How Hackers Use Fake Printers for Remote Command Execution on Linux
0 likes | 9 Views
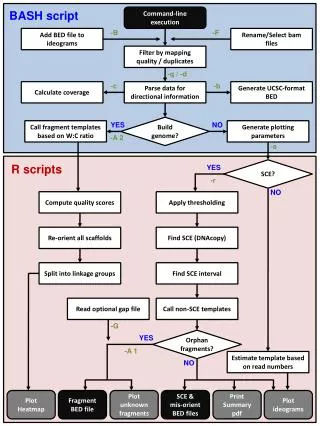
Remote Command Execution (RCE) is one of the most critical and dangerous types of vulnerabilities in cybersecurity. In simple terms, it allows an attacker to remotely execute malicious commands on another machine, often leading to data breaches, unauthorized access, and complete system control.<br>Contact us: 91 9900 53 7711<br>Please write to us: info@bornsec.com<br>Visit us: https://bornsec.com/<br>https://bornsec.com/how-hackers-use-fake-printers-for-rce-on-linux/<br>
Download Presentation 

How Hackers Use Fake Printers for Remote Command Execution on Linux
An Image/Link below is provided (as is) to download presentation
Download Policy: Content on the Website is provided to you AS IS for your information and personal use and may not be sold / licensed / shared on other websites without getting consent from its author.
Content is provided to you AS IS for your information and personal use only.
Download presentation by click this link.
While downloading, if for some reason you are not able to download a presentation, the publisher may have deleted the file from their server.
During download, if you can't get a presentation, the file might be deleted by the publisher.
E N D
Presentation Transcript
More Related