Course Overview
18739A: Foundations of Security and Privacy. Course Overview. Anupam Datta CMU Fall 2009. Course Staff. Instructor: Anupam Datta Office: CIC 2118 Email: danupam@cmu.edu Office hours: Tue 4-5PM, Thur 5-6PM TA: Arunesh Sinha Office: CIC 2127C Email: aruneshs@cmu.edu

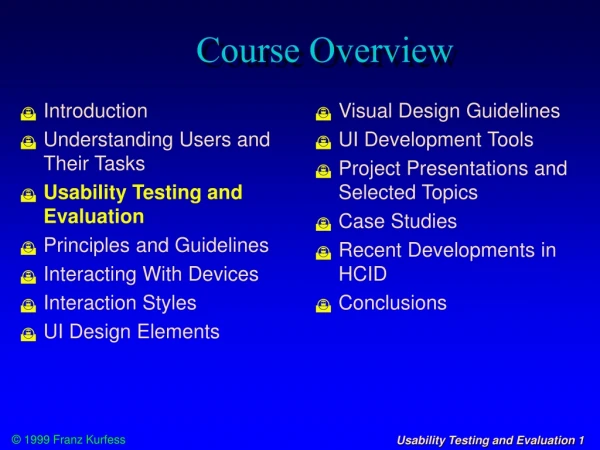
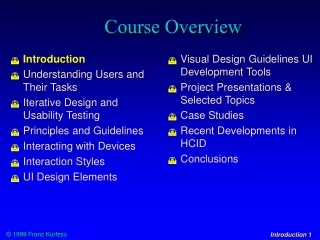
Course Overview
E N D
Presentation Transcript
18739A: Foundations of Security and Privacy Course Overview Anupam Datta CMU Fall 2009
Course Staff • Instructor: Anupam Datta • Office: CIC 2118 • Email: danupam@cmu.edu • Office hours: Tue 4-5PM, Thur 5-6PM • TA: Arunesh Sinha • Office: CIC 2127C • Email: aruneshs@cmu.edu • Office hours: MF 1-2PM
A Real-World Interaction (Protocol) • Depositing a check at a bank • Alice receives check from Bob • Alice hands over check to teller Tyra • Tyra sends check to Bob’s bank • Bob’s bank verifies Bob’s signature • Money transferred from Bob’s account to Alice’s account
Questions for the class • What are the desired security properties? • Authentication : Bob must have written out the check for Alice • Integrity: The check has not been modified by anyone other than Bob • Non-repudiation: Bob cannot deny that he wrote a check if in fact he did • Authorization: Is Bob authorized to withdraw $X in funds? • Privacy: Bob’s bank should not share Bob’s financial information with other companies • What can an adversary do to try to break the protocol? • Forge check, steal an empty check, forge signature, edit check • What mechanisms are used to achieve these properties? • Unforgeable signatures, uniqueness of handwriting, indelible ink, tamper evident paper (unauthenticated modification in body of check is detectable) Now throw the internet and software systems into the mix!
Functional Correctness vs. Security • Program or System Functional Correctness • Program satisfies specification • For reasonable input, get reasonable output • Program or System Security • Program properties preserved in face of attack • For unreasonable input, output is not completely disastrous • Main difference • Active interference from adversary
Plan for Today • Course logistics • Overview of topics and learning outcomes • A quick tour of cryptographic primitives
Logistics (1) • Lectures: Tuesday & Thursday, 10:30-11:50AM, in SH 208 • Recitation: Friday, 4-4:50PM, in SH 208 • Web page: http://www.ece.cmu.edu/~ece739/ • Course blackboard (linked from web page) • Course work and grading: • Homework (40%) – 4 x 10% • Midterm exam(10%) – take home • End term exam (10%) – take home • Course project (30%) • Class participation (10%)
Logistics (2) • Recitation: • Friday, 4-4:50PM, in SH 208 • Supplements topics discussed in class • TA will discuss and demo various security analysis tools • TA will also elaborate on examples and proof techniques discussed in class • Should be useful for projects and homeworks • First recitation this Friday
Logistics (3) • Course Project: • Teams of 2 (form team by end of week) • Project proposal: 1-2 pages (Due: Oct 8) • Models/code (Due: Dec 1) • Written report: 5-10 pages (Due: Dec 1) • Final presentation in class (Dec 1,3) • Project suggestions later in the lecture or pick your own
Logistics (4) Collaboration policy on homeworks and exams: • You are allowed to discuss solutions to written homework problems with other students in the class, but are required to write out solutions independently and to acknowledge any collaboration or other source. For programming/tools homeworks, you can work in groups of 2. • You are required to work on the take home exams on your own. No collaboration is allowed. CMU Computing Policy CMU Policy on Cheating
Prerequisites • An introductory course in computer security such as 18-487, 18-630, or18-730 is recommended, but not required. • If in doubt, please talk to me after class • Quick class poll
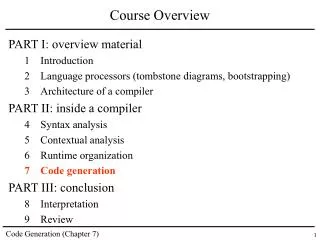
Four Broad Topics • Security Protocols • Access Control • Privacy • Software Security
Secure communicationusing SSL/TLS SSL uses cryptography to protect data confidentiality and integrity, and guarantee entity authentication
Many Protocols • Authentication • Kerberos • Key Exchange • SSL/TLS handshake, IKE, JFK, IKEv2, • Wireless and mobile computing • Mobile IP, WEP, 802.11i • Electronic commerce • Contract signing, SET, electronic cash • Anonymous communication • Dining cryptographers, mixnets, crowds, onion routing Huge practical impact, well-developed theory! Protocol Repositories: http://www.lsv.ens-cachan.fr/spore/, http://www.avispa-project.org/library
Learning Outcomes (1) • Security properties • What does confidentiality, integrity, authentication, denial of service, fairness, anonymity mean? • Adversary model • What are the adversary’s capabilities – snoop on the network, inject traffic, do complicated math, jam network, observe timing effects,…? • Protocol design • How can cryptographic primitives be combined to achieve security in the presence of such adversaries? • What kind of mistakes do protocol designers make? • Protocol analysis • How can we automatically find attacks on protocols? • How can we prove security properties of protocols?
