Lecture Topics: 11/29
210 likes | 341 Views
Lecture Topics: 11/29. Cryptography symmetric key (secret key) public/private key digital signatures. Announcements. Next Monday, Mike Swift will talk about operating system security Next Wednesday, I will give a wrap up of the class and hand out class evaluations

Lecture Topics: 11/29
E N D
Presentation Transcript
Lecture Topics: 11/29 • Cryptography • symmetric key (secret key) • public/private key • digital signatures
Announcements • Next Monday, Mike Swift will talk about operating system security • Next Wednesday, I will give a wrap up of the class and hand out class evaluations • your web servers are also due • Final is on Wednesday December 13th • Review session • Sunday December 10th OR • Monday December 11th
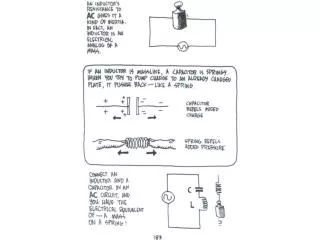
Cryptography • Cryptography transforms data so that it is useless to your opponent • Your opponent could be • the Roman Empire • the CIA • someone eavesdropping on your network • Your data could be • battle plans • credit card number • Cryptography has been around for a long time, but since WWII it has really become a science
Encrypt/Decrypt • Cryptography has two stages • Encrypting converts plaintext data into an unusable form (known as ciphertext) • Decrypting converts ciphertext back to plaintext Encryption Algorithm Decryption Algorithm Attack at Dawn! J#832JN8K9#$&DFG Attack at Dawn! Plaintext Ciphertext Plaintext
Encryption Works When… • Encryption function cannot be easily inverted • "!nwaD ta kcattA" is no good • Encryption and decryption can be done safely • no one is looking over your shoulder or tapping your network • The keys are protected • it doesn't work if your login password is written on the monitor • you shouldn't write your PIN # on your ATM card
Bad Encryption Schemes • Add 1 to every letter • e.g. attack at dawn -> buubdl bu euxo • can figure out actual letters based on their frequency (E, T, A, …) • Any scheme that reassigns or swaps letters is weak • Generally any encryption scheme that requires the algorithm to remain secret is bad • German's Enigma machine in WWII
Symmetric Key Encryption • A good encryption scheme uses a random key (128 bit string) and a bunch of math operations to encrypt data • practically impossible to decrypt without the key • The same key and the same algorithm can be used to decrypt the data • This is known as symmetric key encryption because the same key is used for encryption and decryption • It is also known as secret key encryption • Example: DES, AES, blowfish, RC2 Attack at Dawn! J#832JN8K9#$&DFG Attack at Dawn! Encrypt Encrypt same key same algorithm
Symmetric Key Evaluation • Symmetric key encryption can be used whenever the key can be safely given to everyone who needs it • how would I safely send my credit card number to Amazon? • Advantage: it's very fast • 1 Gbit/sec in hardware • 100 Mbit/sec in software • Good for encrypting large pieces of data • files • network traffic
Eavesdropping • Communication between persons or computers is inherently insecure • Your little sister might listen in on phone conversations • Someone on your Ethernet sees all of your network traffic (known as eavesdropping) • Secure communication over an insecure channel requires encryption • An even more severe attack occurs when communication goes through an attacker. The attacker can • see every message • discard any message • modify messages from either party • replay old messages • this is known as a man-in-the-middle attack
Public Key *#&!# Private Key Hello Hello Private Key Public Key j@xik Hello Hello Public Key Encryption • Public/private key encryption uses two different keys to encrypt and decrypt • Data encrypted with the public key can only be decrypted with the private key • Data encrypted with the private key can only be decrypted with the public key • Public key is known by everyone, private key is known only to you
Public/Private Key Examples • I want to send you a secret message • I encrypt it with your public key • Only you have the private key, so only you can decrypt it • I want you to know that I sent the message • I first encrypt it with my private key • Then I encrypt it with your public key [X]KEY is notation for X being encrypted with KEY Insecure channel Me You Message Message [Message] MyPriv [Message] MyPriv [[Message] MyPriv ] YourPub [[Message] MyPriv ] YourPub
Public/Private Key Evaluation • Don’t have to share a secret to communicate securely • still need some way to get someone's public key (usually trusted third party, e.g. Verisign) • Disadvantage: it's very very slow • more than 1000 times slower than secret key encryption • Too slow to be used to encrypt large amounts of data • so how can network communication be secure?
