Diffie Hellman Key Exchange Algorithm | Cryptography And Network Security |
In this presentation on the Diffie Hellman Key Exchange Algorithm, we look at a vital cog in the area of Cryptography and Network Security in general. We will begin by learning why an efficient key exchange method was necessary and how one-way functions help us in achieving this distinction. Next, we learn about the steps needed to exchange cryptographic keys and the practical implementation of this process. Finally, we take a look at the Diffie Hellman Key Exchange algorithm.<br>

Diffie Hellman Key Exchange Algorithm | Cryptography And Network Security |
E N D
Presentation Transcript
Henry Stella
Let’s consider Henry and Stella who want to exchange messages securely using encrypted messages. Henry Stella
To be able to send encrypted messages, an encryption/decryption key must be formulated. Henry Stella
Sending this key directly makes it easy for hackers to capture it in transit.
Sending this key directly makes it easy for hackers to capture it in transit.
Sending this key directly makes it easy for hackers to capture it in transit. This is where the Diffie Hellman Key Exchange algorithm can help us in securely exchanging keys.
What Is Diffie Hellman Key Exchange? • How do One-Way Functions Work? • Steps in Key Exchange • Practical Implementation • Applications of DHKE Agenda For the Day
What Is Diffie Hellman Key Exchange? • Algorithm to securely exchange keys • Proposed in 1976 by Whitfield Diffie and Martin Hellman • Communicated over “insecure” channels • Used as a precursor to asymmetric cryptographic algorithms.
Both users must have their private colors set, and must decide on a common public color to be used.
The private colors are now combined with the mixture to find the actual secret color.
The private colors are now combined with the mixture to find the correct secret color.
The private colors are now combined with the mixture to find the correct secret color.
Since the hacker doesn’t have each user’s private color, the secret key can be used to encrypt messages safely.
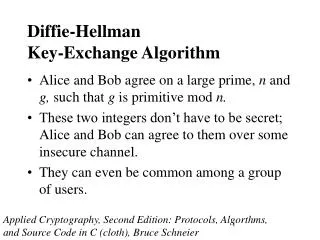
Choose q and α a. Choose a prime number q b. Select αas a primitive root of q To be a primitive root, α mod q α2 mod q α3 mod q . . . . αq-1 mod q Step 1 < q (1,2,3,4….,q-1)
Deriving the Key Pair Step 1 Assume private key = Xa where Xa < q Assume private key = Xb where Xb < q Step 2 Public key (Ya) becomes: Public key (Yb) becomes: Yb = αxb mod q Ya = αxa mod q Key pair : {Xb,Yb} Key pair : {Xa,Ya}
Key Generation Step 2 Step 3 Parameters : Xb, Ya, q Parameters : Xa, Yb, q Step 1 Secret Key generated: Secret Key generated: K = (Ya)Xb mod q K = (Yb)Xa mod q
Key Generation Step 2 Step 3 Parameters : Xa, Yb, q Parameters : Xb, Ya, q Step 1 Secret Key generated: Secret Key generated: = (Yb)Xa mod q (Ya)Xb mod q
Choose q and α a. Choose a prime number q = 17 b. Select αas a primitive root of q, where α = 3 To be a primitive root, 3 mod 17 = 3 32 mod 17 = 9 33 mod 17 = 10 . . . . 316 mod 17 = 1 Step 1 < 17
Deriving the Key Pair Step 1 Assume private key = Xa where Xa = 15 Assume private key = Xb where Xb = 13 Step 2 Public key (Ya) becomes: Public key (Yb) becomes: Yb = 313 mod 17 = 12 Ya = 315 mod 17 = 6 Key pair : {13,12} Key pair : {15,6}
Key Generation Step 2 Step 3 Parameters : Xa, Yb, q Parameters : Xb, Ya, q Step 1 Secret Key generated: Secret Key generated: K = 1215 mod 17= 10 K = 613 mod 17= 10
Applications of DHKE Public Key Infrastructure
Applications of DHKE SSL/TLS Handshake
Applications of DHKE Secure Shell Access (SSH)