VMM Based Rootkit Detection on Android
VMM Based Rootkit Detection on Android. Class Presentation Pete Bohman, Adam Kunk , Erik Shaw. Motivation. Smartphone malware on the rise Increased security implications (compared to PC) Sensitive information: GPS, contacts, SMS, c all log Constantly connected

VMM Based Rootkit Detection on Android
E N D
Presentation Transcript
VMM Based Rootkit Detection on Android Class Presentation Pete Bohman, Adam Kunk, Erik Shaw
Motivation • Smartphone malware on the rise • Increased security implications (compared to PC) • Sensitive information: GPS, contacts, SMS, call log • Constantly connected • Naïve users, limited use of Anti Virus The Increase of Mobile Malware Variants (2004 – 2010)
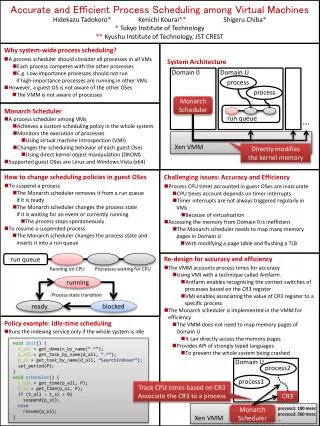
Defensive Rootkit Approaches • User mode rootkits • Process infection, binary patching, lib hooks • User mode integrity checkers • tripwire, chkrootkit, rkthunter, AV scanner • Kernel mode rootkits • malicious device drivers and lkms • sys call hooking, kernel data structure manipulation • Kernel level inspection • behavioral analysis, data structure integrity checkers, hook detection • But… Any kernel level inspection mechanisms can be subverted by kernel level rootkits
Our Approach Android Software Stack • Two Pronged • KM security mechanisms • System call integrity checks • Hidden process detection • Android capability table • VMM inspection • Ensures integrity of static KM • Isolated from host OS • We exercise a “layer-below” level of security in which we establish trust beneath the kernel
Solution Preview (Delete Slide) Android Software Stack Kernel module implements security mechanisms Android VMM ensures integrity of static kernel module
Overview • Design • VMM Design • Protected KM Design • Implementation • Results • Demo Presentation • Conclusion • Q&A
VMM Interface Design Application Framework Android VMM Libraries and Runtime Linux Kernel 4. Invoke KM Trusted KM <ISR> 2. Validate Protected KM 3. Raise Monitor Interrupt 1. Hardware Timer Interrupt Hardware (Emulator)
Protection KM Design Maps Contacts SMS App … Application Framework Content Provider Location Provider Activity Manager Malicious Native Application Libraries and Runtime System Calls Open Socket Read GPS SQL Query Linux Kernel Trusted KM System Call Whitelist Original Sys Call Table SysCall Table Open
Protection KM Design Android VMM Libraries and Runtime System Calls Linux Kernel Trusted KM System Call Whitelist Original Sys Call Table Malicious LKM SysCall Table Z X Y <ISR> Monitor Interrupt
Implementation • Implemented VMM security functionality in an emulated hardware device within QEMU • Protected KM data and text compiled into QEMU emulator (VMM) Kernel Image Linux Kernel Source with Protection KM Compilation Protected Text Sect. Protected Data Sect. QEMU Emulator(VMM) QEMU Emulator (VMM) Compilation Protected Text Protected Data
Implementation • Malicious native mode application • Read contacts database • Read GPS location • Ex-filled data using sockets • Malicious LKM • Intercept read system calls to access GPS location
Results • We are able to detect/correct modifications to the sys_call_table • We are able to prevent malicious access to sensitive resources • TODO Mention Malicious App and LKM • TODO: (Insert link to demo)
Conclusion • Layer Below Protection • Security of the Linux kernel must be rooted in a layer below the kernel • Code contained solely in the kernel is subject to any kernel-level attack • Sensitive Resource Protection • Android mobile phones contain lots of sensitive information that must be protected
Kernel Image Linux Kernel Source with Protection KM Compilation Protected Text Sect. Protected Data Sect. QEMU Emulator(VMM) QEMU Emulator (VMM) Compilation Protected Text Protected Data
Problem Statement • Rootkit detection and prevention on the Android platform with specific regards to the sensitive resources Android provides. • Kapersky 2011: 1046 unique malware strains targeting mobile platforms • Android platform built on Linux Kernel, a well known target. • Sensitive information on smart phones • GPS, contacts, text messages, call log