EHR Privacy & Security
Introduction and Welcome: Nancie McAnaugh, MSW Center for Health Policy MO HIT Assistance Center Presenter: Rebecca Thurmond Fowler System Security Analyst-Principal University of Missouri Division of Information Technology. EHR Privacy & Security . MO HIT Assistance Center.

EHR Privacy & Security
E N D
Presentation Transcript
Introduction and Welcome: Nancie McAnaugh, MSWCenter for Health PolicyMO HIT Assistance CenterPresenter: Rebecca Thurmond FowlerSystem Security Analyst-PrincipalUniversity of Missouri Division of Information Technology EHR Privacy & Security
MO HIT Assistance Center • Missouri’s Federally-designated • Regional Extension Center • University of Missouri: • Department of Health Management and Informatics • Center for Health Policy • Department of Family and Community Medicine • Missouri School of Journalism • Partners: • EHR Pathway • Hospital Industry Data Institute (Critical Access Hospitals) • Missouri Primary Care Association • Missouri Telehealth Network • Primaris
Vision Assist Missouri's health care providers in using electronic health records to improve the access and quality of health services; to reduce inefficiencies and avoidable costs; and to optimize the health outcomes of Missourians
What is our role? • For providers who do not have a certified EHR system - We help you choose and implement one in your office • For providers who already have a system - We help eligible providers meet the Medicare or Medicaid criteria for incentive payments
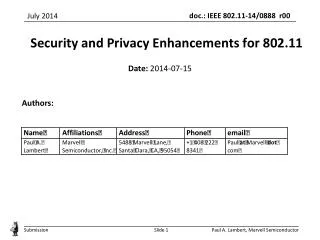
Disclosures Cerner and the University of Missouri Health System have an independent strategic alliance to provide unique support for the Tiger Institute for Health Innovation, a collaborative venture to promote innovative health care solutions to drive down cost and dramatically increase quality of care for the state of Missouri. The Missouri Health Information Technology Assistance Center at the University of Missouri, however, is vendor neutral in its support of the adoption and implementation of EMRs by health care providers in Missouri as they move toward meaningful use. This regional extension center is funded through an award from the Office of the National Coordinator for Health Information Technology, Department of Health and Human Services Award Number 90RC0039/01
Information Security Risk Assessment Process Becky Thurmond Fowler System Security Analyst –Principal Division of IT, University of Missouri
Introduction • Risk Assessment Process • Risk Assessment Cheat Sheet • Moving Forward… • Questions? Agenda
Increased focus on security & privacy in society • Federal and state laws and regulations • Heard of a little thing called HIPAA? Why Are We Doing This?
Covered Entities (CE’s) and Business Associates of CE’s must comply with the HIPAA Security Rule, including: • Due diligence • Good business practices • Analysis of risk • Creation of appropriate safeguards • Documentation HIPAA
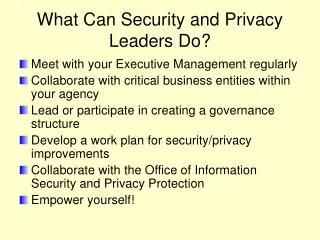
Identify key relevant systems • Conduct a risk assessment • Implement a risk management program • Acquire IT systems and services as necessary • Create and deploy policies and procedures • Develop and implement a sanction policy • Develop and deploy the information system activity review process The Process – An Overview
Identify key relevant systems • Categorize the sensitivity of the data • Which information systems are involved? • Perform inventory – who owns? • Configuration management and documentation Risk Assessment Process
Conduct a risk assessment • Variety of checklists and procedures to help you through the process • Document what you’re doing, do what you’re documenting! • Answers to questions raised in your risk assessment can help you determine where your data is vulnerable Risk Assessment Process
Section 1: Organizational Information • Definition of Personally Identifiable Information (PII) • What kind of PII does your organization have, and what do you do with it? Risk Assessment Cheat Sheet
Section II: Access to Work Area • Objective: To control unauthorized access to work areas where confidential or sensitive information is held or utilized Risk Assessment Cheat Sheet
Section III: Access to Work Equipment/Information/Materials • Objective: To control unauthorized access to confidential or sensitive materials and work equipment Risk Assessment Cheat Sheet
Section IV: Information Systems Security & Access • Objective: To appropriately manage confidential and sensitive electronic files and IT resources Risk Assessment Cheat Sheet
Section IV: (continued) • This section will require close work with your Information Technology folks. • Technical reviews • Application and server level controls • Networking • Disaster Recovery and Business Continuity Risk Assessment Cheat Sheet
Section V: Access to Waste Materials • Objective: To ensure paper and electronic files and media are properly destroyed when appropriate Risk Assessment Cheat Sheet
Section VI: Organizational Procedures & Employee Training • Objective: To set expectations and raise awareness among employees who handle confidential and sensitive information Risk Assessment Cheat Sheet
Implement Risk Management program • Thoughtfully choose security measures to reduce risks. • Qualitative vs. quantitative • Looking to: • Reduce risk • Transfer risk • Accept risk • Avoid risk Risk Assessment Process
Acquire IT systems and services as necessary • Security isn’t free! What is your desired end result? Risk Assessment Process
Create and deploy policies and procedures • Develop and implement a sanction policy • Develop and deploy the information system activity review process (rinse & repeat) Risk Assessment Process
Questions? Thank you! Q & A
Your Phone Line is Now Open! • If you do not wish to ask a question, please press * 6 to mute your phone.
Upcoming Webinars: Meaningful Use & Physician Quality Reporting System (PQRS) Wednesday, November 9th Presenter: Sandra Pogones Program Manager Primaris
MO HIT Assistance Center Now Serves Large Practices & Specialists • Contact MO HIT Assistance Center for details and pricing
For More Information: • Website: http://ehrhelp.missouri.edu • E-Mail: • EHRhelp@missouri.edu • Phone: • 1-877-882-9933