Hacking Communication System
Hacking Communication System. Akib Sayyed akibsayyed@gmail.com. About Me. Telecom Security Researcher Spoke at NullCon 2012 Works on SDR ,GNURADIO Certified Psycho . About Company. Payatu Technologies Pvt. Ltd. Boutique Security Testing Company

Hacking Communication System
E N D
Presentation Transcript
Hacking Communication System Akib Sayyed akibsayyed@gmail.com
About Me • Telecom Security Researcher • Spoke at NullCon 2012 • Works on SDR ,GNURADIO • Certified Psycho
About Company • Payatu Technologies Pvt. Ltd. • Boutique Security Testing Company • Blackbox/Product/Web/Mobile Audits • Security Trainings • Organizers of nullcon Security Conference
What are we looking at • Hacking GSM • Hacking Core Telecom Network
What can we do with GSM • Listen Call • Impersonate some1’s Identity • Track Location
Listening to Calls • More like a Rocket Science Till 2006 • People built own crackers and interceptors • Some of them are open source • Easy to build • Open Source Software and Hardware available to receive data and Crack encryption.
Cost for 1 Interceptor • 1500 Rs Phone • 20000 Rs hard disk with rainbow tables • 20000 Rs worth Computer • Home Made Software + Open Source Code • And your interceptor is ready
Protecting Calls • Upgrade encryption Standard • Allow A5/3 • Randomize SI and Padding • End to End Call encryption • Use 3G :P
Impersonating • Use some’1s identity while making request to network • This allows one to impersonate identity of some1else. • Can • Make/ Receive Calls • Send/Receive SMS • Divert Calls
Protection Against Impersonating • End User Cannot do anything • Operator Need to work on same • Authenticate Calls • Authenticate SMS • Authenticate USSD Request
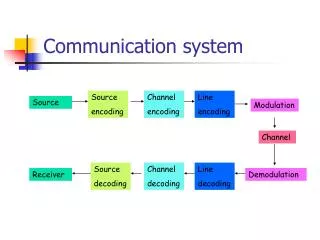
Core Network in Telco Image Credits : http://www.gl.com
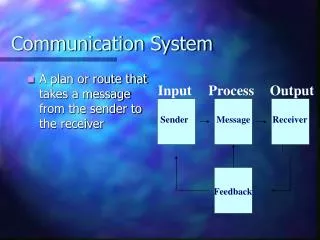
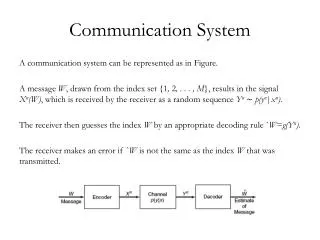
Core Network 2G /3G • Based on SS7/SIGTRAN and IP • In simple words Either TDM(T1/E1) or IP (SCTP/TCP IP) • No authentication (No User Name and Password) (on SS7)
SS7 is used for • Carry Voice • SMS • USSD (Unstructured Supplementary Service Data ) • Call Handling • Operation and Maintenance • Mobility Services • Location Management • ......
SS7 /SIGTRAN Stack Image Credit : Mobicents
Protocols in SS7/Sigtran • MTP1/2/3,M3UA • SCCP -> Signalling Connection Control Part • TCAP -> Transaction Capability Application Part • ISUP -> ISDN User Part • MAP -> Mobile Application Part • CAP ->Camel Application Part • INAP-> Intelligent Network Application Part
MTP1/2/3 And M3UA • Provides physical , data link layer and Network layer • MTP1 = Message Transfer part 1 • MTP2 = Message Transfer part 2 • MTP3 = Message Transfer part 3 • M3UA = MTP3 User Adaption Layer
SCCP /TCAP • Signalling Connection Control Part • Provides Extended Routing , Flow Control ,Connection Oriented /Connection less • Relies on MTP for basic routing and error correction • Transaction Capability Application Part • Facilitate Multiple Concurrent dialog Between Same SSN • More like session handler
MAP • Mobile Application Part • SMS • USSD • Call Handling , Routing • Location Management
CAP • Camel Application Part • Used when subscriber is roaming • Allow home network to monitor and control calls made by subscriber • Intelligent Network Application Part
Routing in SS7 • Based on PC (Point Code) == LAN IP • Based on GT (Global Title) == WAN IP • SSN (Sub System Number) == Port Number • STP(Signalling Transfer Point) == Router • SSP (Service Switching Point) • SCP (Service control point)
Routing based on Point Code Image Credit : Cisco
Routing Based on GTT Image Credit : Cisco
Routing based on GTT Image Credit : Cisco
Where we can attack • SCCP- Signalling Connection Control Part • TCAP- Transaction Capabilities Application Part • ISUP – ISDN user part • MAP – Mobile application part • CAP - Camel Application part • INAP- Intelligent network application part
Some Example of Attacks • Purging MS from HLR • Insert Subscriber Data • Delete Subscriber Data • Send Authentication info Flood • Send Routing info Exposes IMSI of subscriber • Hostile Location Update • Cancel Location Update • MAP ATI exposes Location of subscriber
How to protect network • Check if network is vulnerable to such attack • We have our own proprietary tool for doing same • Perform filtering of non required message at point code level or STP level • Use SS7 Firewall /IDS
Thanks • Questions