Possible Project Topics (1) • Analysis of protocols using existing methods/tools • Electronic voting protocols • Anonymous communication protocols • Protocols for the emerging smart electric grid • Mobility protocols, e.g. Mobile IPv6 • “Next generation” internet protocols (accountability) • Develop/extend a protocol analysis method/tool • Automated prover for PCL (discussed later in class) • Extended the ASPIER tool for protocol implementation verification • Sample projects from protocols course at Stanford • http://www.stanford.edu/class/cs259/projects.htm
Before we look at other topics • A quick (de)tour of cryptography
Access Control • Goal: Control which principals have access to which objects using a reference monitor that mediates access • Examples: File systems, memory protection in OS, virtual machines, access to physical spaces, digital libraries, web browsers CMU
Distributed Access Control • Goal: Flexible and scalable access control in large-scale, open, distributed systems • Challenges: • No central administration, each service makes its own access control decision • Access control policy is distributed
Distributed Access Control Example EPub Alice Grants access to university students Trusts universities to certify students Trusts ABU to certify universities Alice is a student StateU is a university StateU ABU
Learning Outcomes (2) • Access control concepts and foundations • Principals, resources, reference monitor • Policy expressed using access control matrix or logic • Centralized and distributed policies • Access control in practice • Mechanisms in current OS, hypervisors • Mechanisms based on checking proofs in an authorization logic (centralized and distributed) • Case studies of the Grey system (used in CIC for access to physical spaces) and the Taos OS (original application for the seminal work on the Lampson et al authorization logic)
Possible Project Topics (2) • Access control in web browsers • Formal study of access control policies and mechanisms in modern web browsers • Access control in hypervisors • Formal analysis of the TrustVisor system being developed at CMU, or of Xen’s protection mechanisms • Adding flexible access control to svn
Data Privacy • Huge amount of personal information available to various organizations • Hospitals, financial institutions, websites, universities, census bureau, social networks • Information shared within and across organizational boundaries to enable useful tasks to be completed • Personal health information has to be shared to enable diagnosis, treatment, billing • Census bureau releases aggregate statistics
Learning Outcomes (3) • What is privacy? • Philosophical studies (Gavison, Contextual Integrity) • Database privacy definitions (differential privacy) • Policy expression in languages (P3P, Logic of Privacy) • Privacy regulations in the US, e.g., HIPAA, GLBA • How is privacy compromised? • Attacks on AOL & Netflix data sets, cases of HIPAA violation, end-user understanding of privacy promises • How can we enforce privacy? • Achieving differential privacy • Enforcing policies in the logic of privacy (the need for auditing)
Possible Project Topics (3) • Formalize a privacy regulation in a policy language • Example: GLBA in the logic of privacy • Develop a system for enforcing privacy policies • Example: For the logic of privacy
Software Insecurity Root causes of security vulnerabilities in software • Language does not protect the abstractions it provides • Example: buffer overflow attacks are possible because C does not protect the array abstraction; not possible in Java • Language does not provide high-level abstractions for developing security applications • Example: Java does not provide abstractions for writing applications that enforce access or information flow control; similar issue for Javascript and web applications insecurity
Learning outcomes (4) • Understanding of how type systems can be used to improve software security • Protecting language abstractions • Cyclone: Memory safe dialect of C, i.e. no buffer overflow attacks • Providing language abstractions • Information flow control and the Volpano-Smith-Irvine type system
Possible Project Topic (4) • Develop a language for secure web programming • Not recommended unless you have significant experience with typed programming languages
Why study Foundations of Security? Our discipline of computer science seems to be one in which theory and practice are more intimately related than in any other field.....you can’t get very far in practical work without abstract theories that permit you to think at a higher level, and at the same time theoretical work becomes dead if it doesn’t receive fresh inspiration from practical problems in the “real world”. Don Knuth, Professor Emeritus of The Art of Computer Programming at Stanford University
5 Turing Award winning ideas! • Rivest-Shamir-Adleman: RSA public key cryptosystem • Lampson: Foundations of access control • Clarke-Emerson-Sistla: Model-checking systems • Hoare: Axiomatic reasoning about programs • Milner: Theory of concurrency