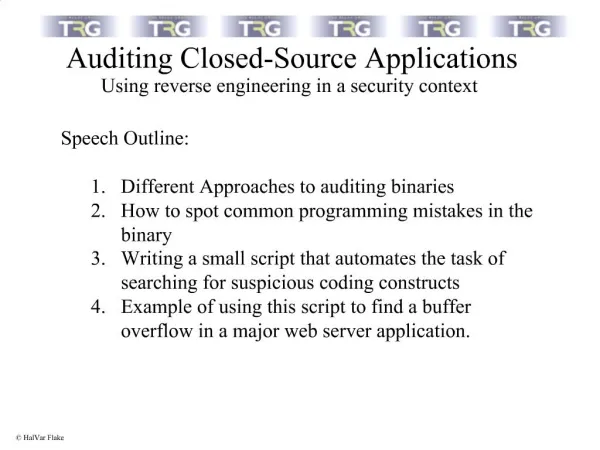
Auditing Closed-Source Applications
DESCRIPTION
This guide explores effective strategies for auditing closed-source applications, focusing on security and compliance best practices. It delves into the challenges posed by proprietary code and offers insights on assessing risks without access to source code. Learn about methodologies for evaluating security controls, ensuring compliance with industry standards, and implementing effective testing procedures. Understand the importance of documentation, vendor assessment, and continuous monitoring to maintain application integrity and safeguard against vulnerabilities.
1 / 33
Download Presentation 

Auditing Closed-Source Applications
An Image/Link below is provided (as is) to download presentation
Download Policy: Content on the Website is provided to you AS IS for your information and personal use and may not be sold / licensed / shared on other websites without getting consent from its author.
Content is provided to you AS IS for your information and personal use only.
Download presentation by click this link.
While downloading, if for some reason you are not able to download a presentation, the publisher may have deleted the file from their server.
During download, if you can't get a presentation, the file might be deleted by the publisher.
E N D
Presentation Transcript
More Related