All You need to know About Firewall
140 likes | 414 Views
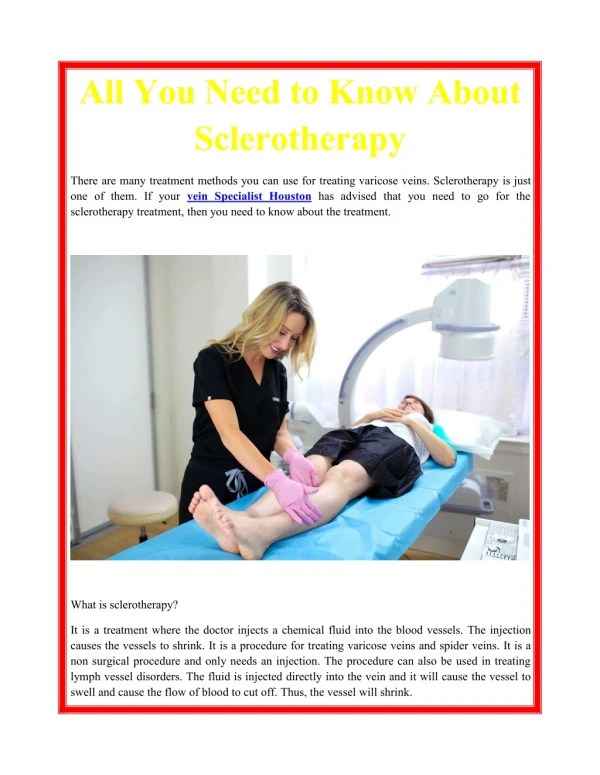
Cyberoam offers next-generation firewall and UTM firewall that provide stateful and deep packet inspection for network, application and user identity-based security. Cyberoam firewall appliances provide ease of management and high security with flexibility.

All You need to know About Firewall
E N D
Presentation Transcript
Firewall N/W Security A firewall can be described as a network security system whose function is to control and monitor incoming and outgoing networks. A firewall is based on predetermined security rules. It acts as a barrier securing an inner network from an outer network, for instance, internet. Network firewall is a software appliance running on hardware based firewall used to filter traffic on more than two networks. A layer of software protection is provided by a host based firewall on one of the hosts that is responsible for network traffic. Routers are used to separate different broadcast domains and pass data between networks, these networks contain firewall components and also performs basic routing functions.
How do Firewalls Work Firewalls are set up at every Internet connection point. This helps the system in evaluating even the minutest of data which flows into it. These firewalls can be tuned to follow a specific set of rules, either specified by you or by the administrator, to allow traffic to their servers.
Characteristic of Firewall Direction control: Helps determine direction for the initiation of requests allowed to flow from Firewalls. Service control: To determine types of services that are accessible, such as outbound and inbound. Traffic can be filtered on the basis of protocol, port number, proxy servers and IP addresses. Behavior control: It controls some particular services. A portion of the information provided on a local web server may be externally accessible. User Control: It can be applied for incoming traffic from external users and requires some form of authentication such as provided by IPsec.
OSI Vs TCP/IP Networks Model To understand the working of a firewall, we must know how different networking layers interact in the flow. Each layer has a set of responsibilities and is handled in a well-defined manner. The OSI model is a newer version that has become a standard as TCP/IP does not meet several requirements and industry standards. The lowest level at which a Firewall works is layer three and it is defined as the network layer in OSI model whereas in TCP/IP it works as an Internet protocol layer. This layer is concerned with the destination of routing packets. At this level, it can be determined whether the source is trusted or not.
Need of Firewall Protection There is no doubt that internet has transformed the way the companies transacted their business years ago. Although enterprises are leveraging its use for day-to-day business transactions, but internet has some setback. Internet has made confidential data available to unscrupulous computer geeks who look out for such sensitive data either to trade or fulfil their other vested interests. Firewall works as a protective sheet between private enterprise networks and hackers, to prevent the theft of such confidential enterprise data.
Use of Next-generation firewalls (NGFW) Next Generation Firewalls came into the picture due to some limitations in Stateful Packet Inspection as it does not inspect network packets containing data payload and also due to high network traffic, it uses web protocols, including business and non-business applications. New approaches have been added by security vendors, including deep packet and inspection intrusion prevention, for the detection of malware in network traffic. This can be a drawback too as these approaches add more and more devices that add latency, as these packets are passed from one appliance to the other. These devices should be configured in some unified threat management systems so that multiple functions can be handled in a single platform. NGFW helps address application awareness drawbacks and traffic inspection, without hampering performance.
The Development of Firewall Types in Network Security System Network security has been through a lot of changes and iterations in order to have evolved and provide better protection to users. . In this brief blog post, we provide you information about the different types of network firewall. Access Control Lists (ACLs) – This type of firewall was used earlier and used for routers. It was fairly used for performance and scalability however a drawback of this firewall is it is unable to read anything more than packet headers. This provides only the undeveloped and fundamental information about the traffic. Proxy firewalls – The firewall works on incoming network traffic by copying the anticipated recipient. Proxy firewalls inspect the network traffic and send details to the destination computers that is possible only when the access is permitted. The response of the computer response is then transferred to the proxy that sends the data across with the origin address of the proxy server. Through this process the proxy firewalls build a gap between two computers which implies that it is the only machine connected to the outside world.
The Development of Firewall Types in Network Security System (Cont.) Stateful inspection firewalls – An evolutionary step in the world of network firewall, it is effective in sorting and tracking the actual state of traffic. It tracks the state of traffic by examining all the connection interactions till the time a connection is suspended. Unified Threat Management (UTM) solutions – These are the solutions that combine stateful examination firewalls, IPS and antivirus into a single machine by taking into account other network security capabilities. Next-generation firewalls (NGFWs) – These firewalls were created to counteract the growing capability of appliances and malware. The NGFW brings together the major network protection functions, comprising of unconventional firewall, URL filtering, IPS/IDS and threat security. The NGFW solutions ensure improved security as compared to the legacy firewalls, point threat finding products, or UTMs. These functions are designed into the product from the beginning and share important information across various disciplines.
Benefits of Firewall Prevent attacks on your private network by the other networks outside the world. It allows you to define a funnel, keeping aside the non-authorized users. Allow monitoring the security of your network and computer when suspicious activity occurs, it will generate an alarm. Monitor and record services using WWW (World Wide Web), FTP (File Transfer Protocol) and other protocols. Control the use of Internet. It helps to block or un-block inappropriate or appropriate material.
Disadvantages of Firewall Legitimate User Restriction Diminished Performance Vulnerabilities Internal Attack Cost
Cyberoam Technologies USA Central : +1-732-412-4896 Delhi & NCR : +91-9899150300 Ahmedabad : +91-9925011328 Bangalore: +91-9880345671 Dubai: +971-4-214 9860 Cyberoam House, Saigulshan Complex, Opp. Sanskruti, Beside White House, Panchwati Cross Road, Ahmedabad - 380006, GUJARAT, INDIA. North America 505 Thornall Street, Suite # 304 Edison, NJ -08837 USA sales@cyberoam.com http://www.cyberoam.com/