Group-based Source Authentication in VANETs
Group-based Source Authentication in VANETs. You Lu, Biao Zhou, Fei Jia, Mario Gerla UCLA {youlu, zhb, feijia, gerla}@cs.ucla.edu. VANET slide. VANET Scenario. The problem: authentication. VANET broadcast messages: Beacons for safe driving, surveillance, situation etc

Group-based Source Authentication in VANETs
E N D
Presentation Transcript
Group-based Source Authentication in VANETs You Lu, Biao Zhou, Fei Jia, Mario Gerla UCLA {youlu, zhb, feijia, gerla}@cs.ucla.edu
VANET slide • VANET Scenario
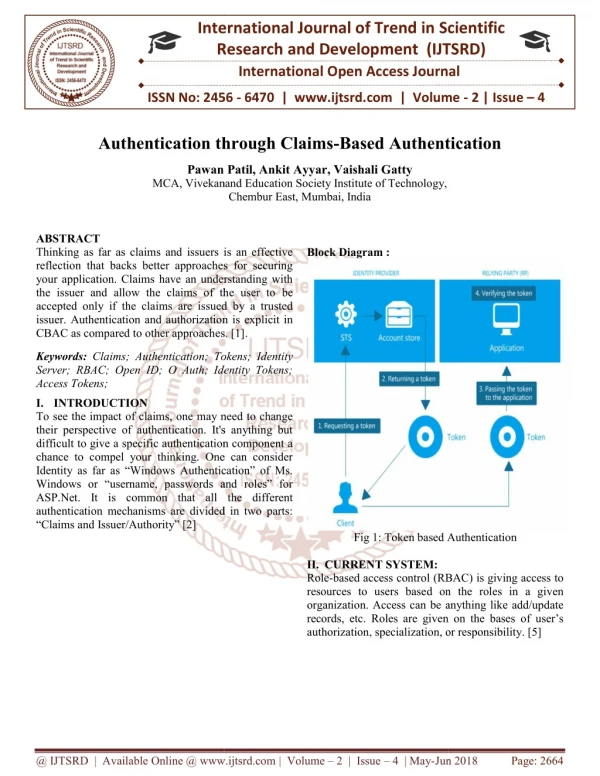
The problem: authentication • VANET broadcast messages: • Beacons for safe driving, surveillance, situation etc • Problem: malicious sources can generate bogus messages • Attack models • Critical issue we address here: • Sender authentication (within group) • Not addressed here: • Non repudiation • Privacy protection, • Secret delivery to selected group (e.g. police agents, taxi cabs, coalition members), etc
Existing Authent. solutions • PKI – a bit too expensive • TESLA – cheaper, but ..slow (Toyota et al)
TESLA: One Way Hash Chain • In TESLA a source generate a one way chain of length L by randomly picking the last element SL of the chain S and by repeatedly applying the Hash function F( ) to get the next values one after the other. • After creating the one way chain, the source stamps each packet with the chain values in reverse order. The receiver can verify Si+1 only after it receives Si from the source. • At this time, the receiver also verifies the source authenticity
TESLA overview (cont) • TESLA (Time efficient stream loss tolerant authentication) • Assumption: 2- time slot delay in authentication • Packet P1 received in slot 5; K5 received in slot 7 • Authentication of P1: • Verify K5 from K4 pr K3 (explain how) • MAC(K5, P1) = Verify MAC • Pros: Robust to packet loss; Data all in plain text. • Con: delayed authentication.
Exploit Group Motion to reduce latency • Group Scenario • Nodes move in groups • Each group is a closed broadcast group: • Military peace keeping patrols; police agents in a mission; presidential motorcade. • Group nodes acquire SECRET initial group attribute, and initial mobility counter before joining • Our Goal: reduce the key disclosure delay in group broadcast
Group-based Source Authentication (GSA) • Basic Idea:
Group-based Source Authentication (GSA) • Protocol Design • How to define a group? • Group Identifier, such as group name, group ID… • Dynamic Attributes, such location intersection, group speed etc Must be better explained • Initial Group property is shared by the same group. • How to ensure disclosure key cannot be captured and replayed by attacker? • Encrypt the disclosure key with secret group ID. • External nodes cannot get K7, • secret group ID never transmitted in plain text. • Proactively updated dynamic attributed for extra security Encrypt (K7, secret group ID)
Step 1: Group Authentication • Group Authentication Phase • The sender broadcasts nonce with own GID and requests receivers in the group to authenticate themselves • Each Receiver R uses individual TESLA reverse hash chain. Receiver Packet: Time interval 3 • After key disclosure delay period, each receiver sends K3 • Sender checks if R is in the same group as itself. Same Group member • Now all group members are authenticated and “in synch” • Periodically authenticate group membership after timeout
Step 2: Group-based Source Authentication (GSA) • Data Transfer Phase • Inter-group • Use conventional TESLA-like scheme (large latency) • Intra-group • Instant KEY disclosure • Packet sent at time i: • Group members: • decrypt K_i usinggroup_property key • verify Packet_i immediately using decrypted K_i.
Experiments • Average End-to-End Latency: • Testbed: 7 Laptops with Intel M740 processor, 1.73 Ghz • Number of active GSA Sessions: from 5 to 500
Experiments (cont) • CPU and Memory Usage:
Experiments (cont) • MAC Average Computing Time:
Experiments (cont) • Performance Comparison of GSA and TESLA for single session: • GSA guarantees efficient, safe delivery of vehicular alarms within a group
Conclusions • GSA is applicable in the following scenarios: • Nodes move in group • Group nodes know initial group secret and initial mobility attributes • Incremental addition of attributes supported • Experiment results: • In TESLA, large latency due to key disclosure delay • GSA reduces key disclosure delay to significant groups (e.g., vehicles in the same convoy) • Future work: • Dynamic Group ID certificates to short lived urban vehicle platoons • Safety improvement resulting from of reduced latency • Secret content to selected groups (e.g., police) • Privacy preservation
Thanks Q & A