Kerberos
180 likes | 567 Views
Kerberos. Presented By: Pratima Vijayakumar Rafi Qureshi Vinay Gaonkar CS 616 Course Instructor: Dr. Charles Tappert. Introduction. Kerberos History Kerberos Environment Kerberos Architecture Kerberos Protocols Kerberos Version 5 Kerberos Advantages Kerberos Weaknesses and Solutions.

Kerberos
E N D
Presentation Transcript
Kerberos Presented By: Pratima VijayakumarRafi QureshiVinay GaonkarCS 616Course Instructor: Dr. Charles Tappert
Introduction • Kerberos History • Kerberos Environment • Kerberos Architecture • Kerberos Protocols • Kerberos Version 5 • Kerberos Advantages • Kerberos Weaknesses and Solutions
History • Developed at MIT in early 1980’s • Computing shift from mainframes to workstations • Pools of distributed workstations connected to servers • Concept of ”Network Credentials” • Commercial versions V4 and V5 • Principles and systems are relevant until today • Concepts incorporated in DCE, AFS, NT, etc.
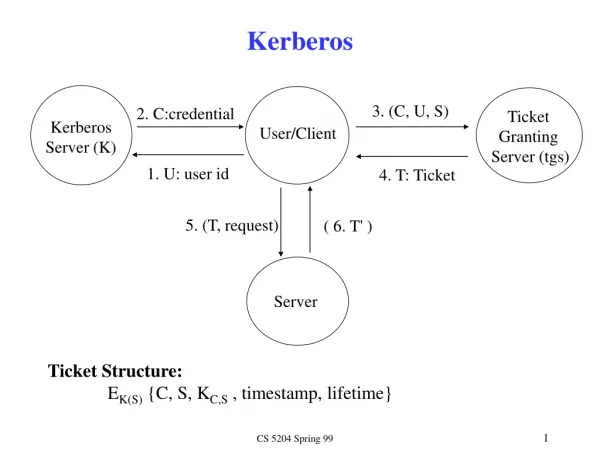
Kerberos Environment (II) KRB consists of: AS – Authentication Server TGS – Ticket Granting Server DB – Database of entity keys Separation between two actions: Authentication – ”logging into the network” Communication – ”holding a session between two parties”
Kerberos Architecture (II) • Kerberos implements the ”Internet Scenario” • User A has password PWA to authenticate to KRB • KRB stores key KA that is derived from password PWA • Server B has key KB to authenticate to KRB • KRB stores key KB that is identical to the server’s key • Workstations are stateless – they don’t know the users and their passwords, and they don’t have keys • Kerberos provides tickets to the source party (A+WS), which requested the session, and it does not bother the destination party (B)
Kerberos V5 Protocols (I) Acquiring Network Credentials: 1.) User A starts working at workstation WS by entering its name ”A” and password PWA. Workstation WS computes key KA from PWA, and it then erases password PWA from its memory. 2.) Workstation WS contacts Authentication Server (AS) and requests ”Network Credentials” to A+WS. Workstation WS sends following clear data – < A, WS, RealmA, TGS, Times, Nonce1> to AS (where Times gives the time validity interval, and Nonce1 is random value). 3.) Authentication Server AS replies to A+WS with following two items: < RealmA, A, TKTTGS > AND < KA,TGS, Times, Nonce1, RealmTGS, TGS > sealed by key KA (where TKTTGS = < KA,TGS, RealmA, A, WS, Times > sealed by key KTGS). Workstation WS now tries to open the sealed item using the computed key KA.
Kerberos V5 Protocols (II) Establishing Connection with Server: 4.) Workstation WS contacts Ticket Granting Server (TGS) and requests ticket for B as follows: < B, Times, Nonce2, TKTTGS, Auth1 > (where Auth1 = < A, WS, RealmA, Timestamp1 > sealed by key KA,TGS). 5.) Ticket Granting Server TGS replies to A+WS with following two items: < RealmA, A, TKTB > AND < KA,B, Times, Nonce2, RealmB, B > sealed by KA,TGS (where TKTB = < KA,B, RealmA, A, WS, Times > sealed by KB). Workstation WS opens the sealed item using key KA,TGS. 6.) Workstation WS requests a session from B by sending < TKTB, Auth2 > (where Auth2 = < A, WS, RealmA, Timestamp2, Subkey, Seq# > sealed by key KA,B). Fields Subkey and Seq# are optional. 7.) Server B opens ticket TKTB with key KB and replies to A+WS with authentication Auth3 = < Timestamp2, Subkey, Seq# > sealed by A,B.
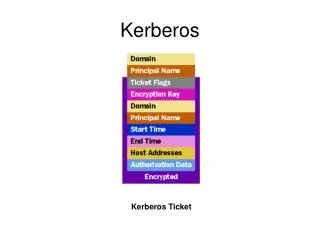
Kerberos V5 Options and Flags INITIAL: Indicates that a ticket was issues by AS and not by a TGS. PRE-AUTHENT: Indicates that the user was pre-authenticated by some means before a TGS ticket was issued. HW-AUTHENT: Indicates that the user was authenticated with a hardware token before a TGS ticket was issued. RENEWABLE: Tells TGS that this ticket can be used to obtain a replacement ticket that expires at a later date. INVALID: Indicates that this ticket is invalid and must be validated by the TGS before use.
Kerberos V5 Options and Flags MAY-POSTDATE: Tells TGS that a post-dated ticket may be issued based on this ticket-granting ticket. POSTDATED: Indicated that this ticket has been postdated. PROXYABLE: Tells TGS that a new service-granting ticket with a different network address may be issued based on this ticket. FORWARDABLE: Tells TGS that a new ticket-granting ticket with different network address may be issued based on this ticket-granting ticket. FORWARDED: Indicates that this ticket has either been forwarded or that it was issued based on authentication involving a forwarded ticket.
Kerberos - Advantages • Passwords aren’t exposed to eavesdropping • Single Sign-on • More convenient: only one password, entered once • Stolen tickets hard to reuse • Need authenticator as well, which can’t be reused • Wide support in various operating systems. • Prevents transmission of passwords over the network.