IT Vendor Management Strategies
IT Vendor Management Strategies. Alan Ferguson, Vice President alan.ferguson@coalfiresystems.com March 2008. Who is Coalfire?. Founded in 2001, with offices in Denver, Seattle and NYC with over 30 full time IT Auditors. Clients include Fortune 100, retail, government, education,

IT Vendor Management Strategies
E N D
Presentation Transcript
IT Vendor Management Strategies Alan Ferguson, Vice President alan.ferguson@coalfiresystems.com March 2008
Who is Coalfire? Founded in 2001, with offices in Denver, Seattle and NYC with over 30 full time IT Auditors Clients include Fortune 100, retail, government, education, financial, healthcare, Law Firm and manufacturing Security, Governance, Compliance Management, Audit – GLBA, SOX, PCI, HIPAA, SAS70 & Government IT Governance and Compliance Management Practice areas: Risk and Vulnerability Assessment, E-discovery and Forensic Analysis Solutions: Policy Development, Data Classification, Logging and Monitoring, Incident Response, Etc. Application Security: PABP Certification, Code Audits, Penetration Testing, SDL Development
Compliance Overview Vendor Threats Vendor Management Overview Vendor Management Program Case Study Agenda Questions
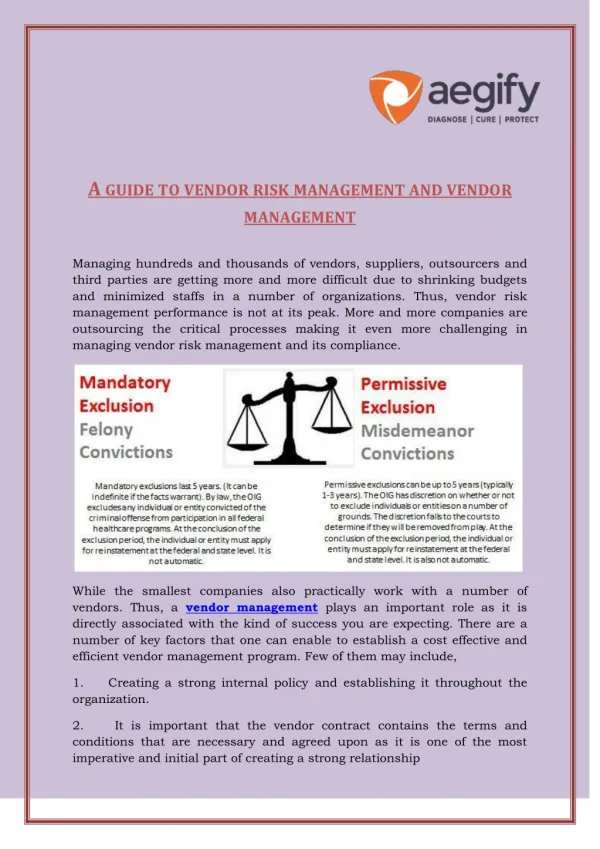
Shatter the Myth You are responsible for your vendors and service providers. • Regulations assign data protection responsibility to the data owner • Most regulations define provisions for data owners to provide oversight • Case law is more thoroughly defining data protection responsibilities
IT Governance at a Glance Risk Management Programs Critical Drivers Reduced Tolerance for Service Disruption Increasing Cyber Threats More Regulatory Requirements
Compliance Trends The Regulatory Environment Represents a New Enterprise Challenge 2000- Present 1970-1980 • COPPA • USA Patriot Act 2001 • EC Data Privacy Directive • CLERP 9 • CAN-SPAM Act • FISMA • Sarbanes Oxley (SOX) • CIPA 2002 • Basel II • NERC 1200 (2003) • CISP • Payment Card Industry (PCI) • California Individual Privacy SB1386 • Other State Privacy Laws (38) 1990-2000 • Privacy Act of 1974 • Foreign Corrupt Practice Actof 1977 • EU Data Protection • HIPAA • FDA 21CFR Part 11 • C6-Canada • GLBA 1980-1990 • Computer Security Act of 1987
State Privacy Laws Businesses must establish basic information security programs In the event of an actual or suspected security breach businesses have a legal obligation to notify impacted consumers resulting in new security requirements Businesses must proactively manage their confidential consumer information Businesses must take steps to know when their defenses have been breached Compliant infrastructures are required!
