Layer 2 - Data Link Layer
Layer 2 - Data Link Layer. Access to Shared Media -. Media Access Control protocols. Review: Physical layer and its Limitations - Issues with shared media. Layer 1 involves Media Physical , Wireless Digital data bit streams that travel on media,

Layer 2 - Data Link Layer
E N D
Presentation Transcript
Layer 2 - Data Link Layer Access to Shared Media - Media Access Control protocols RD-CSY1017
Review: Physical layer and its Limitations - Issues with shared media • Layer 1 involves • Media • Physical , Wireless • Digital data • bit streams that travel on media, • Components that put signals on media, and • cables, connectors.. • Have I missed anything? • Topologies • Shared access • Any examples ? • Dedicated access • any example ? RD-CSY1017
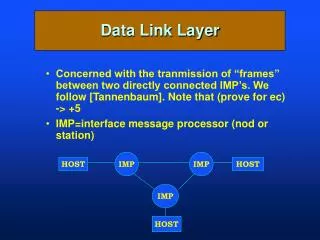
Two major issues with Physical Media • Physical layer does not have any provision to: • Issue 1: Identify • Which computer does data belong to? • Issue 2: Data Format • How is data ORGANISED and Carried on the media • bits/bytes, Frames • Issue 3: Access shared media Answer: Assign these jobs to the layer above it – the Data Link Layer RD-CSY1017
Overview • Data Link layer components • Data Frames • MAC address • Media Access and protocols • Ethernet • Ring Topology protocol • Token Ring • FDDI RD-CSY1017
Computer Two Application Application Presentation Presentation Session Session Transport Transport Network Network Data Link Data Link Physical Physical ISO 7 layer model Computer One Underlying Physical Medium RD-CSY1017
Data Link Layer Sub layers LLC (Logical Link Control) MAC (Media Access Control) • The OSI –Data Link Layer is divided into two separate sub-layers: • Media Access Control (MAC) – provides service to the layer below - physical layer • Logical Link Control (LLC) - provides services to layer above - the network layer RD-CSY1017
Every Ethernet NIC card has a unique address – called MAC address, which provides a way for computers to identify themselves. They give hosts a permanent, unique identification on a network. Example: 00-60-2F-3A-07-BC How long is the MAC address ( in terms of bytes)? Issue 1: Identify devices on network - The MAC (Media Access Control) Address RD-CSY1017
Example of MAC address 00-60-2F-3A-07-BC 48 bits (6 bytes) in length. The first 3 bytes, are administered by the IEEE (Institution of Electrical and Electronics engineers) to help identify the manufacturer. The first three bytes are called the Organizational Unique Identifier (OUI). The remaining 3 bytes comprise the interface serial number and are unique to a card The MAC Address RD-CSY1017
What is the Address on my Network Interface card (NIC)? RD-CSY1017
Issue 2: Framing data: converting bits to bit-streams • Data bits are generated by a computer that wishes to communicate • Stream of data bits or bit-stream is framedby layer 2 and transmitted on the cable (layer 1) by the Network Interface Card (NIC). • Framing provides structure to the bit-stream. • Example data frame : RD-CSY1017
Issue 3 : Accessing Shared Media - Media Access Control (MAC) Protocols • Two ways to access shared media • Random Access • Any device on the network that has data to send can access the medium, if not used • Taking turns • Each device on a network takes turns in a round-robin manner. Multi-access RD-CSY1017
Random Access - Ethernet Protocol for media access 1111 2222 3333 nnnn Abbreviated MAC Addresses 3333 1111 1111, 2222,… are MAC addresses When an Data frame is sent out all devices on the network receive it. What do they do with it? RD-CSY1017
Sending and receiving Ethernet frames Nope Hey, that’s me! Nope nnnn Abbreviated MAC Addresses 2222 1111 3333 Data Frame 3333 1111 When information (frame) is transmitted, each NIC on the shared media copies part of the transmitted frame to see if the destination address matches the MAC address on its NIC. If there is a match, the rest of the frame is copied, otherwise rest of the frame is ignored. RD-CSY1017
Issues – Random Access - Sending and receiving Ethernet frames on a bus I have data to send I have data to send X Collision! Issue: What happens when multiple computers want try to transmit at the same time? E.g., Computer 1 and 2 has data to send… Two or more computers accessing media at the same time causes data Collision Collision is detected by all computers, which then stop transmitting data Ethernet protocol CSMA/CD summarizes these steps.. RD-CSY1017
CSMA/CD (Carrier Sense Multiple Access with Collision Detection) Listens (Carrier Sense) to the network’s shared media to see if any other users are “on the line” by trying to sense a neutral electrical signal or carrier. If no transmission is sensed, then multiple accessallowsanyone onto the media without any further permission required. If two PCs detect a neutral signal and access the shared media at the exact same time, a collision occurs and is detected. RD-CSY1017
“Taking Turns” MAC protocols • Which topology is this ? • Taking turns MAC protocols need a permission to transfer data on network • Permission is given in the form of a control token (T), which ispassed from one computer to next in a round-robin fashion • Token is short, reserved frame that cannot appear in data • There is only one token, so only one computer can transmit at a time RD-CSY1017
Transmission around a token ring network • When a computer wants to transmit, it waits for the token • After it acquires the token, it can send data for the preset time. • After preset time, computer transmits token on ring • Next computer ready to transmit receives token and then transmits • If no computer is ready to transmit data, token circulates around ring RD-CSY1017
Protocols using ring topology • IBM Token Ring • Now obsolete • Data transfer rate upto16Mbps • Fibre Distributed Data Interconnect (FDDI) • Uses ring topology • Uses fibre optics cable between stations • Transmits data at 100Mbps • Uses pairs of fibres to form two concentric rings to provide fault tolerance RD-CSY1017
IEEE 802.x series standards are defined for Layer 2 (Data Link Layer) protocols for media access. Two Popular standards for local area network are: Ethernet IEEE 802.3 - Wired network IEEE 802.11 – Wireless network Token Ring IEEE 802.5 Data Link Layer Components IEEE 802.x Standards for Media Access Logical Link Control (LLC) Ethernet Token Ring Media Access Control (MAC) Protocols RD-CSY1017
Bringing it all together… • Let’s pause here for a moment and bring the following together: • What is the data entity at layer 2 called ? • W hat is role of MAC address in data communication? • Which protocols of media access are probabilistic/ deterministic? • CSMA/CD • Token Ring RD-CSY1017