Cloud Computing Services Overview
Cloud Computing Services Overview. Arizona State Capital Chapter of NIGP 2014 Regional Conference October 16, 2014 Presented by: Brian Walsh and Michael Echols, Maricopa County. CLOUD COMPUTING AGENDA. What is Cloud Computing? Cloud Computing Architecture Types of Cloud Computing

Cloud Computing Services Overview
E N D
Presentation Transcript
Cloud Computing Services Overview Arizona State Capital Chapter of NIGP 2014 Regional Conference October 16, 2014 Presented by: Brian Walsh and Michael Echols, Maricopa County
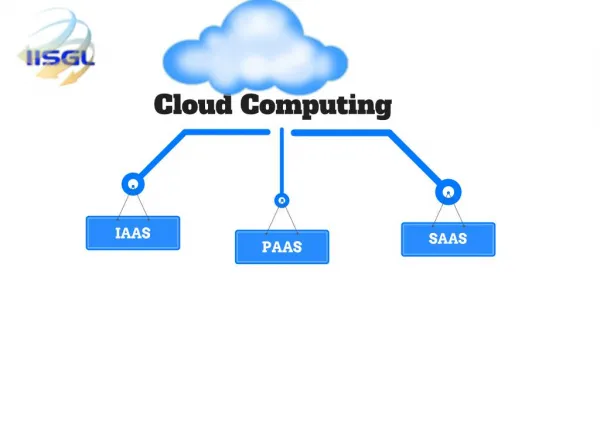
CLOUD COMPUTINGAGENDA What is Cloud Computing? Cloud Computing Architecture Types of Cloud Computing What is a Data Center? Is Cloud Computing for you? Cloud Computing Case studies Cyber Security and Breaches Cyber Security Insurance What is the role of Procurement? Questions
CLOUD COMPUTING? Source: www.evolven.com
What is Cloud Computing? Cloud computing is typically defined as a type of computing that relies on sharing computing resources rather than having local servers or personal devices to handle applications. In cloud computing, the word cloud (also phrased as "the cloud") is used as a metaphor for "the Internet," so the phrase cloud computing means "a type of Internet-based computing," where different services — such as servers, storage and applications — are delivered to an organization's computers and devices through the Internet. Cloud computing is comparable to grid computing, a type of computing where unused processing cycles of all computers in a network are harnessed to solve problems too intensive for any stand-alone machine. Source: www.webopedia.com
Cloud Computing Architecture Source: www.wikipedia.com
Types of Cloud Computing Hybrid Cloud
Data Centers Data Center Types What is a Data Center? Data centers are physical or virtual infrastructure used by enterprises to house computer, server and networking systems and components for the company's information technology (IT) needs, which typically involve storing, processing and serving large amounts of mission-critical data to clients in a client/server architecture. A data center often requires extensive redundant or backup power supply systems, cooling systems, redundant networking connections and policy-based security systems for running the enterprise's core applications. A data center is classified as a Tier I-IV based on established industry infrastructure design and function standards by the National Institute of Standards and Technology (NIST) or the “Uptime Institute”. Source: www.webopedia.com
The Future of the Cloud Cloud Vision - Access to any service, anytime, anywhere, from any device with limited overhead. Source: Silicon ANGLE “20 cloud computing statistics every CIO should know”
Advantages of the Cloud 60% of Cloud Users reported Capital Cost Reductions
Disadvantages of the Cloud Source: www.sbinfocanada.about.com
US Department of the Army • Challenge • The U.S. Army Experience Center needed a flexible, extendable and customizable recruitment tracking platform to track prospective recruits. • Solution • Move to a cloud environment that permits a 360 degree community outreach and relationship management approach. • Result • Costs down to $8M for full licensing from $83M • 33% productivity gain • 30 times higher response rates • Twitter, Facebook integration • Geo-location and contact data in the field via iPhone and Blackberry • Visitor and user surveys for instant information • Massive email campaign capabilities Source: cloud.cio.gov
US Department of Labor Relations Authority • Challenge • The Federal Labor Relation Authority’s decade-old, off the shelf case management system no longer met the agency’s needs and was financially unsupportable. • Solution • The agency migrated to a cloud-based Software-as-a-Service case management system that allows users the flexibility to monitor case activity anytime, anywhere. • Results • 88% reduction in total cost of ownership over a five year period • Eliminated up-front licensing cost of $273,000 • Reduced annual maintenance from $77,000 to $16,800 • Eliminated all hardware acquisition costs • Secure access from any Internet connection • Ability to operate and access case information from any location in the world, supporting the virtual enterprise Source: cloud.cio.gov
US Department of Treasury • Challenge • Replace the hosting service used to run the Bureau of Engraving and Printing’s public-facing website and eCommerce store with one that has equivalent capabilities and can improve service metrics. • Solution • Used SaaS cloud-based services to replace both the public-facing webpage and the eCommerce storefront. • Results • Reduced infrastructure costs from $800,000 to $1,550 • Eliminated transaction fees • Improved wait time and accessibility • Eliminated coding requirements • Faster deployment Source: cloud.cio.gov
Apple iCloud Breach • What Happened? • Apple iCloud Celebrity User Accounts were allegedly accessed by unauthorized personnel, which resulted in the loss and exposure of personal photos. • Why did this occur? • Hackers exploited a vulnerability that allowed them to “Brute Force Attack,” accounts’ passwords • How did Apple respond? • Corrected the vulnerability and took other measures to mitigate future risk. Source: InformationWeek “Apple iCloud Hack’s Other Victim: Cloud Trust”
Sony PlayStation Breach • An "illegal and unauthorized person" obtained people's names, addresses, email address, birth dates, usernames, passwords, logins, security questions and possibly credit card numbers of more than 77 million users. • Why did this occur? • Sony did not pay enough attention to security during the development of this platform. • How did Sony Respond? • Shutdown online PlayStation services for an extended period of time. • Hired an outside recognized firm to investigate and correct the issues that led to the breach. Source: Reuters “Sony PlayStation suffers massive data breach”
How might a breach occur? Typical Malware will do the following:
Cloud Risk Mitigation 1,367 Confirmed and Reported Data Breaches in 2013 63,437 Confirmed Cyber Security Incidents in 2013 Source: Verizon 2014 Data Breach Investigations Report
Cyber Security Insurance • Cyber security insurance is designed to mitigate losses from a variety of cyber incidents, including data breaches, network damage, and cyber extortion • Market-driven way of increasing cyber security posture • Helps to reduce the number of successful cyber attacks by promoting widespread adoption of preventative measures; • Encourages the implementation of best practices by basing premiums on an insured’s level of self-protection • Limits the level of losses that companies face following a cyber attack. • Many companies nevertheless forego cyber security insurance for the following reasons; • Perception of high cost • Lack of awareness about what it covers • Uncertainty that they’ll suffer a cyber attack as just some reasons for their decision
Contract Review Checklist • Service model • Risk factors • Pricing • Security controls and reports • Data assurances • Data conversion • Governing law • Service level agreement (SLA) • Contact information (24x7)
Contract Review Checklist Cont’d • Outsourced services • Disaster recovery • Mergers and acquisitions • Site inspections • Warranty • Liability • Compliance with laws-PCI, HIPPAA, CJIS, etc. • Professional services • Contract renewal and termination
Questions • Brian Walsh, Senior Procurement Officer, 602-506-3243 • Office of Procurement Services • walshb@mail.maricopa.gov • Michael Echols, Chief Information Security Officer, 602-506-5798 • Office of Enterprise Technology • echolsm@mail.maricopa.gov