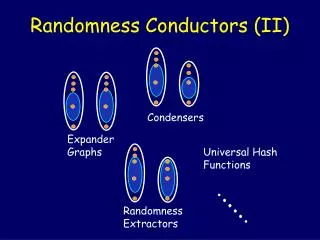
S, |S|=K=2k |(S)| > (1-) M D =2d Dispersers [Sipser 88] N=2n M =2m Difference from Expanders: • Typically M << N (farewell constant degree). • Expansion to almost the entire right hand side.
Ext(x,0…0) S T x Ext(x,1…1) Extractors imply Dispersers N=2n ={0,1}n • In fact we have the stronger property that S, |S|=K=2k and T, M =2m ={0,1}m
N N Y X A Construction in Search of Many Applications [WZ] • If G is a disperser (with < 1/2) then X, Y s.t.|X|=|Y|=K have at least onecommon neighbors. M G G • Using similar ideas, [WZ93] get Superconcentrators, highly expanding graphs, and much more
N N Y X Depth 2 Superconcentrators • X, Y, ts.t.|X|=|Y|=tthere existstvertex-disjoint paths between X andY. • [WZ] A construction with N log2N edges. • [RT] More carefully gives N log2N/loglog N edges. And this is essentially the only possible construction.
Some Conclusions • Need randomness to extract randomness. • Weak random sources appear naturally in computations. • Expanders, Extractors and Dispersers are closely related combinatorial objects. • Extractors are fascinating and very useful objects. Go home and build your own extractor …
(read only) Space S (i.e. 2sconfiguration) A (read once) input random string Weak Sources in Computations • Space bounded computations: