Encryption/Decryption system Project Characterization
By: Shay Amosi & Jasmin Amitai Mentor: Mony Orbach Spring 2013. Encryption/Decryption system Project Characterization. Our challenge. Today, encryption is used in many fields and consuming significant processor resources, therefore causes a decrease in performance.

Encryption/Decryption system Project Characterization
E N D
Presentation Transcript
By: Shay Amosi & JasminAmitai Mentor: MonyOrbach Spring 2013 Encryption/Decryption systemProject Characterization
Our challenge Today, encryption is used in many fields and consuming significant processor resources, therefore causes a decrease in performance. We can find various encryption uses: sites such as FACEBOOK and Bank accounts, wireless networks, digitally signed messages, military communication equipments and so on. Because encryption is implemented by a computer processor, it consumes substantial resources which could have channeled for other programs, and the stronger the encryption is, the greater need of CPU resources. Our goal is to find a way to still maintain a strong encryption, however, not detract from the overall computer performance.
Our project • Our project goal is to create a hardware system that encrypts the data quickly and efficiently. • The system will simulate real-time encryption between a PC and USB using FPGA.
Morse Code? There are two common approaches for encryption today: Symmetric encryption Asymmetric encryption
Symmetric encryption Symmetric encryption is the process of converting readable data to unreadable format and converting it back to readable format using the same key (*). Symmetric encryption algorithms use the same key for encryption and decryption. The key must be exchangedso that both the data sender and the data recipient can access the plaintext data. The plaintext (Readable Text) is converted to cipher-text (unreadable text) using a key and at the receiving side the same key is used to covert back the cipher-text to plaintext.
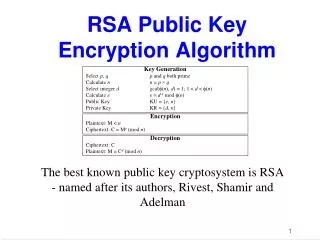
Asymmetric encryption Asymmetric encryption increases the security of the encryption process by utilizing two separate but mathematically related keys known as a public key and a private key. Asymmetric encryption algorithms use a mathematically related key pair for encryption and decryption. The private key is possessed only by the user or computer that generates the key pair. The public key can be distributed to any person who wishes to send encrypted data to the private key holder. It is impossible to compute the private key if you know the public key.
Certificate authority • Digital signature • Key exchange
Selecting Encryption Considerations and Requirements: Encryption speed (Saves time) Encryption strength Efficiency Integrability \ Our Vision...
Twofish • The Twofish is a symmetric key 128-bit Block Feistel network. • Twofish can work with variable key length from 128 to 256 bits. • Twofishexhibits fast and versatile performance across most platforms. • The Twofish structure offers a great deal of flexibility in terms of space versus speed tradeoffs.
The Twofishalgorithn The TwofishConsists of the following steps: • The plaintext is split into 4 words • Input Whitening • 16 rounds of the F function • Output Whitening
Working environment Hardware: DE2 Development and Education Board Altera’s FPGA Cyclon II Hardware description language: VHDL Synthesis and Simulation: • ModelSim • Quartus
Feistel network Is symmetric structure used to build blocks ciphers. Feistel network is built so that it divides the visible text into two parts, right and left. Each iteration step function is enabled on one side and at the end the two parts connect.The next iteration exchanging between the parts so that the output from the right side becomes the input to the left and vice versa. Back
Whitening operation Whitening operation include XOR of input and output with sub-keys. Back
F function Contains the following operations: • Fixed left rotation by 8 bytes • Key-dependent s-boxes • MDS matrices • Pseudo-Hadmard Transform (PHT) BackMore
S-boxes S-box is a basic component of symmetric key algorithms which preforms substitution. In general S-box take input bit and transform them into output bites .(the number of the input bitesdoes not necessarily equal to the number of the output bites ). Back
MDS Matrices MDS-Maximum Distance Separable is a matrix representing a function with certain properties that have useful applications in cryptography. Back
Pseudo-Hadmard Transform (PHT) Given two inputs, a and b, the n bit PHT is: Back
F Function • The two words on the left are used as input for the h function ,when one of them is rotated by 8 bits first. • The h function consist 4 key-depedent s-boxes, followed by linear mixing step based on MDS matrix • The output of the 2 h function are combined using PHT, and two round key words are added. • The third word is XORed with the first output of F and then roted.
F Function • The fourth word is rotted and then XORed with the second output of the F function • Finally, the tow half are exchanged. Back