Exploring the Packet Delivery Process
Exploring the Packet Delivery Process. Chapter 1 - 6. Exploring the Packet Delivery Process. The previous sections discussed the elements that govern host-to-host communications. You also need to understand how these elements interact.

Exploring the Packet Delivery Process
E N D
Presentation Transcript
Exploring the Packet Delivery Process Chapter 1 - 6
Exploring the Packet Delivery Process • The previous sections discussed the elements that govern host-to-host communications. • You also need to understand how these elements interact. • This section covers host-to-host communications by providing a graphic representation.
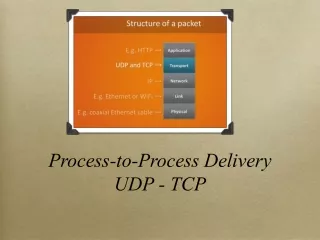
Layer 1 Devices and Their Functions • Layer 1 defines the electrical, mechanical, procedural, and functional specifications for activating, maintaining, and deactivating the physical link between end systems. • Some common examples are Ethernet segments and serial links like Frame Relay and T1. • Repeaters that provide signal amplification are also considered Layer 1 devices.
Layer 2 Devices and Their Functions • Layer 2 defines how data is formatted for transmission and how access to the physical media is controlled. • These devices also provide an interface between the Layer 2 device and the physical media. • Some common examples are a NIC installed in a host, bridge, or switch.
Host communications require a Layer 2 address. Figure 1-58 shows an example of a MAC address for a Layer 2 Ethernet frame.
When the host-to-host communications were first developed, several network layer protocols were called network operating systems (NOS). • Early NOS were NetWare, IP, ISO, and Banyan-Vines. It became apparent that a need for a Layer 2 address that was independent of the NOS existed, so the MAC address was created. • MAC addresses are assigned to end devices such as hosts. • In most cases, Layer 2 network devices such as bridges and switches are not assigned a MAC address. However, in some special cases, switches might be assigned an address.
Layer 3 Devices and Their Functions • The network layer provides connectivity and path selection between two host systems that might be located on geographically separated networks. • In the case of a host, this is the path between the data link layer and the upper layers of the NOS. • In the case of a router, it is the actual path across the network.
Layer 3 Addressing • Each NOS has its own Layer 3 address format. • the OSI reference model uses a network service access point (NSAP), while TCP/IP uses an IP address.
Mapping Layer 2 Addressing to Layer 3 Addressing • For IP communication on Ethernet-connected networks to take place, the logical (IP) address needs to be bound to the physical (MAC) address of its destination. • This process is carried out by the Address Resolution Protocol (ARP).
To send data to a destination, a host on an Ethernet network must know the physical (MAC) address of the destination. • ARP provides the essential service of mapping IP addresses to physical addresses on a network. • The term address resolution refers to the process of binding a network layer IP address of a remote device to its locally reachable, data link layer MAC address. • The address is "resolved" when ARP broadcasts the known information • The broadcast is received by all devices on the Ethernet segment. • When the target recognizes itself by reading the contents of the ARP request packet, it responds with the required MAC address in its ARP reply. • The address resolution procedure is completed when the originator receives the reply packet (containing the required MAC address) from the target and updates the table containing all of the current bindings. • (This table is usually called the ARP cache or ARP table.) • The ARP table maintains a correlation between each IP address and its corresponding MAC address.
The bindings in the table are kept current by a process of aging out unused entries after a period of inactivity. • The default time for this aging is usually 300 seconds (5 minutes), ensuring that the table does not contain information for systems that might be switched off or that have been moved.
ARP Table The ARP table, or ARP cache, keeps a record of recent bindings of IP addresses to MAC addresses • Each IP device on a network segment maintains an ARP table in its memory. • This table maps the IP addresses of other devices on the network with their physical (MAC) addresses. • When a host wants to transmit data to another host on the same network, it searches the ARP table to see if an entry exists. • If an entry does exist, the host uses it, but if not, ARP is used to get an entry. • The ARP table is created and maintained dynamically, adding and changing address relationships as they are used on the local host. • The entries in an ARP table usually expire after a period of time, by default 300 seconds; • when the local host wants to transmit data again, the entry in the ARP table is regenerated through the ARP process
Host-to-Host Packet Delivery • an application on the host with a Layer 3 address of 192.168.3.1 wants to send some data to the host with a Layer 3 address of 192.168.3.2. • The application wants to use a reliable connection. • The application requests this service from the transport layer. • The transport layer selects TCP to set up the session. • TCP initiates the session by passing a TCP header with the SYN bit set and the destination Layer 3 address (192.168.3.2) to the IP layer. • The IP layer encapsulates the TCP's SYN in a Layer 2 packet by prepending the local Layer 3 address and the Layer 3 address that IP received from TCP. • IP then passes the packet to Layer 2. Figure 1-64 shows this operation
Layer 2 needs to encapsulate the Layer 3 packet into a Layer 2 frame. • To do this, Layer 2 needs to map the Layer 3 destination address of the packet to its MAC address. • It does this by requesting a mapping from the ARP program. • ARP checks its table. • In this example, it is assumed that this host has not communicated with the other host, so you see no entry in the ARP table. • This results in Layer 2 holding the packet until ARP can provide a mapping. Figure 1-65 shows this operation.