Negotiating a Secret Key • Frequently public/private keys are used to negotiate a shared secret key • Messages used to find a secret key must be small • Messages encrypted with the secret key can be any size You [What secret key to use?] AmazonPub [Use SymmetricKeyXYZ] YourPub [Order form w/ credit card #] SecretKeyXYZ [Receipt w/ credit card #] SecretKeyXYZ
Digital Signatures • Need a way to "sign" messages to verify who they came from • If send the message "Reminder: The final is at 8:30", I don't want someone to change it to "The final has been cancelled, everyone gets an A" • I could encrypt the whole message with my private key • only I can encrypt messages with my private key so you know I sent the message • problem: too slow for large messages • Solution: message digests
One-way Hashes • A one-way hash function hashes data to a value, and it’s impossible to guess the original value from the hash • It's almost impossible to find collisions • it's very very unlikely that two messages could produce the same hash value • Example: MD5 hashes data to a 128-bit value • no MD5 collisions have ever been found • Can be used to store passwords • store MD5 hash of a password in a password file • when checking a password, first hash it and then compare it to what is in the file • no way to get the password from the stored hash value
“Impossible” to modified Data w/ Identical Hash value Modified Data w/ Identical Chksum Orig. Data w/ One-way Hash Orig. Data w/ Chksum 1010100101110100110010101011010101011011101000101101010101101010101011010100101110100110010101011010101011011101 1010100101110100110010101011010101011011101000101101010101101010101011010100101110100110010101011010101011011101 1010111010011001010101101010101100100010110101010110101010101101010010111010011001010110101010110111010101001110 1010111010011001010101101010101100100010110101010110101010101101010010111010011001010110101010110111010101001110 0010010111010000110001110100001100010111000011000101110100010010001001011101000000111010000110001011100001100100 0010010111010000110001110100001100010111000011000101110100010010001001011101000000111010000110001011100001100100 0011000101110100 0011000101110100 One-way Hash Continued • A one-way hash is similar to a checksum, but much safer • It's easy to modify a message that preserves the original checksum • It's impossible to modify a message that preserves the original one-way hash value
We the people of the United States, in order to form a more perfect union ... until an election of Representatives shall have intervened. AFD4 17E9 C039 BAD3 1C84 F832 7326 836C 275D CA86 5ED0 0345 9831 8376 CD72 C98C Message Digest • A message digest is a one-way hash of a message • much smaller than the original message • “impossible” to find another message that generates the same digest Constitution of the United States Digest of the Constitution. Cannot find another document that generates the same digest.
Digital Signatures • I can digitally sign a message by • computing a digest of the message • encrypting the digest with my private key • You can verify I wrote the message by • decrypting the digest using my public key • computing the digest of the message • comparing this digest with the decrypted digest • Much faster than encrypting the entire message • Problem: replay attacks • what if I sent the message “Class is cancelled today” and signed it • what prevents someone from retransmitting this message everyday? • Solution: don’t write ambiguous messages (i.e. use timestamps) or use challenge response
Challenge/Response • To verify the server’s identity, the client challenges the server • The challenge is usually to encrypt a random string (known as a nonce) with the server’s private key • Only the true server can encrypt the nonce with its private key • If server responds with the correct encrypted nonce, the client trusts his identity • The nonce is a different random string each time so replay attacks are impossible
Nonce 1 [Amazon.com, AmazonPubKey]VerisignPubKey 2 [SecretSessionKey]AmazonPubKey 3 Establishing a secure connection with SSL 4 [Credit Card Number]SecretSessionKey [Nonce]SecretSessionKey 5 Simplified SSL • Some additional information is transferred with each message, but this simplified version contains all of the necessary details You
Explanation of Simplified SSL • The client sends the server a nonce to prevent a replay attack, and the server stores this nonce • The server sends the client a certificate, which contains it’s name and public key. This certificate has been digitally signed by Verisign (a trusted third party) • The client chooses a secret (symmetric) session key to use for this connection. It encrypts this key with the server’s public key and sends it to the server. • The server decrypts the session key using it’s private key. It sends the original nonce back to the client encrypted with the session key. The client now has verified that it is actually talking with the correct server, because only the correct server can decrypt the session key sent in step 3. • Any remaining secret communication between the client and server can use the session key. • There is much more to SSL than what is presented here. There are a vast number of options and features.