Introduction to Stream Cipher
Introduction to Stream Cipher. Sayed Mahdi Mohammad Hasanzadeh Hasanzadeh@Raymandcrypto.ir Spring 2004. Why we need to Cryptography ?. Data transfer algorithm. Source “ Plain text” ABCD… Source coding 100101001010111… Encryption Channel coding Data Transfer.

Introduction to Stream Cipher
E N D
Presentation Transcript
Introduction toStream Cipher Sayed Mahdi Mohammad Hasanzadeh Hasanzadeh@Raymandcrypto.ir Spring 2004
Data transfer algorithm • Source “Plain text” ABCD… • Source coding 100101001010111… • Encryption • Channel coding • Data Transfer
Why we need to Cryptography • We have redundancy in every language Pr(A) Pr(B) Pr(C) … Pr(Z) • Plain text redundancy leakage to Source Coding => Pr(1) Pr(0) ½ • Attacker guesses some of the bites from sequence • Then attacker guesses the plain text
Goals in cryptography 1) Cryptography remove the redundancy from sequence Pr(1)=Pr(0)=1/2 2) Cryptography is a mapping in the sequence space 3)Cryptography provide security in some cases: data integrity, Authentication and identification ,…
Tools in Cryptography • Symmetric encryption • Hash functions • Message authentication codes • Random number generators • Public-key encryption • Digital signatures • Authentication and identification • Key establishment, management, and certification
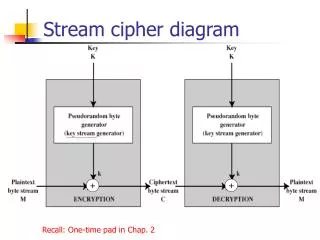
Symmetric Encryption • There are basically two ways to make a symmetric cipher: • Stream cipher: The encryption rule depends on the plaintext symbol’s position in the stream of plaintext symbols. • e.g.: Vigenere, RC4, A5 • Block cipher: Encrypt several plaintext symbols at once in a block. • e.g.: DES, AES, Twofish, RC6
Stream Cipher Pr(Pi=0) Pr(Pi=1) 1/2 Pr(Ci=0) =Pr(Ci=1) =1/2 Pr(ai=0) =Pr(ai=1) =1/2
Generator Properties • Randomness • Provable security • Bit rate • Key length • Complexity of algorithm • Memory • Resistant against every attack