The ARP program builds an ARP request and passes it to Layer 2, telling Layer 2 to send the request to a broadcast (all Fs) address. • Layer 2 encapsulates the ARP request in a Layer 2 frame using the broadcast address provided by ARP as the destination MAC address and the local MAC address as the source. Figures 1-66 and 1-67 show this operation
When host 192.168.3.2 receives the frame, it notes the broadcast address and strips the Layer 2 encapsulation. Figure 1-68 shows this operation.
Figure 1-69. Layer 2 Passes to ARP • The remaining ARP request is passed to ARP.
Using the information in the ARP request, ARP updates its table. Figure 1-70 shows this operation.
ARP builds a response and passes it to Layer 2, telling Layer 2 to send the response to MAC address 0800:0222:2222 (host 192.168.3.1). Figure 1-71 shows this operation.
Layer 2 encapsulates the ARP in a Layer 2 frame using the destination MAC address provided by ARP and the local source MAC address. Figure 1-72 shows this operation
When host 192.168.3.1 receives the frame, it notes that the destination MAC address is the same as its own address. It strips the Layer 2 encapsulation. Figure 1-73 shows this operation. • Figure 1-73. Layer 2 Recognizes MAC Address
The remaining ARP reply is passed to ARP. Figure 1-74 shows this operation. • Figure 1-74. Layer 2 Passes to ARP
ARP updates its table and passes the mapping to Layer 2. Figure 1-75 shows this operation. • Figure 1-75. ARP Updates the Table
Layer 2 can now send the pending Layer 2 packet. Figure 1-76 shows this operation. • Figure 1-76. Layer 2 Sends Packet Inside Frame to Start the Three-Way Handshake
At host 192.168.3.2, the frame is passed up the stack where encapsulation is removed. The remaining protocol data unit (PDU) is passed to TCP. Figure 1-77 shows this operation.
In response to the SYN, TCP passes a SYN ACK down the stack to be encapsulated. Figure 1-78 shows this operation. • Figure 1-78. Receiver Acknowledges Frame
The sender receives the ACK along with a SYN from the receiver that it must respond to. This is shown in Figure 1-79. • Figure 1-79. Sender Receives ACK
The sender sends the ACK to the receiver that it must respond to. This is shown in Figure 1-80. • Figure 1-80. Sender Acknowledges ACK and Completes the Three-Way Handshake
With the three-way handshake completed, TCP can inform the application that the session has been established. This is shown in Figure 1-81.
Now the application can send the data over the session, relying on TCP for error detection. Figures 1-82 through 1-84 show this operation.
Figure 1-84. Data Is Acknowledged The data exchange continues until the application stops sending data.
Function of the Default Gateway • In the host-to-host packet delivery, the host was able to use ARP to map a destination's MAC address to the destination's IP address. • this option is available only if the two hosts are on the same network. • If the two hosts are on different networks, the sending host must send the data to the default gateway, which forwards the data to the destination.
Using Common Host Tools to Determine the Path Between Two Hosts Across a Network • Ping is a computer network tool used to test whether a particular host is reachable across an IP network. • Ping works by sending Internet Control Message Protocol (ICMP) "echo request" packets ("Ping?") to the target host and listening for ICMP "echo response" replies. • Using interval timing and response rates, ping estimates the RTT (generally in milliseconds) and packet-loss rate between hosts.
ping [-t] [-a] [-n Count] [-l Size] [-f] [-i TTL] [-v TOS] [-r Count] [-s Count] [{-j HostList | -k HostList}] [-w Timeout] [TargetName] Windows arp command, which contains one or more tables that store IP addresses and their resolved Ethernet physical addresses. • A separate table exists for each Ethernet or Token Ring network adapter installed on your computer. • Used without parameters, arp displays help. • arp [-a [InetAddr] [-N IfaceAddr]] [-g [InetAddr] [-N IfaceAddr]] [-d InetAddr [IfaceAddr]] [-s InetAddr EtherAddr [IfaceAddr]]
The TRACERT (traceroute) diagnostic utility determines the route to a destination by sending ICMP echo packets to the destination. • In these packets, TRACERT uses varying IP TTL values. • Because each router along the path is required to decrement the packet's TTL by at least 1 before forwarding the packet, the TTL is effectively a hop counter. • When the TTL on a packet reaches zero (0), the router sends an ICMP "Time Exceeded" message back to the source c • TRACERT sends the first echo packet with a TTL of 1 and increments the TTL by 1 on each subsequent transmission until the destination responds or until the maximum TTL is reached. • The ICMP "Time Exceeded" messages that intermediate routers send back show the route. • some routers silently drop packets with expired TTL values, and these packets are invisible to TRACERT. .
Summary of Exploring the Packet Delivery Process • Layer 1 devices provide the connection to the physical media and its encoding. • Layer 2 devices provide an interface between the Layer 2 device and the physical media. • Layer 2 addresses are MAC addresses. • The network layer provides connectivity and path selection between two host systems. • Layer 3 addresses provide identification of a network and a host, such as an IP address. • Before a host can send data to another host, it must know the MAC address of the other device. • ARP is a protocol that maps IP addresses to MAC addresses. • TCP uses a three-way handshake to establish a session before sending data. • Most operating systems offer tools to view the device ARP table as well as tools like ping and traceroute to test IP connectivity.