Rootkits
Rootkits. Students: Jacek Czeszewski and Marcos Verdini Rosa Professor: José Manuel Magalhães Cruz. Introduction How a rootkit works Detection Preventing and Removing Attack damage References. 1. Introduction.

Rootkits
E N D
Presentation Transcript
Rootkits Students: JacekCzeszewskiand Marcos Verdini Rosa Professor: José Manuel Magalhães Cruz
Introduction • How a rootkit works • Detection • Preventingand Removing • Attack damage • References
1. Introduction A rootkit is a suite of one or more programs that allows a third party to hide files and activities from the administrator of a computer system.
1.1 Origins The original intent of rootkits (1996) appears to have centered simply on hiding programs that would allow an attacker to “sniff” or spy on traffic going to and from a computer system.
1.2 Functionality • Provide an attacker with full access via a backdoor, permitting unauthorized access to, for example, steal or falsify documents. • Conceal other malware, notably password-stealing key loggers and computer viruses. • Appropriate the compromised machine as a zombie computer for attacks on other computers. • Enforcement of digital rights management (DRM). • Conceal cheating in online games. • Detect attacks, for example, in a honeypot. • Enhance emulation software and security software. • Anti-theft protection. • Bypassing Microsoft Product Activation
1.3 Types of rootkits • User mode • Kernel mode • Bootkits • Hypervisor level • Hardware/Firmware
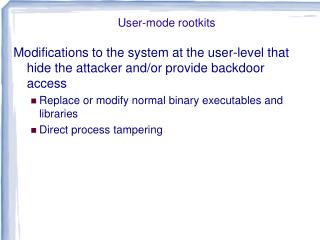
1.3.1 User mode • run in Ring 3 • manyinstallationvectors • Make to executeinsideany target processoroverwritethe memory of a target application
1.3.2 Kernel mode • run in Ring 0 • adding code or replacing portions of the core operating system, including both the kernel and associated device drivers • unrestrictedsecurityaccess
1.3.3 Bootkits • lows the malicious program to be executed before the operating system boots • cannot be detected by standard means of an operating system because all its components reside outside of the standard file systemserating system boots
1.3.4 Hypervisor level • uses hardware virtualization • trap a running instance of the operating system by starting a thin hypervisor and virtualizing the rest of the machine under it • donthave to load before the OS
1.3.5 Hardware/Firmware • hidden in BIOS, network card etc. • only way to remove is to replace infected hardware • could be hidden outside the computer for example in network printer
2. How a rootkit works • Installation • Physical access to the target system • Privilege Escalation • Cloaking • Obscure its presence from security tools • Modify the behavior of OS core parts • Load code into other processes
2. Study Case: Stoned Bootkit • Stoned is the name of a boot sector computer virus created in 1987, apparently in New Zealand. It was one of the very first viruses. • A memory resident bootkit up to the Windows kernel • Boot applications executed on startup • Drivers executed beside the Windows kernel
2. Study Case: Stoned Bootkit • Your PC is now Stoned! (1987) • Your PC is now Stoned! ..again (2010)
2. Study Case: Stoned Bootkit Windows Boot Process • Windows boot system assumes an already secure environment when starting
2. Study Case: Stoned Bootkit Hooking and Patching • Interrupt 13h hooked • Ntldr hooked for calling 32-bit code and patching the code integrity verification • Patching the NT kernel • Executing pay loads(driver)
2. Study Case: Stoned Bootkit Installation • Live CD • Infected PDF
2. Study Case: Stoned Bootkit Demonstration
3. Detection • Signature-Based • File IntegrityMonitoring • Cross-View Analysis • HookingDetection • Heuristics-BasedDetection • Network-BasedDetection
3.1 Signature-BasedDetection • analyzingrootkitto definefingerprint • integrating fingerprint in to the database • fingerprint can be used for rootkits detection 3.2 File Integrity Monitoring • calculatescryptographichashes for critical, unchangingoperating system files and comparesthem to knownvaluesthatarestored in a database
3.3 Cross-ViewAnalysis • It involves looking at the system from the high level “user”, or API view, and comparing it to the actual low level hardware view. 3.4 HookingDetection • When the rootkit modifies a hook to point to a malicious service or interrupt routine, the memory location almost invariably is located outside this specific range of the “clean” system, and is easily detected.
3.5 Heuristics-BasedDetection • Heuristics-Based detection of malware attempts to classify malicious behavior according to certain pre-determined rules. 3.6 Network-BasedDetection • System periodically send a snapshot of the network traffic and open ports to a trusted gateway for analysis. • The gateway compare this data with its “external” view of the system’s network activity
4. Preventingand Removing • Operating system updates • Automatic updates • Personal firewalls • Host-basedintrusionpreventionsystems • Rootkitpreventiontechniques
4. Preventingand Removing • number of security-software vendors offer tools to automatically detect and remove some rootkits • Some antivirus scanners can bypass file system APIs, which are vulnerable to manipulation by a rootkit • There are experts who believe that the only reliable way to remove them is to re-install the operating system from trusted media • in some cases the only possibility is to replace somehardware
5. Attack damage Home Users • Stealing Identity and private information • Turning Home User's computers into zombies • Loss of time, money and confidence
5. Attack damage Enterprise and Government • Loss of confidential information, theft of intellectual property • Reputation and customer trust • Additional costs of purchasing, installing, and administering security measures • Increases system complexity
6. References • Stallings & Brown - Computer Security: Principles and Practice • A comparative analysis of rootkit detection techniquesby ThomasMartinArnold • RicVieler - Professional Rootkits • http://en.wikipedia.org/wiki/Rootkit • http://opensecuritytraining.info/Rootkits.html • http://www.stoned-vienna.com