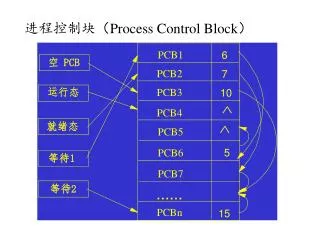
The Process Control Block
The Process Control Block. From: http://en.wikipedia.org/wiki/Task_struct

The Process Control Block
E N D
Presentation Transcript
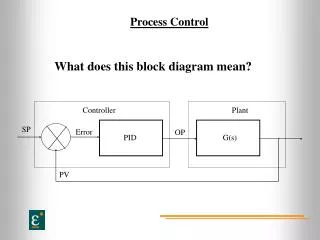
The Process Control Block From: http://en.wikipedia.org/wiki/Task_struct • A Process Control Block (PCB, also called Task Control Block or Task Struct) is a data structure in the operating systemkernel containing the information needed to manage a particular process. The PCB is "the manifestation of a process in an operating system".[1]
Implementations differ, but in general a PCB will include, directly or indirectly: • The identifier of the process (a process identifier, or PID) • Register values for the process including, notably, the Program Counter value for the process • The address space for the process • Priority (eg., nice value on Unix operating systems) • Process accounting information, such as when the process was last run, how much CPU time it has accumulated, etc. • Pointer to the next PCB i.e. pointer to the PCB of the next process to run • I/O Information (i.e. I/O devices allocated to this process, list of opened files, etc)
During a context switch, the running process is stopped and another process is given a chance to run. The kernel must stop the execution of the running process, copy out the values in hardware registers to its PCB, and update the hardware registers with the values from the PCB of the new process. • Location of the PCB • Since the PCB contains the critical information for the process, it must be kept in an area of memory protected from normal user access. In some operating systems the PCB is placed in the beginning of the kernel stack of the process since that is a convenient protected location. [2]
Interrupts • An interrupt is an event that stops the execution of the current program (at the end of its currently executing instruction), saves the state of the current program and its process, begins execution of the appropriate interrupt routine that handles the interrupt, then selects (schedules) a program in the “ready” wait queue, and then dispatches that program.
The Scheduler is an OS routine that selects the next process in the ready queue to begin execution. This selection is based on the scheduling algorithm used. (covered later) • The Dispatcher is an OS routine that begins the execution of the program for the scheduled process. • Restores the state of the process • Loads the PSW • Loads the PC with the address of the program’s next instruction to be executed after the last instruction executed and the process was interrupted.
Two common types of interrupts • A time-out interrupt where the system timer signals the end of the process’s time slice
A software interrupt by the program which is most often an I/O instruction executed by the program • The program specifies the type of interrupt such as a read or a write by storing values in registers (?) • The program issues and interrupt call (ex. INT instruction in the Intel 8086)
From: http://en.wikipedia.org/wiki/Interrupt • Interrupts can be categorized into: maskable interrupt (IRQ), non-maskable interrupt (NMI), interprocessor interrupt (IPI), software interrupt, and spurious interrupt. • A maskable interrupt (IRQ) is a hardware interrupt that may be ignored by setting a bit in an interrupt mask register's (IMR) bit-mask. • Likewise, a non-maskable interrupt (NMI) is a hardware interrupt that does not have a bit-mask associated with it - meaning that it can never be ignored. NMIs are often used for timers, especially watchdog timers.
An interprocessor interrupt is a special case of interrupt that is generated by one processor to interrupt another processor in a multiprocessor system. • A software interrupt is an interrupt generated within a processor by executing an instruction. Software interrupts are often used to implement System calls because they implement a subroutine call with a CPU ring level change.
A spurious interrupt is a hardware interrupt that is unwanted. They are typically generated by system conditions such as electrical interference on an interrupt line or through incorrectly designed hardware. • Processors typically have an internal interrupt mask which allows software to ignore all external hardware interrupts while it is set. This mask may offer faster access than accessing an interrupt mask register (IMR) in a PIC, or disabling interrupts in the device itself. In some cases, such as the x86 architecture, disabling and enabling interrupts on the processor itself acts as a memory barrier, in which case it may actually be slower.
Multitasking and Time Slices • http://en.wikipedia.org/wiki/Time-sharing • Time-sharing refers to sharing a computing resource among many users by multitasking. Its introduction in the 1960s, and emergence as the prominent model of computing in the 1970s, represents a major historical shift in the history of computing. By allowing a large number of users to interact simultaneously on a single computer, time-sharing dramatically lowered the cost of providing computing, while at the same time making the computing experience much more interactive.
From: MDSN pages on Multitasking • A multitasking operating system divides the available processor time among the processes or threads that need it. The system is designed for preemptive multitasking; it allocates a processor time slice to each thread it executes. The currently executing thread is suspended when its time slice elapses, allowing another thread to run. When the system switches from one thread to another, it saves the context of the preempted thread and restores the saved context of the next thread in the queue.
The length of the time slice depends on the operating system and the processor. Because each time slice is small (approximately 20 milliseconds), multiple threads appear to be executing at the same time. This is actually the case on multiprocessor systems, where the executable threads are distributed among the available processors. However, you must use caution when using multiple threads in an application, because system performance can decrease if there are too many threads.
From the Linux man page > man 7 time The Hardware Clock • Most computers have a (battery-powered) hardware clock which the kernel reads at boot time in order to initialize the software clock. For further details, see rtc(4) and hwclock(8).
The Software Clock, HZ, and Jiffies The accuracy of many system calls and timestamps is limited by the resolution of the software clock, a clock maintained by the kernel which measures time in jiffies. The size of a jiffy is determined by the value of the kernel constant HZ.
The value of HZ varies across kernel versions and hardware platforms. • On x86 the situation is as follows: • on kernels up to and including 2.4.x, HZ was 100, giving a jiffy value of 0.01 seconds; • starting with with 2.6.0, HZ was raised to 1000, giving a jiffy of 0.001 seconds; • since kernel 2.6.13, the HZ value is a kernel configuration parameter and can be 100, 250 (the default) or 1000, yielding a jiffies value of, respectively, 0.01, 0.004, or 0.001 seconds.
Broken-down time Certain library functions use a structure of type tm to represent broken-down time, which stores time value separated out into distinct components (year, month, day, hour, minute, second, etc.). This structure is described in ctime(3), which also describes functions that convert between calendar time and broken-down time. Functions for converting between broken-down time and printable string representations of the time are described in ctime(3), strftime(3), and strptime(3).
Sleeping and Setting Timers • Various system calls and functions allow a program to sleep (suspend execution) for a specified period of time; see nanosleep(2) and sleep(3). • Various system calls allow a process to set a timer that expires at some point in the future, and optionally at repeated intervals; see alarm(2), getitimer(2), and timer_create(3).