Fibonacci Heaps
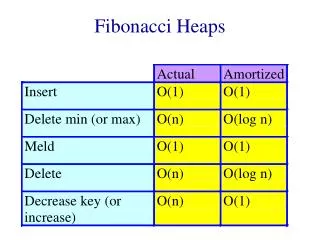
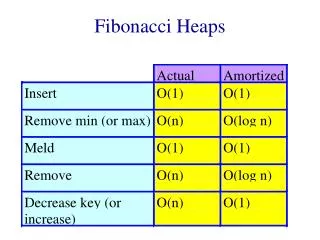
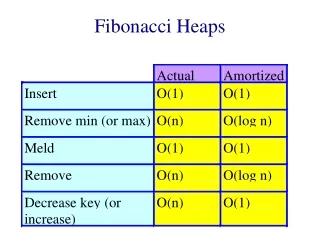
Fibonacci Heaps. Especially desirable when the number of calls to Extract-Min & Delete is small (note that all other operations run in O(1)

Fibonacci Heaps
E N D
Presentation Transcript
Fibonacci Heaps • Especially desirable when the number of calls to Extract-Min & Delete is small (note that all other operations run in O(1) • This arises in many applications. Some graph problems, like minimum spanning tree and single-source-shortest-path problems call decrease-key much more often than other operations
Fibonacci Heaps • Loosely based on binomial heaps • If Decrease-key and Delete are never called, each tree is like a binomial tree
Fibonacci Heaps • A Fibonacci heap is a collection of heap-ordered trees. • Each tree is rooted but unordered. • Each node x has pointed p[x] to its parent & child [x] to one of its children • Children are linked together in a doubly-linked circular list. • Doubly-linked circular list: Removing a node is O(1) and splicing two lists is O(1)
Fibonacci Heaps • Each node also has degree [x] indicating the number of children of x • Each node also has mark [x], a boolean field indicating whether x has lost a child since the last time x was made the child of another node • The entire heap is accessed by a pointer min [H] which points to the minimum-key root
Amortized Analysis • Potential function: (H) = t (H) + 2 m (H) • The amortized analysis will depend on there being a known bound D(n) on the maximum degree of any node in an n-node heap • When Decrease-Key and Delete are not used, D(n)=log (n)
Fibonacci Heap • An unordered binomial tree is the same as a binomial tree except that Uk = 2 copies of Uk-1 where the root of one tree is made any child of the root of the other • If an n-node Fibonacci heap is a collection of unordered binomial trees, then D(n)=log(n)
Fibonacci Heaps • Called a lazy data structure • Key idea: Delay work for as long as possible
Fibonacci Heap Operations • Insert • Find-Min • Union • Extract-Min • Consolidate
Analysis of Extract-Min • Observe that if all trees are unordered binomial trees before the operation, then they are unordered binomial trees afterwards • Only changes to structure of trees: • Children of minimum-root become roots • Two Uk trees are linked to form Uk+1
Analysis of Cost: Actual Cost • O(D(n)) children of minimum node. • Plus cost of main consolidate loop • Size of root list upon calling consolidate is D(n) + t(H) - 1 • Every time through loop, one root is linked to another • Therefore, total amount of work is D(n)+t(H)
Analysis of Cost • Actual Cost: D(n) + t(H) • Potential Before: t(H) + 2m(H) • Potential After: At most (D(n)+1) + 2 m(H) since at most D(n) + 1 roots remain.
Decrease Key • If heap order is not violated (by the change in key value), then nothing happens • If heap order is violated, we cutx from its parent making it a root • The mark field has the following effect: as soon as a node loses two children, it is cut from its parent • Therefore, when we cut a node x from its parent y, we also set mark [y]
Decrease Key • If mark [x] is already set, we cut y as well. • Therefore, we might have a series of cascading cuts up the tree.
Actual Cost of Decrease Key • Actual Cost: 1 + cost of cascading cuts • Let c be number of times cascading cut is recursively called. • Therefore, actual cost is O(c)
Change in Potential • Let H be original heap. Each recursive call, except for last one, cuts a marked node and clears a marked bit. • Afterwards, there are t(H) + c trees & at most m(H) - c + 2 marked nodes ( c - 1 unmarked by cascading cuts & last call may have marked one)
Cost of Decrease Key • Intuitively: m(H) is weighted twice t(H) because when a marked node is cut, the potential is reduced by 2. One unit pays for the cut & the other compensates for the increase in potential due to t(H)
Bounding Maximum Degree • To show that Extract-Min & Delete are O(log n), we must show that the upper bound D(n) is O(log n) • When all trees are unordered binomial trees, then D(n)=log n • But, cuts that take place in Decrease-Key may violate the unordered binomial tree properties.