Applying Security In Software Development Life Cycle Program
Integrating security into the development of an application or software is necessary to decrease its risk of susceptibility to attacks and exploits. Traditional methods of security testing were performed on a finished product. However, with the rise in the intensity and the number of attack vectors, it has become necessary for organizations to include it as a part of every phase of an SDLC.

Applying Security In Software Development Life Cycle Program
E N D
Presentation Transcript
Integrating Security Across SDLC Phases Hack2Secure Contribution In
Why Secure SDLC • Hackers are continuously looking for any vulnerability, flaw or weakness in an application that could be exploited to compromise the security of it. • Exponential increase in number of Security attacks and Vulnerabilities
Benefits Of SDLC • Decrease its risk of susceptibility to attacks and exploits • Reduce overall Security Control Implementation cost, Handle Active and Passive Losses etc
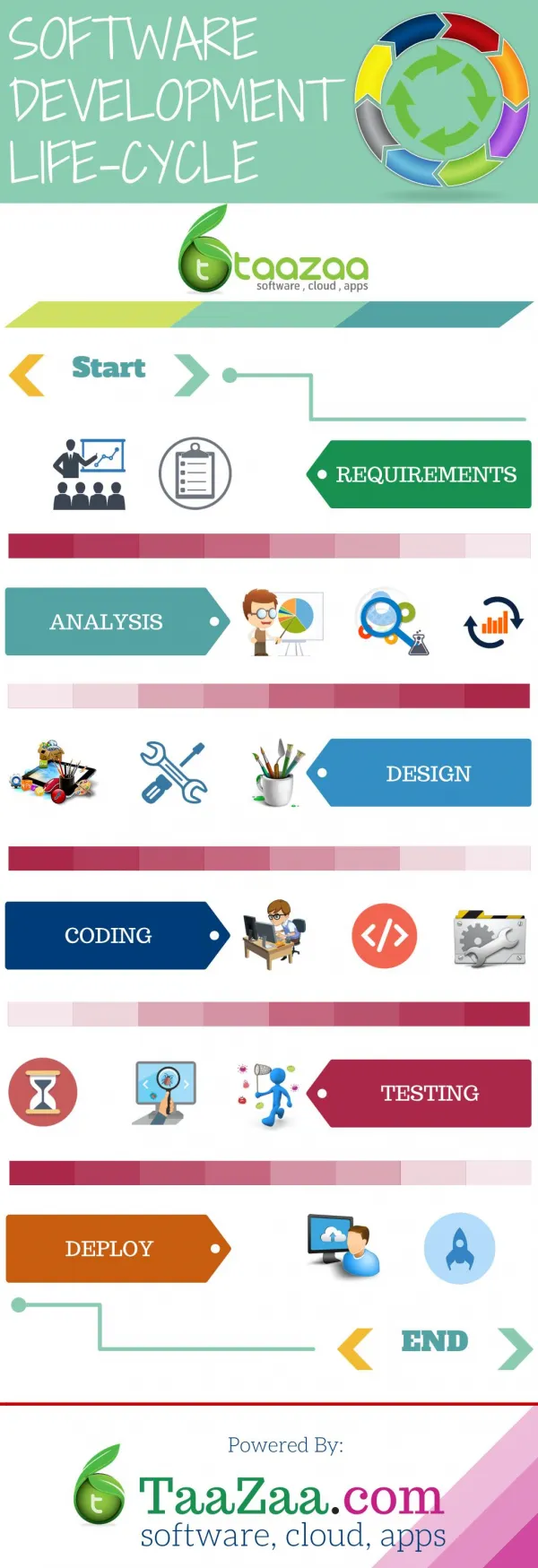
Software Development Lifecycle • Process which defines the various steps involved in the development of a software. • Adopted as a standard procedure by organizations to meet the industry requirements and deliver high-quality and secure software. • Various models of SDLC are Agile, Waterfall, V-Shaped, Iterative and more,
Secure SDLC Include security as a part of every phase of an SDLC
1. Security Training & Awareness: Educate workforce about Security Concepts, possible threats and attack scenarios so that they will be able to define and evaluate security Risk and Definitions. Training and Awareness programs needs to be organized to learn about Security Assurance and methodologies, Security Policy, Procedure and Best practices.
2. Building Security Requirements: Establishing correct security requirements is often a hard learned lesson but is very important for software development in order to avoid any confusions later. Includes preparing Security checklist, integrating Security in Quality Gates, preparing Product Security Baselines along alignment with Security Models and Standards.
3. Secure by Design: Using the prepared Requirement document, product architectures are designed. Processes like, Threat modeling will help you to analyze Attack surfaces and possible threat scenarios in existing product design.
4. Secure Implementation & Coding: Ensuring Security in Code review process and analysing standard checkpoints generally occurred at this stage to ensure it has the features and functions securely specified.
5. Security Verification/Testing: In testing stage, the developed product is evaluated to handle possible security attacks and vulnerabilities or Security defects. Different security testing tools, techniques and methodologies are required to verify Security of the product.
6. Security Review & Response Plan: Security engineers may have to build Final Security Review Plan. This plan includes tasks like Auditing, VA-PT, and Incident Handling. Organizations should have dedicated skilled staff who should be responsible for Deployment and Procurement Risk.
7. Security Maintenance: Organizations should have a maintenance plan ready to provide customer’s after service help. Security maintenance includes handling 3rd Party Vulnerabilities, Security Escalation & Patch Management Plan and Application Disposal: Policies, Criteria & Process.
Hack2Secure SWADLP Certification Secure SDLC Services Security Training Evaluate individual's implementation level skills in Security practices to ensure Secure Application Development Unique Secure SDLC program & Security services across it Information Security Training Secure Software Development
Hack2Secure provides the overall solutions to organizations that will be helpful for you to develop a secure, flawless and threat free Application, and make your product differentiated from others. • It will help to pay attention to every single detail and perform in a structured manner so as to minimize threats or entry points for an attacker.