Common Theme • Vendors and Service providers introduce unique risks • The current state of vendor data security is inconsistent • Regulators have inserted vendor management as a key element for all significant data security programs • Compliance by service providers with those regulations is in the early stages (i.e. don’t expect much)
A History of Issues • Poor Controls - Wells Fargo reports a lost server with sensitive data at a marketing firm • Unsecure Applications - VISA reports that unsecure applications and services are the highest risk to cardholder data processing • Weak NDA - Choice Point sells sensitive data and gets a $10 million fine from the FTC • Poor Staff Supervision – • a rogue contractor at a level 1 merchant changes PIN Entry Devices to collect security codes • A careless firewall management firm leaves unsecured ports open to a bank network
Vendor Management Program RISK Know your vendor Aligned expectations Effective Controls Enforced PROGRAM Due Diligence Contract Terms Joint Risk Assessment Defined Standards Defined Control Responsibility Vendor Reporting Periodic Audit
Due Diligence • Service Provider capabilities aligned to business needs • Financial stability • Reference checks • Formal review and approval process • Maintain evidence of due diligence validation
Contract Terms • Acknowledge access to sensitive data • Agree to protect sensitive data • Non-Disclosure and Confidentiality Agreement (NDA) • Risk assessment and selection of controls • Specify standards • Define control responsibility • Periodic reporting of control effectiveness • Audit • Notification of breach and support of incident investigation
Risk Assessment and Control Selection • Define system data flow • Identify system responsibilities • Perform risk assessment • Select justified controls • Identify control metrics • Measure control effectiveness • Identify a roadmap to jointly mitigate risks to sensitive data
Sample Payment Processing Data Flow Where is the card holder data? Customer Production Environment POS Terminals (card present in stores and parking facilities) Web Server (card not present) Authorization Transaction Servers or Payment Gateway Transaction Record & Archive Phone, Fax, Email Admin Environment Batch Settlement • Marketing • Customer Service • Ecommerce • Phone / Fax • Gift Cards • Fraud • Accounting / Administration Application Servers Back Office & Customer Svc Data Warehouse Payment Gateway and Transaction Database Acquiring Bank Wells Fargo, BoA, Chase Document Vaults Paper records Portal Access to Reconciliation Data (Charge Back / Sales Audit)
PCI HIPAA ISO-17799 SOX GLBA Privacy Laws Unified Compliance Programs Training Sec. Doc. Security Policy Access Controls Security Arch. Design Unified IT Controls Code Review Penetration Testing NIDS/HIDS IDS Firewall Loggin
Standards Not all service providers are aware of industry or regulatory standards for data protection. The data owner must make service providers aware of standards to include: • Regulatory requirements (GLBA, HIPAA, PCI) • Industry best practices (CoBIT, FFIEC, ISO 27001, NIST, ITIL) • Company standards and policies • Audit and reporting standards (PCI, SOX, SAS 70)
Reporting Control reporting is not optional and is NOT a service provider trade secret. No news is usually bad news. • Regulatory reporting • Company oversight, required by contract • Industry reporting (SAS 70) • Breach notification • Audit support or incident investigation
2008 Remediation Program Q3 Q1 Q2 Q4 • Document the Control Environment and Test for Design Adequacy • Complete Risk Assessment • Update Policies to Mitigate Risks • Design and Deploy Technical Security Controls • Re-segment the NW – FW rules • Configuration management • Vulnerability management (remediate known vulnerabilities) • Patch management • Access Controls / ID management / 2 Factor Authentication • Enhance log collection, analysis and reporting • Expand integrity monitoring • Encryption key management • Staff Training • Add Security Considerations to SDLC for Developer Guidelines • Enhance Monitoring and Reporting • Final Test for Control Effectiveness
Case Studies • Wrong Way – Stolen ServerRight Way – Meaningful SAS70 23
Prevention vs. Response The VA laptop encryption program was reportedly valued at $6 million and could have prevented the lost data on a stolen laptop computer that cost the VA in excess of $50 million A recent Gartner study showed that preventing an incident was typically less than 4% of the cost of the incident
Getting Started • Assign a Program Manager • Identify all critical Vendors and Service Providers • Establish a process • Implement the process • Measure the process • Adjust the program
Compromised? (Consumer Notice Provisions) This What To Do If Compromised guide is intended for Visa members but similar guidelines have been published by the FBI as part of the former NIPC. A sample Incident Response Plan has been included in the CD.
Knowledge – Action = Negligence Safe Harbor Safe Harbor requires validation of compliance at the time of compromise So far, no compromised account has been compliant at the time of the incident